When it comes to cybersecurity, an automated scan is your first line of defense. Think of it like a security guard doing a quick patrol, checking every door and window for an obvious unlocked entry point. For MSPs and vCISOs, these scans are a must for getting a quick lay of the land across a client's digital world. They are fast, affordable, and provide a great starting point.
What is an Automated Scan and Why Does It Matter?
An automated scan is a software tool that checks systems, apps, and networks against a big database of known security flaws. It's the fastest, most affordable way to get a baseline read on a company's security. For you, as an MSP or vCISO, this is the perfect entry point for any new client. You get broad coverage, fast.
These scans find the low-hanging fruit and common misconfigurations that attackers love to exploit first. This initial sweep is also key for checking the box on baseline compliance for frameworks like SOC 2, HIPAA, and PCI DSS. It helps you prove your value right away by flagging real issues without a huge upfront cost.
An automated scan is like a spell-checker for your security. It’s fantastic at catching common errors, but it doesn't know if the story you’ve written makes sense. It’s a great tool, but it's not the whole process. This is where your real value comes in. The report from an automated scan isn't the final word; it’s the conversation starter. It gives you the data to build a compelling story for your client, map out a real risk assessment, and pinpoint areas that need a human touch.
Scans are the Foundation of Your Security Services
If you're a reseller, automated scans are your gateway to selling higher-margin security services. The findings let you create a clear, actionable story for your clients about their security gaps. This instantly positions you as a strategic advisor, not just another IT vendor. From there, the conversation naturally turns to the limits of automation.
It becomes much easier to explain why they need a manual penetration test. A real pen test picks up where the scanner leaves off. A certified expert, like our pentesters with OSCP, CEH, and CREST certifications, actively tries to exploit the vulnerabilities the scan found. More importantly, they find the ones it missed. This is the core of manual pentesting.
An automated scan tells you where to look, and a manual penetration test tells you what it all means. Automated scans are also a key part of satisfying any comprehensive cybersecurity audit checklist. They provide the initial data needed to build a strategy that will hold up under review. By combining the speed of an automated scan with the intelligence of a pen test, you deliver real security.
Breaking Down the Types of Automated Scans
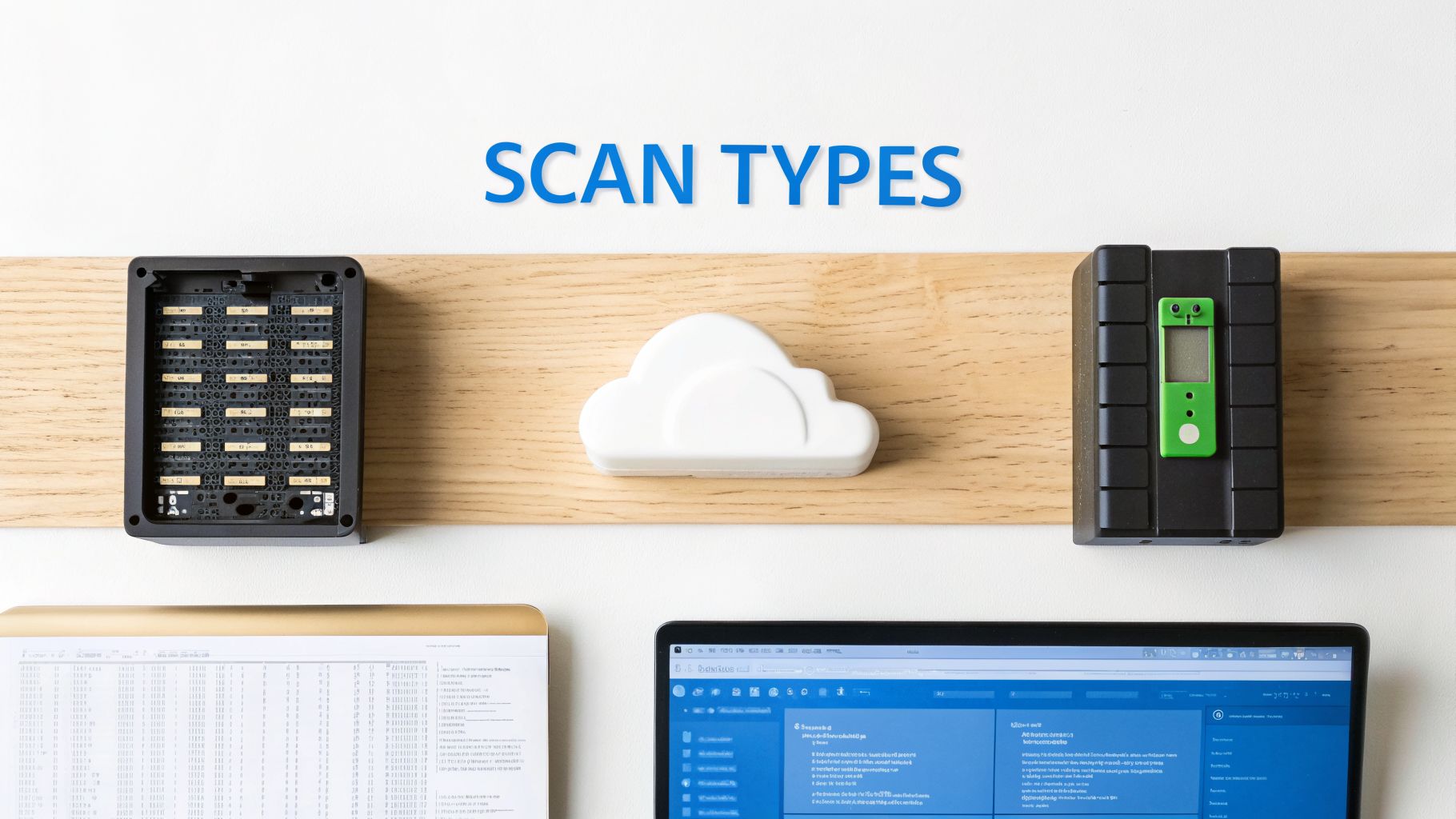
Not all automated scans are the same. Knowing the difference is what separates you from the competition and makes you a trusted security advisor. Each automated scan is a specific tool for a specific job. As an MSP or vCISO, you need to know which tool to use to protect your clients properly.
You wouldn't use a vulnerability scanner to find a business logic flaw in a web app. Using a mix of scans is the only way to get a real, actionable picture of your client's risk assessment and prove your value. These tools are the first line of defense and the most common type of automated scan. They act like a security patrol checking every digital door and window on your client's network.
Their mission is to find the low-hanging fruit before an attacker does. We're talking unpatched software, weak passwords, and basic misconfigurations. This is a must-have for most compliance frameworks and gives you a quick view of your client's basic security. For more on this, check out our guide on security vulnerability scanning.
Understanding Web, Network, and Cloud Scans
Your client’s web apps are a massive target for attackers. Web application scanners are built to find cracks in these digital storefronts. Static Application Security Testing (SAST) tools review the source code, finding bugs when they are cheapest to fix. Dynamic Application Security Testing (DAST) tools attack a live, running application from the outside, just like a hacker would.
Your client's network and cloud environments are the foundation. Network scanners map out your client’s attack surface, finding every device and open port. Cloud configuration scanners are essential. They audit AWS, Azure, and GCP for things like public S3 buckets or weak IAM policies, which is critical for meeting ISO 27001 and PCI DSS compliance. You can dig deeper into the tools in our guide on automated penetration testing software.
Beyond the big three, specialized scanners handle niche problems. For example, tools can perform automated cookie audits to ensure a client's website doesn't violate privacy laws and create a GRC nightmare. As a reseller, your job is to know which combination of tools gives your client the security they need. By starting with a broad automated scan and then upselling a targeted, manual penetration test, you deliver a complete security picture. Our white label pentesting lets you offer these high-value services under your own brand.
Knowing the Limits of Automated Scanning Tools
Automated scans are fast and cheap, but you have to be clear about what they are and what they are not. Think of an automated scanner like a spell-checker. It’s great at finding known typos but has no idea if the story makes sense. These tools create a ton of noise with "false positives" and "false negatives," where real issues are missed.
The biggest weakness of any automated scan is its lack of business context. A scanner can’t understand what an application is supposed to do. That means it will always miss the clever flaws a human attacker would spot. A scanner might check for SQL injection, but it won’t think to try manipulating a shopping cart price to buy a $1,000 item for $0.01. That’s a business logic flaw, and automated tools are blind to them.
An automated scan checks for unlocked doors. A manual penetration test checks if the locks can be picked and if the security guard can be tricked. This gap between what a scanner finds and what a real attacker can exploit is your biggest opportunity as an MSP. It’s the perfect opening to explain why a deeper, human-led penetration testing engagement is essential for real security and compliance.
Why Your Business Needs Manual Pentesting
False positives from an automated scan are a headache. A scanner might flag an old software library as a risk, but it can't know if the vulnerable part is even used. This creates busywork. All that noise can make a client lose faith in the process. Your job is to cut through it and deliver a clear risk assessment.
This is why you need a human-driven penetration testing approach for validation. Our certified experts, with credentials like OSCP and CREST, can tell you if a flagged vulnerability is a real fire or just a low battery in the smoke alarm. Automated scans almost always miss business logic flaws, chained exploits, creative thinking, and privilege escalation. This is the core of our partnership. We provide expert, manual pentesting that goes beyond a simple checklist.
As bad as false positives are, false negatives are worse. This is when an automated scan comes back clean, giving a false sense of security while a major vulnerability is lurking. Imagine a scanner misses a subtle flaw. The report looks good, your client thinks they’re secure, and a month later, they’re dealing with a data breach. This is why a manual penetration test isn’t optional for any business serious about security or compliance with standards like SOC 2, HIPAA, or ISO 27001. We provide that manual layer of assurance quickly and affordably.
How to Leverage Scan Results for Your Clients
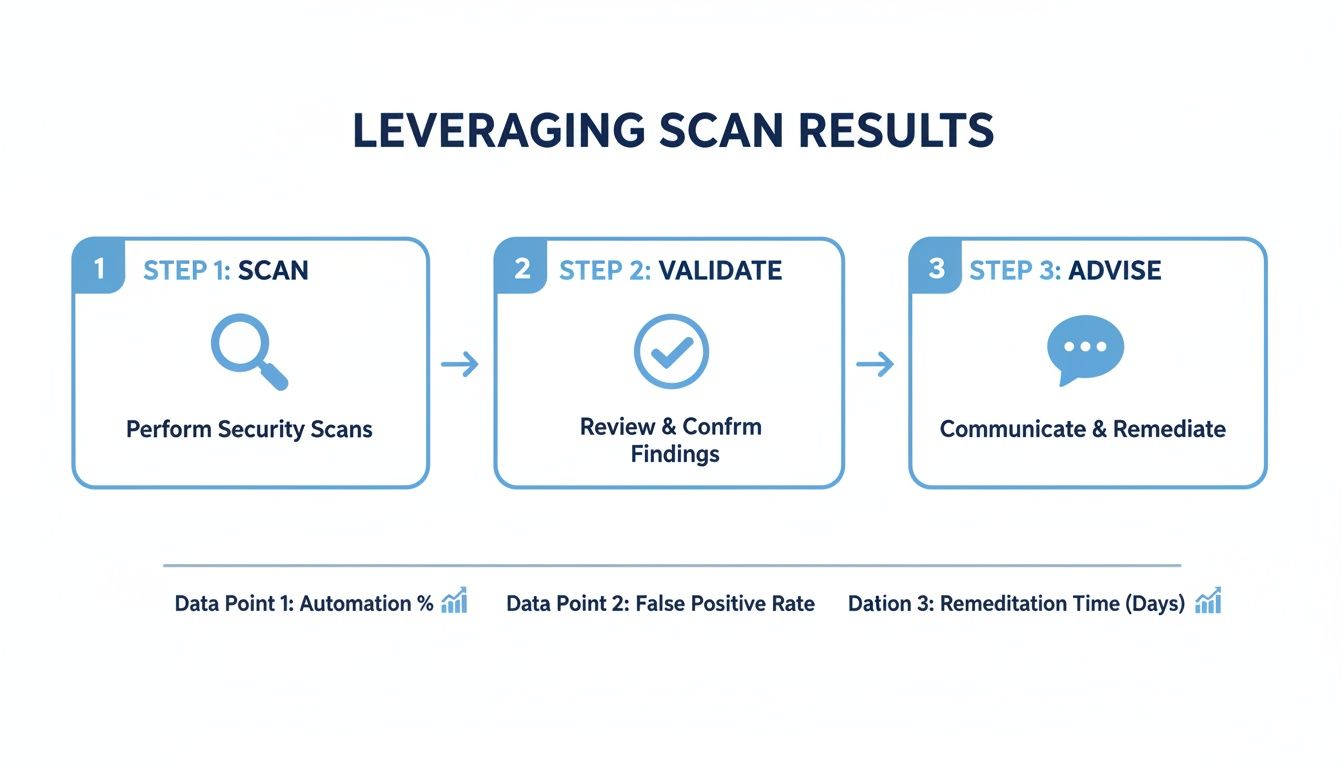
To a smart MSP or vCISO, an automated scan report is a goldmine. It's the start of a conversation and a path to more revenue. The trick isn't running the scan—it's what you do with the results. A raw scan report is just noise. Your first job is to cut through it, validate the findings, and zero in on the threats that actually put your client's business at risk.
Security isn't a one-and-done deal. You need to get your clients on a regular scanning schedule. Quarterly scanning is a great place to start. This ensures you're always on the lookout for new holes and keeps them honest for compliance frameworks like SOC 2 and HIPAA that demand continuous monitoring. This rhythm is affordable, fast, and effective.
Once you have a clean report, get on a call. Walk your client through the most critical findings and show them why it's a threat. This is your moment to highlight the limits of automation. Explain how a human attacker could chain a tiny vulnerability with others to create a massive breach. This conversation flows naturally into explaining why they need a manual penetration test. The scan data you just presented is the proof. You're no longer just selling a pen test; you're solving a problem you've proven they have.
Partner With Us for White Label Pentesting
The managed service and compliance industries have a problem: inflated prices, bad testing, and long lead times. We are the solution. We are a channel-only partner, which means we never compete with our MSP or vCISO clients. We exist to make you successful. Our entire business is designed to give you affordable, fast, and thorough manual pentesting services that you can resell.
Our white label pentesting model is simple. We do the heavy lifting in the background, and you get all the credit. You can start offering expert-led penetration tests under your own brand, opening up a revenue stream you might be missing. Stop saying no to pen test opportunities just because you don't have the team in-house. Our team becomes your team, holding certs like OSCP, CEH, and CREST.
We handle the complex penetration testing. You build a more profitable security practice. Our partnership turns you into the complete security advisor your clients are looking for, minus the overhead of hiring your own pentesters. Instead of being stuck with the limits of an automated scan, you can offer the kind of deep-dive analysis that finds critical business logic flaws. Our reports are fast, so you can get clients from discovery to remediation without the usual delays.
If you're ready to scale your security offerings, it’s time we talked. Learn more about how to grow your business by exploring our pentest partner program.
Answering Your Toughest Pentesting Questions
As an MSP or vCISO, your clients rely on you to cut through the security noise. Knowing how to explain the difference between a cheap automated scan and a real manual penetration test is everything. Use these answers to guide your conversations and show your expertise.
An automated scan is a good first step for SOC 2, but it will never be the last. Auditors know scanners miss the big stuff and will want to see a manual penetration test. A pen test shows you’ve looked for complex business logic flaws—the kind that scanners are blind to. A scan gets you on the field, but a pen test wins the game.
When clients ask about the cost difference, frame it as an investment. An automated scan is like a security guard checking for locked doors. A manual pentest is like hiring professional thieves to find every hidden way into the building. The cost of that expert-led test is small compared to the bill for a real-world breach. For a cadence, baseline security is handled with quarterly automated scans. A full manual penetration test should happen at least once a year, which is also a requirement for frameworks like PCI DSS and ISO 27001.
A vulnerability scan is an automated checklist for known problems. A penetration test is a manual attack where a certified expert tries to break your systems to find what's truly at risk. By blending the frequency of automated scanning with the expertise of a manual pen test, you give clients a complete security picture. This is the perfect opportunity to bring in our affordable, fast, white label pentesting services.
Ready to add expert, manual pentesting to your service offerings without the sticker shock? Contact us today to learn more about our partner program at https://msppentesting.com.



.avif)
.png)
.png)
.png)

