Meta description: Compare the best pentest AI tools for MSPs, vCISOs, and resellers. Learn when automated penetration testing helps, when manual pentesting is required for SOC 2, HIPAA, PCI DSS, and how to scale white label pentesting profitably.
Ignoring AI in pentesting is a service delivery mistake. Your clients expect faster testing cycles, clearer validation, and proof that security work leads to risk reduction, not another pile of scanner output.
AI pentest tools already handle a lot of the repetitive work well. They scan, correlate findings, retest changes, and highlight likely attack paths faster than a human team can do by hand. That makes them useful for MSPs trying to serve more clients without adding headcount every time a new account signs.
They do not replace a skilled tester. Manual work still decides whether an engagement reflects real business risk, whether the scope matches compliance needs, and whether the final report will hold up with an auditor, insurer, or security-conscious buyer.
That distinction matters for MSP economics.
Use AI to make your service faster and more repeatable. Use manual, white-labeled pentesting when the client needs evidence that stands up to review for SOC 2, HIPAA, PCI DSS, or ISO 27001, or when the central question is how an attacker would chain small weaknesses into a meaningful compromise. If you want a practical model for combining both, this guide to AI pentesting for MSPs lays out the service approach clearly.
That is the lens for this list. The best AI pentest tools help MSPs validate exposure, prioritize effort, and scale recurring security services. The best manual pentests still deliver the context, judgment, and client-ready reporting that automation cannot. For broader background, this overview of AI penetration testing is a useful reference.
Horizon3.ai NodeZero for autonomous pentest
NodeZero proves a simple point fast. Autonomous pentesting is useful when it shows what an attacker can do, not when it dumps another long list of findings into your queue.
That makes it a strong fit for MSPs running repeatable security services across many client environments. If you need regular internal and external validation, NodeZero helps you test at scale, show progress over time, and give clients evidence tied to exploitable paths instead of noise.
Where NodeZero earns its place
The platform is strongest in infrastructure-heavy environments where the question is straightforward. Can an attacker get in, move laterally, abuse credentials, or escalate privileges?
What stands out
- Exploit-backed results: It prioritizes demonstrated attack paths over raw vulnerability counts.
- Strong internal testing value: Active Directory, credential exposure, and internal network risk are where tools like this save MSP teams real time.
- Useful reporting: Findings are easier to discuss with clients because they connect to impact, not just severity labels.
If you are comparing platforms in this category, this guide to automated penetration testing software for MSPs gives useful context on where autonomous tools fit.
Use NodeZero for efficient, recurring validation. Use a manual, white-labeled penetration test when the client needs an auditor-ready deliverable for SOC 2, HIPAA, or PCI DSS, or when significant risk lives in a web app, API, payment workflow, or business logic.
Where it stops
NodeZero is not your answer for every engagement.
It will not replace a skilled tester reviewing custom applications, authorization flaws, tenant isolation, chained logic issues, or the messy edge cases that matter in a real breach. Those are the cases that trigger failed audits, customer escalations, and expensive cleanups for MSPs that oversell automation.
That is the line MSPs need to hold. AI tools like NodeZero make your service faster and more consistent. Manual pentesting still carries the work when the client needs deeper application testing, white-labeled reporting, and evidence that stands up to a compliance review.
A lot of MSPs use that split well. They run autonomous testing to keep exposure visible between larger engagements, then bring in manual testers for the scopes where context and human judgment decide the outcome. This article on AI pentesting for MSPs explains that service model clearly.
Direct website: Horizon3.ai NodeZero
Pentera for continuous security validation
Pentera fits MSPs that need proof their clients’ controls still hold up after constant change. New cloud workloads, policy drift, admin sprawl, and AD changes can turn last quarter’s “secure enough” into this quarter’s incident.
That makes Pentera useful as an ongoing validation layer, especially for MSPs building recurring security services instead of selling one annual pentest and disappearing. It emulates attacker behavior across internal environments, cloud, and identity infrastructure, then shows what is exploitable instead of dumping another long list of theoretical findings.
Why Pentera makes sense for MSPs
Pentera is a practical choice when your service model depends on repeatability. You can run regular validation, show clients whether controls are working, and track whether remediation changed the result. That is much easier to sell and retain than raw vulnerability scanning.
It also gives MSPs a cleaner story for security reviews. Instead of saying, “we found 400 issues,” you can show which paths matter, which controls failed, and what needs fixing first. This breakdown of automated penetration testing software for MSPs is useful if you are comparing validation platforms against traditional scanners.
Best fit for
- Recurring security services: Regular testing across client environments without rebuilding the process every time
- Control validation: Verifying segmentation, identity controls, and detection layers against realistic attack paths
- Client reporting: Clearer prioritization for leadership teams that do not want scanner noise
Where MSPs get this wrong
Some MSPs oversell platforms like Pentera as a replacement for a penetration test. That is a mistake.
Pentera improves efficiency and gives you consistent validation between larger engagements. It does not replace a manual tester reviewing custom applications, broken access control, payment flows, tenant isolation, API abuse, or business logic. Those are the issues that create real exposure and trigger hard questions during audits.
That matters even more for clients working toward SOC 2, HIPAA, or PCI DSS. Continuous validation helps prove control health. It does not give the client everything they need when the requirement is a deeper, scoped assessment with human judgment, white-labeled reporting, and findings that stand up in a compliance review.
Use Pentera to keep exposure visible and to make recurring services more efficient. Bring in a manual, white-labeled penetration test when the client needs audit-ready evidence or when the risk lives in the application layer.
Direct website: Pentera
Hadrian for external attack surface focus
Hadrian matters when your client’s biggest security problem is simple to describe and painful to manage. They do not know everything they have exposed to the internet.
That happens all the time with fast-growing SaaS companies, multi-cloud environments, acquired domains, and old DNS records nobody wants to touch. MSPs inherit that mess during onboarding, then get blamed for exposure that existed long before the contract started. Hadrian helps you find public-facing assets fast and sort real attack paths from background noise.
Best use case for Hadrian
Use Hadrian when you need a clear view of external attack surface risk across changing client environments. It is a strong fit for discovery, exposure validation, and prioritizing what deserves attention first.
Where it fits
- External asset discovery: Useful when the client inventory is incomplete or wrong
- Internet-facing validation: Better for proving which exposed systems increase risk
- Scoping support: Helpful before a larger engagement, especially when public exposure keeps shifting
Nova also gives MSPs a way to package targeted external testing without forcing every client into a full platform rollout.
What MSPs should not expect from it
Hadrian improves speed and visibility. It does not replace a skilled tester reviewing how an attacker would abuse a custom app, chain weak permissions in cloud infrastructure, or move through sensitive business workflows.
That distinction matters for both security and service delivery. If a client needs help cleaning up shadow IT, unknown subdomains, exposed services, or stale internet-facing assets, Hadrian is a smart tool. If the client needs evidence for SOC 2, HIPAA, or PCI DSS, or they need findings that stand up to auditor scrutiny, add a manual, white-labeled penetration test.
That is the right split. Use AI-driven platforms to reduce blind spots and speed up recurring external checks. Use human-led pentesting where judgment, context, and client-ready reporting determine the outcome.
Direct website: Hadrian
Ridge Security for MSP repeatability

Ridge Security fits MSPs that need testing they can run again and again without building a custom process for every client. That matters more than flashy AI claims. If your margins depend on repeatable delivery across many SMB accounts, RidgeBot and PurpleRidge deserve a serious look.
The appeal is straightforward. Ridge gives MSPs a way to run recurring exploit validation across infrastructure, web apps, and mixed client environments without dragging every engagement into a labor-heavy manual project.
Why Ridge Security is MSP-friendly
Ridge Security is built for operational consistency. That is a significant value for MSPs.
What MSPs should notice
- Multi-environment testing: Useful when clients have a mix of network, application, and hybrid assets
- SaaS deployment model: Faster to roll out across tenants than piecing together your own stack
- Flexible consumption: Easier to package into recurring service tiers or smaller-scope checks
That makes Ridge a practical option for baseline validation, recurring retests, and service packages aimed at cost-sensitive clients.
Where the limits show up
Automation helps with coverage and cadence. It does not replace human judgment.
Ridge can validate known paths and common weaknesses at scale, but MSPs still need an experienced tester for business logic abuse, role and permission edge cases, chained findings, and anything tied to how a client operates. Those are the issues that create real exposure, and they are often the issues auditors and security leaders care about most.
Use Ridge Security to improve efficiency and keep recurring testing from becoming a delivery burden. Add a manual, white-labeled penetration test when the client needs defensible evidence for SOC 2, HIPAA, or PCI DSS, or when the scope includes custom apps, sensitive workflows, or a high-stakes release.
That split is the smart one. AI-assisted tools help MSPs scale. Manual pentesting is still the right answer when the work needs context, credible reporting, and findings that hold up under review.
Direct website: Ridge Security
SafeBreach for BAS style validation
SafeBreach fits best when your client needs proof that security controls still detect, block, and contain common attacker behavior. That is a useful service. It is not the same service as a penetration test.
For MSPs, that distinction matters because clients often buy both for different reasons. SafeBreach helps you run repeatable breach and attack simulations across environments, measure control performance over time, and turn that into a recurring validation program. If you offer managed detection support, purple team exercises, or regular control reviews, that is a practical use case.
Where SafeBreach earns its place
SafeBreach is strong at answering operational questions. Are endpoint controls firing? Is email protection catching payloads? Did a policy change create a detection gap? BAS platforms are built for that kind of validation.
Good fits for SafeBreach
- Control validation: Useful for checking whether defensive tools still work after changes
- Recurring assurance: Easier to run on a schedule than a manual test
- Security operations support: Helpful for tuning detections and validating response workflows
That makes SafeBreach a good complement to your service stack, especially for clients that want ongoing evidence instead of a once-a-year snapshot.
Where MSPs need to draw the line
SafeBreach will not give you the depth of a manual pentest. It will not dig into business logic flaws, abuse custom workflows, test odd privilege boundaries, or explore the kind of chained issues that create serious exposure in real environments.
MSPs should use BAS to improve speed and coverage. Then bring in a human-led, white-labeled penetration test when the client needs credible evidence for SOC 2, HIPPA, or PCI DSS, or when the scope includes custom applications, sensitive data handling, or high-risk changes.
That is the right split. AI-driven simulation helps you deliver continuous validation efficiently. Manual pentesting is still the work product that holds up when a client needs context, judgment, and reporting that can survive compliance review.
Direct website: SafeBreach
Cymulate for modular exposure testing
Cymulate makes sense for MSPs that need flexible service packaging, not one fixed testing model. You can run focused email validation for one client, endpoint and lateral movement scenarios for another, and broader exposure exercises for a larger account without forcing all of them into the same scope.
That matters when margins are tight and client maturity is all over the map.
Why MSPs can sell this cleanly
Cymulate’s modular structure fits the way managed services are sold. You can attach recurring validation to existing security bundles, keep smaller clients on a narrower scope, and expand testing as the environment or contract grows.
Where it fits well
- Tiered service offers: Easier to match scope to budget
- Multi-client operations: Better for standardizing repeatable checks across accounts
- Client reporting: More usable for recurring reviews than raw security tool output
It also works well between formal assessments. If you already offer continuous penetration testing for managed clients, Cymulate helps cover the validation work that clients expect on a monthly or quarterly cadence.
Where MSPs should draw the line
Modular exposure testing still depends on scenario quality and operator judgment. If the simulations are weak or poorly tuned, the client gets activity logs and dashboards, not a meaningful explanation of risk.
Use Cymulate to improve speed, coverage, and service consistency. Do not position it as a replacement for a manual, white-labeled penetration test when the client needs evidence that will hold up under SOC 2, HIPAA, or PCI DSS review, or when the scope includes custom applications, sensitive workflows, or high-impact privilege paths.
That is the right split for MSPs. AI-driven tools like Cymulate help you run efficient, repeatable exposure testing. Manual pentesting is still the work that finds chained weaknesses, tests business logic, and gives your client a report they can hand to an auditor without apology.
Direct website: Cymulate
XM Cyber for attack path management
XM Cyber earns its place on this list because MSPs do not need more alerts. They need to know which chain of weaknesses gets an attacker from initial access to the systems that matter.
That is XM Cyber’s value. It maps attack paths across identities, misconfigurations, privileges, and exposures so your team can fix the few issues that create real blast radius instead of drowning in low-priority findings.
For MSPs managing hybrid estates, this matters fast. Cloud permissions, legacy AD, flat vulnerability scans, and disconnected tickets do not tell a client how an attack unfolds. XM Cyber does. It gives you a clearer remediation order and a better story for quarterly reviews.
Where XM Cyber fits
XM Cyber is a strong fit between formal assessments. If your service stack already includes continuous penetration testing for managed clients, attack path mapping adds day-to-day prioritization that those engagements are not built to provide on their own.
Best use cases
- Hybrid environments: Useful when on-prem, cloud, and identity paths overlap
- Privilege escalation exposure: Better than basic scan output for showing how access expands
- Remediation triage: Helps technical teams fix the path, not just the symptom
- Security reviews: Gives account managers and vCISOs something more useful than a raw findings export
AI-backed analysis helps here. It improves speed and prioritization.
It does not replace a manual, white-labeled penetration test when the client needs proof for SOC 2, HIPAA, or PCI DSS, or when you need a human tester to validate exploitability, abuse business logic, or document real-world impact in a report an auditor will accept.
That is the line MSPs should hold. Use XM Cyber to keep exposure visible and remediation focused. Use manual pentesting to verify risk, satisfy compliance expectations, and deliver the kind of client-ready evidence automated platforms do not produce.
Direct website: XM Cyber
ForAllSecure Mayhem for code and API fuzzing

Mayhem matters because pentest ai tools are not all built for the same job. MSPs that support software companies, product teams, or DevSecOps programs need coverage before release, not just after deployment.
That is Mayhem’s lane.
It focuses on AI-assisted fuzzing for binaries, applications, and APIs. For MSPs with clients shipping code regularly, that makes it far more useful in pre-production than another platform chasing exposed hosts and credentials. It helps teams find crash conditions, unsafe input handling, and API behavior that standard scanners often miss.
Where Mayhem fits
Mayhem is a strong fit if your service offering touches the software lifecycle at all. It works well for partners supporting secure SDLC reviews, release gating, and engineering teams that need repeatable testing inside CI/CD.
Best use cases
- API-heavy products: Finds edge-case input and behavior issues that break normal test coverage
- Application security programs: Supports teams that need more than SAST and dependency scanning
- Pre-release testing: Helps catch defects before production exposure and client impact
- Engineering-focused accounts: Better fit for software vendors and SaaS providers than infrastructure-only clients
MSPs should position this correctly. Mayhem improves efficiency in app and API testing, and it can support teams already using large language models (LLMs) across security workflows. It does not replace a manual, white-labeled penetration test when a client needs auditor-ready evidence, exploit validation, or a formal assessment for SOC 2, HIPAA, or PCI DSS.
That distinction matters. Fuzzing can expose defects early and reduce avoidable risk. A human tester still has to verify real-world impact, test business logic, and produce the report your client can hand to an auditor or procurement team.
Direct website: ForAllSecure Mayhem
PentestGPT for assisted operator workflows
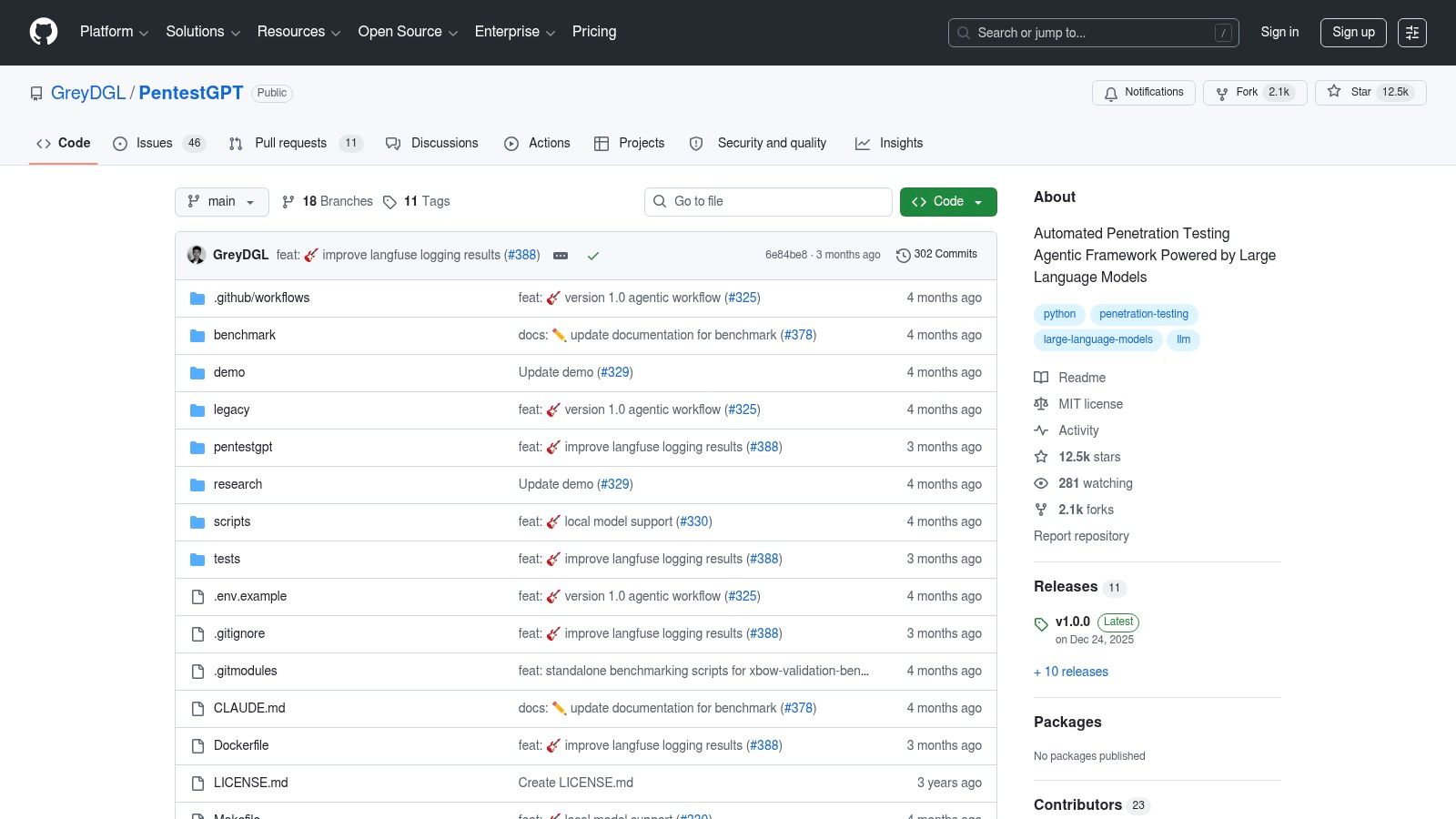
PentestGPT gets overrated by teams that want faster pentesting without paying for senior talent. That is the wrong use case.
For MSPs, PentestGPT works best as an assistant for experienced operators. It can speed up recon planning, organize findings, help draft test steps, and clean up documentation during an engagement. That saves time. It does not produce the judgment, exploit validation, or client-safe reporting that makes a pentest worth selling.
Who should use it
Use PentestGPT if you already have testers who know what good looks like. Skip it if your plan is to turn junior analysts into client-facing pentesters with a prompt window.
Where it helps
- Internal R&D: Low-cost option for testing workflows in a lab
- Operator support: Useful for note organization, test sequencing, and summarizing outputs
- Flexible deployment: Can run with local or hosted models, depending on your security requirements
PentestGPT belongs in the same broader category as tools built on large language models (LLMs). The value is speed and structure for the human operator. The human still does the hard part.
Where MSPs get this wrong
Open-source AI pentest tools look cheap on paper. In practice, your team pays in setup time, prompt tuning, review effort, and rework. If the operator lacks real offensive experience, the output can be sloppy, unsafe, or flat-out wrong.
That matters for service delivery. Clients buying a white-labeled pentest do not want a transcript of AI suggestions. They want a clear scope, tested findings, evidence that holds up under review, and a report they can use for procurement, insurance, or audit conversations.
Use PentestGPT to improve internal workflow efficiency. Do not position it as your pentesting methodology. For SOC 2, HIPAA, PCI DSS, and any engagement where credibility matters, manual testing and human verification are still required.
Direct website: PentestGPT on GitHub
DeepExploit for research and labs
DeepExploit is a lab tool, not an MSP service platform. That distinction matters.
It is useful because it shows how AI-assisted exploitation can be tested in controlled environments with Metasploit and reinforcement learning. If you run an internal lab, train junior staff, or want hands-on exposure to automated exploit selection, it has value. If you need consistent client delivery, clean evidence, and reports that stand up to compliance review, look elsewhere.
When DeepExploit is useful
DeepExploit fits research and training far better than production work. Use it to study attacker logic, test automation ideas, and show analysts how exploit chains can be assembled inside a safe environment.
Good use cases
- Research: Examine how AI-driven exploitation workflows behave
- Training labs: Show analysts how automated exploit chaining works
- Controlled testing: Experiment in isolated environments without client risk
Where MSPs should draw the line
Do not build a white-labeled pentest service around DeepExploit. The project is better suited to experimentation than repeatable, supportable assessments for paying clients.
That is the essential line MSPs need to hold. AI tools can speed up research, improve internal testing, and help your team prepare for engagements. They do not replace manual validation, scoped testing, and reviewer-ready reporting. For SOC 2, HIPAA, PCI DSS, and similar requirements, a human-led penetration test is still the standard if you want credible findings and audit-ready evidence.
Use DeepExploit to sharpen your team in the lab. Sell manual pentesting when the client needs trust, compliance coverage, and real risk reduction.
Direct website: DeepExploit on GitHub
Top 10 AI Pentest Tools: Feature Comparison
| Product | Core focus | Key features | Strengths / Quality | Best for | Pricing / Licensing |
|---|---|---|---|---|---|
| Horizon3.ai - NodeZero | Autonomous internal & external pentesting | AD credential audits, cloud attack-path discovery, MITRE-mapped evidence, continuous/on-demand runs | Evidence-backed findings; auditor-friendly; consistent depth vs scanners | MSPs needing repeatable, scalable validation for clients | Annual license; cost scales with asset count; marketplace pricing signals |
| Pentera | Automated Security Validation (ASV) | Continuous attacker emulation, risk-prioritized attack paths, AD/cloud coverage, ransomware modules | Broad coverage; analyst-recognized; enterprise-grade validation | MSPs offering CTEM-style managed validation | Quote-based enterprise pricing |
| Hadrian (Nova) | External exposure management + agentic pentesting | Continuous internet-facing asset discovery, AI attack agents, CART-style red teaming, hourly scans | Low noise; fast SaaS onboarding; per-test option available | MSPs focused on perimeter/external assessments and project work | Per-test (Nova) & scope-based pricing; limited transparency |
| Ridge Security (RidgeBot / PurpleRidge) | Autonomous pentesting with SMB/MSSP options | Automated exploit validation across infra, apps, OT/IoT; credit-based self-service | Repeatable on-demand testing; SMB-friendly credit model | MSSPs/MSPs serving many small clients or multi-tenant environments | Credit-based, self-service tiers; marketplace availability |
| SafeBreach | Breach & attack simulation (BAS) | Large attack library, continuous simulations, MITRE mapping, "Original Attacks" research | Mature BAS vendor; safe repeatable simulations for production | MSPs delivering continuous control validation and purple-team services | Enterprise quote-based pricing |
| Cymulate | Modular BAS + Automated Red Teaming | Configurable campaigns (email, web, lateral), automated red teaming, compliance reporting | Flexible modules; strong scenario coverage; easy tailoring | MSPs offering continuous validation and improvement tracking | SaaS with modular pricing; marketplace options |
| XM Cyber | Continuous attack-path & exposure management | Graph-based attack path analysis, continuous validation, prioritized remediation | Excellent exposure prioritization; keeps risk current between pentests | MSPs providing ongoing exposure management and remediation guidance | Mid-to-enterprise pricing; quote-based |
| ForAllSecure - Mayhem | AI-assisted fuzzing for code/APIs | AI-guided fuzzing for binaries & APIs, CI/CD integration, free tier for light use | Finds hard-to-reach bugs missed by scanners; developer-friendly | MSPs offering secure SDLC/DevSecOps services | Free tier + paid enterprise plans |
| PentestGPT (open source) | LLM-assisted pentest orchestration & R&D | Orchestration of tools, session persistence, LLM-driven reasoning | No license fee; extensible; accelerates reconnaissance & PoC drafting | Experienced pentesters, R&D labs, internal MSP tooling | Open-source (requires LLM keys/hosting); self-managed |
| DeepExploit (open source) | RL-based auto-exploitation research | RL agent for Metasploit exploit selection, automated scan-exploit loops | Educational and research value; can speed lab workflows | Labs, CTFs, research teams, not for production clients | Open-source; research project with variable reliability |
Making AI work for MSP security services
AI pentest tools save time. They do not carry an MSP security practice on their own.
Your clients want fast answers, lower costs, and audit-ready evidence for SOC 2, HIPAA, PCI DSS, or ISO 27001. They also expect judgment. They want someone to tell them which findings matter, what can wait, and where a real attacker would break through. Automated platforms help with coverage and frequency. Manual testing handles context, validation, and defensible reporting.
Use AI where speed and repetition drive margin
Use automation for recurring work that would otherwise eat analyst hours. Run it for attack surface monitoring, routine internal checks, control validation, attack path review, and drift detection across cloud or identity changes.
That gives MSPs three practical wins:
- More frequent evidence: Clients see progress between annual or quarterly projects
- Better service packaging: You can sell a recurring validation layer without staffing every task manually
- Faster prioritization: Your team spends less time gathering noise and more time reviewing what deserves escalation
This is the right use of AI. It improves efficiency. It does not replace offensive security judgment.
Use manual pentesting where the outcome has to hold up
Compliance buyers often blur the line between automated testing and a true penetration test. You should not.
A compliance-ready pen test needs defined scope, test methodology, evidence, validation, attack chaining, and clear explanation. It also needs a tester who can spot business logic abuse, weak trust boundaries, broken authorization, risky cloud configurations, and workflow flaws that automated platforms routinely miss. When an auditor, insurer, or client legal team asks follow-up questions, a report generated by tooling alone is rarely enough.
For MSPs, the rule is simple. Use AI to find more. Use human testers to prove impact and deliver results that stand up under review.
If the client wants defensible findings for compliance and risk reduction, manual pentesting is the requirement.
Build the service around both
The strongest offer is a hybrid one.
Start with automated validation to keep visibility high and reporting cadence steady. Then scope manual pentesting around the areas where failure would be expensive or embarrassing: custom web apps, mobile workflows, internal networks before an audit, privileged access paths, or a retest after major remediation. That model keeps entry pricing reasonable while giving clients a clear reason to buy deeper testing.
It also helps you sell the right thing at the right time:
- Automation covers repeatable checks and ongoing exposure tracking
- Manual testing covers attacker behavior, edge cases, and audit scrutiny
- White label delivery keeps your brand in front of the client
That distinction matters for MSP margins. It also matters for client trust.
Where MSP Pentesting fits
If you need a partner for the manual side, keep the filter tight. Choose a team that works channel-only, stays out of your client relationships, delivers white label pentesting, and can explain the methodology behind the report.
MSP Pentesting fits that model. The company provides white-labeled pentests for MSPs, vCISOs, resellers, and compliance-focused firms across web apps, internal networks, mobile apps, cloud, external testing, social engineering, and physical engagements. Its team includes OSCP, CEH, and CREST certified pentesters, and reports are delivered under the partner’s brand with fast turnaround times.
That is the practical split. Use AI tools to improve coverage and efficiency. Use certified human testers when the client needs credible reporting, compliance support, and a real assessment of how an attacker would move through the environment.
If you need affordable, fast, white label pentesting that supports your brand and never competes for your clients, talk to MSP Pentesting. We help MSPs, vCISOs, GRC firms, and resellers combine automated testing with certified manual pentesting for compliance and real risk reduction.



.avif)
.png)
.png)
.png)

