Title Tag: Application Security Engineer What MSPs Need to Know
Meta Description: Learn what an application security engineer does, why MSPs shouldn't hire one first, and how white label pentesting turns AppSec demand into affordable recurring revenue for compliance and risk assessment clients.
Your client asks a simple question.
“Can you help us secure our app?”
That question changes the whole conversation. You're not talking about help desk anymore. You're talking about SOC 2, HIPAA, PCI DSS, secure development, client risk, and whether your MSP can act like a real security partner instead of a general IT vendor.
A lot of MSPs get stuck here. They know the client needs more than antivirus, patching, and endpoint monitoring, but they also know that building an in-house AppSec function is messy, expensive, and slow. Meanwhile, another reseller, vCISO, or MSSP is already pitching pentesting, pen testing, and application reviews.
Your Client Needs Security Are You Ready
If you support clients with custom web apps, customer portals, APIs, mobile apps, or even third-party software integrations, AppSec questions are coming. They usually show up through compliance first. A CPA asks about controls for SOC 2. A healthcare client asks about HIPAA risk. A GRC partner wants evidence for a risk assessment. Then somebody asks whether the application has had a real penetration test.
That's the moment many MSPs realize they have a gap.
You can ignore it and hope the client shops elsewhere. You can try to fake it with a scanner report. Or you can treat application security engineer work as a service you resell under your brand. That last option is the one that makes money.
What clients are really asking
Clients rarely ask for an “application security engineer” by title. They ask for outcomes.
- Safer releases: They want fewer security issues reaching production.
- Audit readiness: They need proof for SOC 2, ISO 27001, PCI DSS, or internal governance reviews.
- Actionable findings: They need someone to explain what matters, what doesn't, and what to fix first.
- A partner: They want one vendor relationship, not five disconnected specialists.
Practical rule: If your client has software and compliance pressure, AppSec demand already exists. The only question is whether you'll capture it or refer it away.
The smart move is to stop thinking about this role as a hire you need on payroll. Think of it as a capability you package. That shifts the conversation from overhead to margin.
What an Application Security Engineer Does
An application security engineer puts security checks into the way software gets built and shipped. The simplest analogy is a building inspector who reviews the blueprint, checks the foundation, inspects the wiring, and flags weak points before people move in.
That matters because fixing a design flaw early is easier than cleaning up an incident after release. According to Huntress on the application security engineer role, AppSec engineers integrate security testing and secure coding practices into the SDLC, which can reduce vulnerabilities reaching production by 40–70% when applied consistently.
Here's the role at a glance.
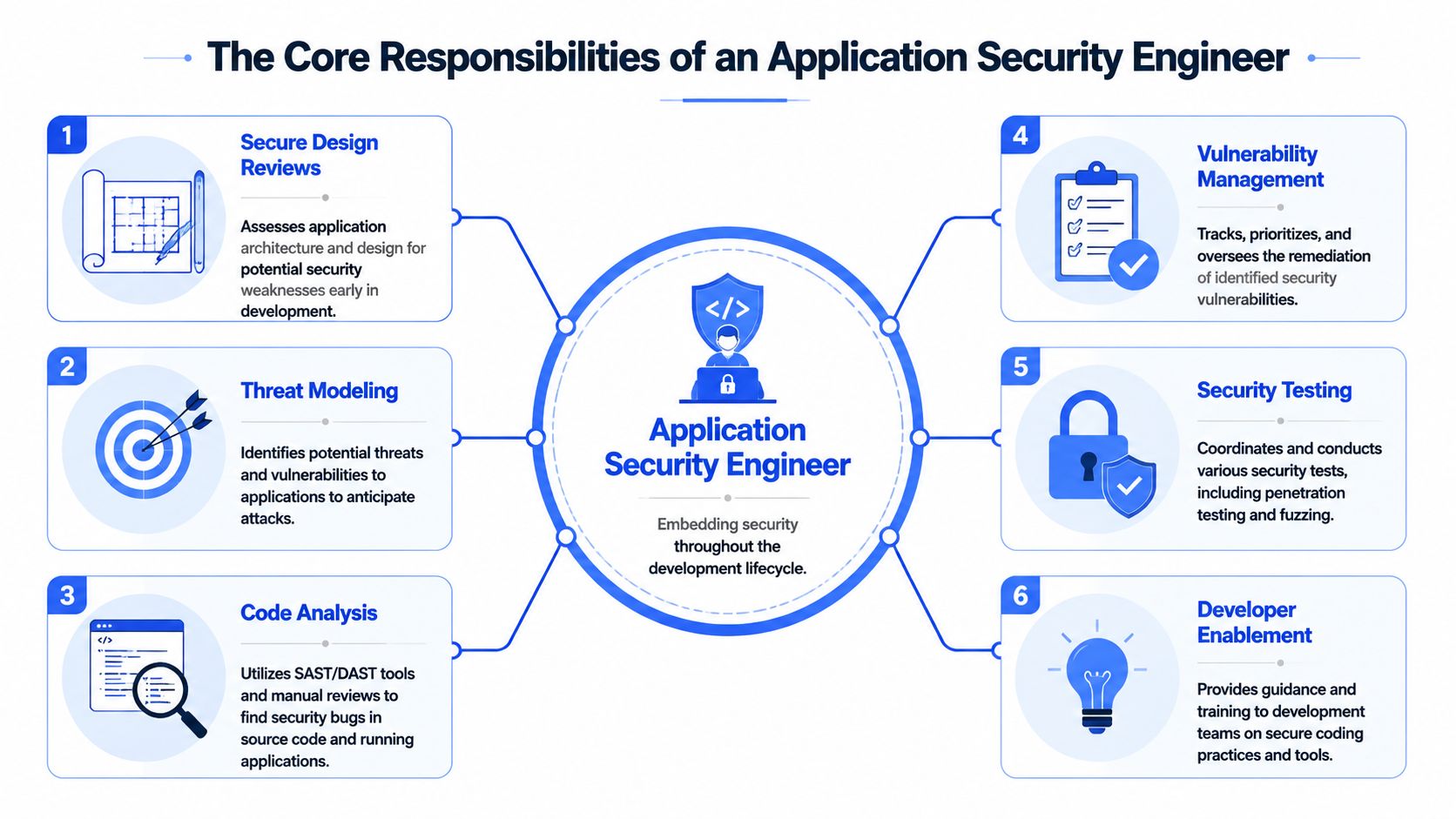
How the work shows up day to day
A real AppSec workflow usually includes a mix of engineering review and testing.
- Threat modeling: Looking at how an attacker might abuse login flows, APIs, file uploads, privilege paths, or business logic.
- Code and build analysis: Using SAST, DAST, and SCA to catch insecure code, runtime weaknesses, and vulnerable dependencies.
- Manual pentesting: Verifying whether a discovered issue is exploitable in the application.
- Remediation support: Helping developers understand the fix, not just dumping findings in a PDF.
Those tools matter because they map to the common flaws buyers already hear about, including the OWASP Top 10. If you need a plain-English refresher on those issues, this guide to common web application vulnerabilities is useful when you're explaining risk to clients.
Why MSPs should care
MSPs don't need to turn every account manager into a security engineer. They do need to understand what AppSec work solves.
An AppSec engineer helps clients answer questions like these:
| Client concern | AppSec function |
|---|---|
| “Is our app vulnerable?” | Manual penetration testing and tool-assisted analysis |
| “Will this pass review?” | Evidence for compliance and GRC discussions |
| “What do we fix first?” | Prioritization based on exploitability and business risk |
| “How do we stop repeating this?” | Secure coding guidance inside the SDLC |
Good AppSec work doesn't just find bugs. It helps the client ship software with fewer surprises.
Key Skills and Certifications Clients Trust
Clients care about credentials because credentials help them trust the report in front of them. If you're reselling AppSec services, you need testers with recognizable signals of competence. The big ones buyers understand are OSCP, CEH, and CREST.
Those certifications don't replace judgment, but they do help in sales calls, procurement reviews, and audit conversations. When a client asks who performed the pen test, “certified pentesters” is easier to sell than “we ran a tool.”

Technical skill is only half the job
A weak AppSec engineer can find flaws and still fail the client. Why? Because developers need context, not theater. Security findings have to be translated into plain language, tied to business impact, and prioritized in a way that engineering teams can act on.
That point gets missed in a lot of career content. As noted in this discussion of cloud security versus application security, “human oversight is essential for contextual analysis, prioritization, and helping developers fix issues the right way.”
If you train your own team to talk about pentests, this article on penetration testing training helps frame the difference between noise and meaningful findings.
What good AppSec communication looks like
Here's what separates a useful tester from a report generator:
- They can brief executives: They explain risk in business terms, not scanner jargon.
- They can work with developers: They know how to discuss fixes under deadline pressure.
- They can defend the finding: They can show how an issue was validated during manual pentesting.
- They avoid drama: They focus on remediation and proof, not fear-based language.
“Human oversight is essential for contextual analysis, prioritization, and helping developers fix issues the right way.”
That's exactly why reselling a credible white label pentesting service works better than handing your client an automated export and hoping for the best.
Hiring an Engineer vs Outsourcing Pentesting
A client asks for an application pentest before a product launch. You can either scramble to hire rare AppSec talent, or you can sell the engagement now and deliver it under your own brand. MSPs that want margin and speed should choose the second option.
Hiring an application security engineer makes sense only if you already have consistent demand for secure code review, threat modeling, remediation guidance, and repeated testing across multiple client environments. Most MSPs do not. They have periodic pentest demand, uneven project flow, and no reason to carry a six-figure specialist as fixed overhead.

Hiring creates a capacity problem
The issue is not just salary. It is utilization, coverage, and delivery risk.
| Build in house | Outsource white label pentesting |
|---|---|
| Recruiting delays slow down sales | On-demand delivery supports faster close cycles |
| Fixed payroll hits margin every month | Costs map to billable engagements |
| One hire limits testing depth and scope | Access to broader specialist coverage |
| Bench time turns into overhead | Demand scales up or down by client need |
One engineer also does not give you a full AppSec function. Clients ask for web apps, APIs, mobile apps, cloud testing, and sometimes social engineering or internal testing in the same quarter. A single hire rarely covers all of that well. If that person leaves, your service line goes with them.
Outsourcing lets you sell the function
Outsourcing pentesting is the cleaner commercial model. You keep the client relationship. You own the proposal, the account strategy, and the margin. The testing work is handled by specialists who do it every day.
That matters because buyers do not pay for a tool run. They pay for verified findings and credible reporting. If a prospect is treating scanner output and a pentest as the same thing, send them this breakdown of DAST vs penetration testing for DevOps. It gives your sales team a simple way to explain why manual validation carries more weight.
MSP Pentesting is one example of this model. It provides channel-only white label pentesting across web, mobile, cloud, internal, and social engineering environments. For an MSP, that means you can resell application security expertise as a service instead of trying to build an expensive AppSec bench before the revenue exists.
How White Label Pentesting Works for MSPs
White label delivery is straightforward when the partner is set up for channel work.
You sell the engagement under your brand. You stay in front of the client. The testing partner performs the manual pentest, validates findings, and delivers reporting you can present as part of your broader advisory or managed service package.
The operating model that makes sense
A clean white-label workflow usually looks like this:
Scope the engagement
Define whether the client needs web app, API, mobile, cloud, external, or internal penetration testing. Tie it to the business driver, like a SOC 2 review, HIPAA concern, PCI DSS requirement, or broader risk assessment.Set communication boundaries
The MSP remains the primary relationship owner. That matters. A true channel-only partner won't try to turn your client into their direct account.Run the test and validate findings
At this stage, manual pentesting is essential. Automated scanners can help, but clients pay for validated results, clear reproduction steps, and findings that hold up under scrutiny.Deliver branded reporting
The report should be readable by engineers, managers, auditors, and compliance teams. That's what makes it useful for GRC workflows and remediation tracking.
The best white-label model is invisible to the client and obvious to your margin.
If you're building a broader security stack, a guide like this overview of managed services for security-minded partners helps frame where white-labeled testing fits.
One side note. The hiring market for security roles is noisy and inefficient, which is why many firms avoid building internal teams until demand is consistent. Even outside cybersecurity, tools like ParakeetAI's innovative assistant for job seekers show how broken the hiring process can be. For MSPs, that's one more reason to buy specialist capacity instead of chasing rare talent.
Your Checklist for a Pentest Partner
A lot of providers say they do AppSec. Fewer deliver partner-friendly penetration testing that helps an MSP retain accounts and grow revenue.
Use this checklist before you sign anything.

The questions that matter
Is the testing manual or mostly automated
You want real manual pentesting, not a scanner dressed up as a consulting engagement.Do they understand channel relationships
If they aren't channel-only, assume they may market to your client later.Are the testers certified
Ask whether the team includes OSCP, CEH, and CREST certified pentesters.Can they explain findings clearly
A report that developers can't use becomes a ticket-closing exercise, not risk reduction.Do they support compliance use cases
Your clients need reports that make sense for SOC 2, HIPAA, PCI DSS, ISO 27001, and broader GRC reviews.Can they move fast
Long lead times kill deals. Clients asking for a pen test usually already have a deadline.
The red flags to avoid
Some providers oversell methodology, underdeliver validation, and disappear during remediation questions. Others price the work so high that the MSP can't package it profitably.
If the partner can't make your service easier to sell, easier to deliver, and easier to defend, they're not a partner. They're a complication.
The right AppSec partner helps you act bigger than your internal headcount. That's the whole point. You keep the account, expand your service line, and give clients a real security outcome instead of a vague promise.
If you want to add white label pentesting, pen testing, and compliance-focused penetration testing to your portfolio without hiring a full AppSec team, MSP Pentesting is built for that channel model. Contact us today to learn more.



.avif)
.png)
.png)
.png)

