Title Tag: Burp Automated Scan for MSPs and Resellers
Meta Description: Learn how to use a burp automated scan as a force multiplier for manual pentesting. A practical guide for MSPs, vCISOs, GRC firms, and resellers focused on speed, affordability, compliance, and white label pentesting.
A client needs a penetration test for SOC 2, HIPAA, PCI DSS, or ISO 27001. They want it done fast, they do not want production disrupted, and they definitely do not want a bloated bill for a report full of junk findings.
That is where a burp automated scan gets interesting. Used well, it speeds up discovery, gives your team a working map of the app, and helps expert testers spend more time on the vulnerabilities that matter. Used badly, it becomes a noisy report generator that hurts your credibility.
Most MSPs, vCISOs, GRC firms, CPAs, and IT resellers run into the same problem. Traditional penetration testing is often too slow, too expensive, or too rigid for a service business that needs quick turnaround and predictable delivery. On the other side, fully automated pen testing is often oversold as if a scanner alone can replace a real pentest. It cannot.
The smart middle ground is simple. Use automation for breadth. Use certified people for depth. That is how you keep white label pentesting affordable without turning it into a checkbox exercise.
If you want a bigger-picture view of where automation fits, this overview of automated pen testing is a useful starting point. The key idea is the same throughout. A scanner is a force multiplier, not a substitute for an OSCP, CEH, or CREST tester who knows how to validate findings, chain issues, and explain business risk clearly.
That matters for your business. Faster testing means better turnaround. Better validation means fewer embarrassing false positives. Cleaner reports mean happier clients, stronger renewals, and less back-and-forth during compliance reviews.
Introduction
A lot of MSPs get pulled into penetration testing because their clients ask for it during a compliance push. The request usually sounds simple. “We need a pen test for our web app.” The situation is not simple at all.
If you hand that off to the wrong provider, you get long lead times, high pricing, and a generic report. If you try to solve it with only a scanner, you risk delivering something that looks technical but does not hold up under scrutiny from a client, auditor, or security lead.
Why automation matters
A burp automated scan helps because it handles the repetitive first pass quickly. It maps the application, checks common issue patterns, and gives testers a starting point without wasting hours on basic discovery.
That has significant business value for an MSP or reseller. You can move faster, scope smarter, and keep projects from stalling before the core work starts.
Why automation is not enough
The problem is not the tool. The problem is pretending the tool is the whole service.
A real penetration test needs judgment. Someone has to verify the finding, understand whether it is exploitable, measure business impact, and decide what deserves urgent attention. That is the difference between a raw scan and a professional risk assessment.
A scanner can spot patterns. A pentester decides what is real, what is noise, and what could hurt the client.
Such judgment is especially important in SOC 2, HIPAA, PCI DSS, and ISO 27001 conversations. Clients do not just need a list of alerts. They need a credible process and a report that supports remediation and compliance.
What smart resellers do differently
The best white label pentesting programs treat automation like a helper. They use it to speed up recon and coverage, then let certified testers handle the parts that machines miss. That approach keeps delivery fast without watering down quality.
For an MSP, that is the model that scales. You stay affordable. You keep client trust. You avoid selling “penetration testing” that is really just a vulnerability scan in nicer packaging.
Understanding How a Burp Automated Scan Works
A burp automated scan works a lot like a security guard inspecting a building. First, the guard walks the property and notes every door, hallway, stairwell, and entry point. Then the guard comes back and checks which of those points can be abused.
That same logic applies to web apps.
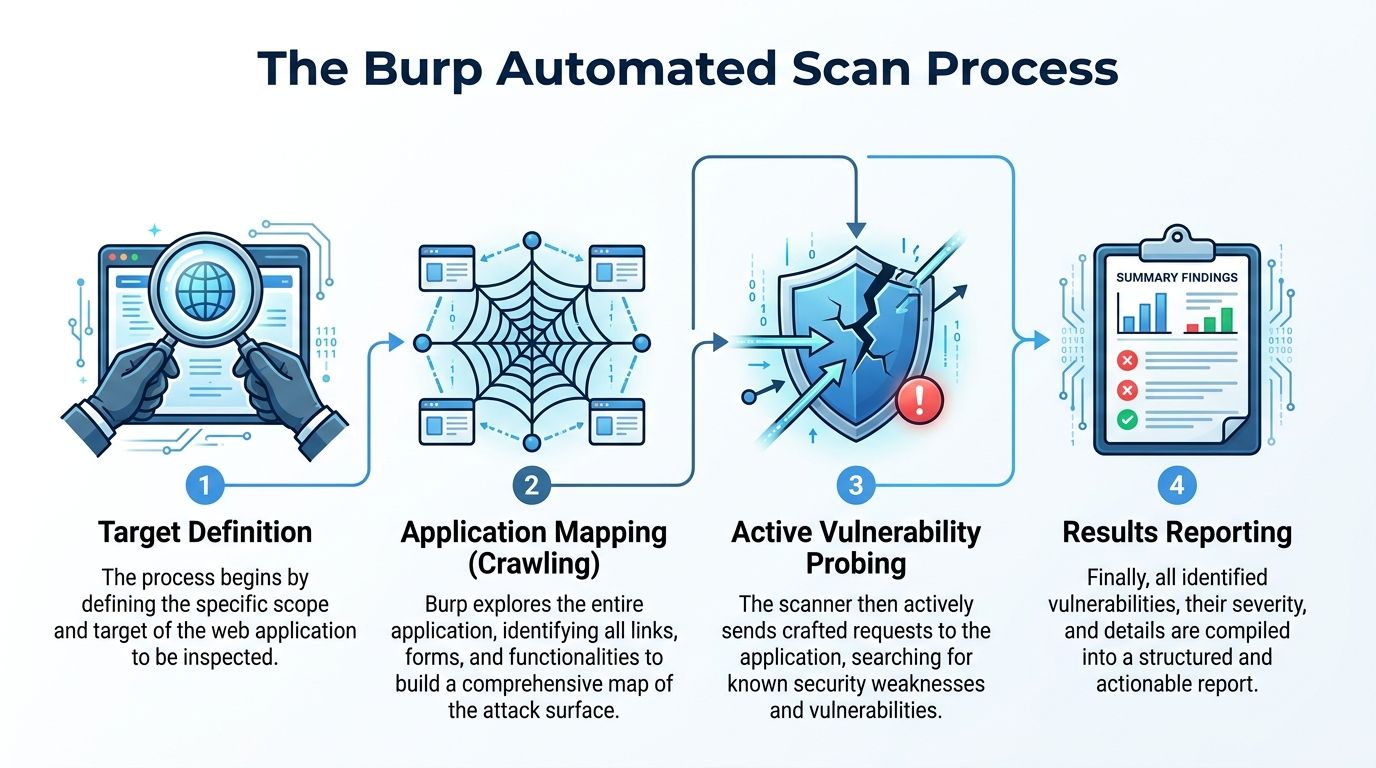
Crawling maps the application
In the first phase, crawling, Burp catalogs the application’s content and navigational paths. It follows links, submits forms, and works through the app to build a useful site map. The YesWeHack explanation of Burp’s crawling and auditing flow describes this two-phase model clearly.
This matters more than many resellers realize. If the scanner cannot map the app correctly, the rest of the test starts from a weak foundation.
A strong crawl helps the tester answer basic but important questions:
- What pages exist
- Which inputs accept user data
- Where authentication changes behavior
- Which areas deserve deeper manual review
Auditing probes for weaknesses
After the app is mapped, Burp moves into auditing. In this phase, it sends targeted payloads into discovered parameters and watches the responses for signs of weakness.
Consider this practical approach: The goal is not random noise. The goal is structured testing against known security patterns.
Typical output from this stage helps surface likely areas for:
- XSS
- SQL injection
- misconfigurations
- input handling problems
That does not mean every alert is valid. It means the scanner has done useful first-pass work.
Why this helps a real pentest
Automation gives you coverage. A human tester gives you meaning.
When a scan builds a good map of the target, a pentester can move straight into validation and deeper abuse paths instead of wasting time rediscovering application structure manually. That is a better use of billable effort and a better experience for the client.
The fastest way to ruin a pen test is to confuse “found a signal” with “proved a risk.”
For penetration testing engagements tied to compliance, this distinction matters. Auditors and security buyers care less about how many raw alerts appeared and more about whether the final report reflects a defensible testing process.
Configuring Scans for Speed and Accuracy
Most scan problems come from bad tuning, not bad tooling. If you want a burp automated scan to support a real penetration test, you need to configure it for the target, the timeline, and the client’s tolerance for disruption.
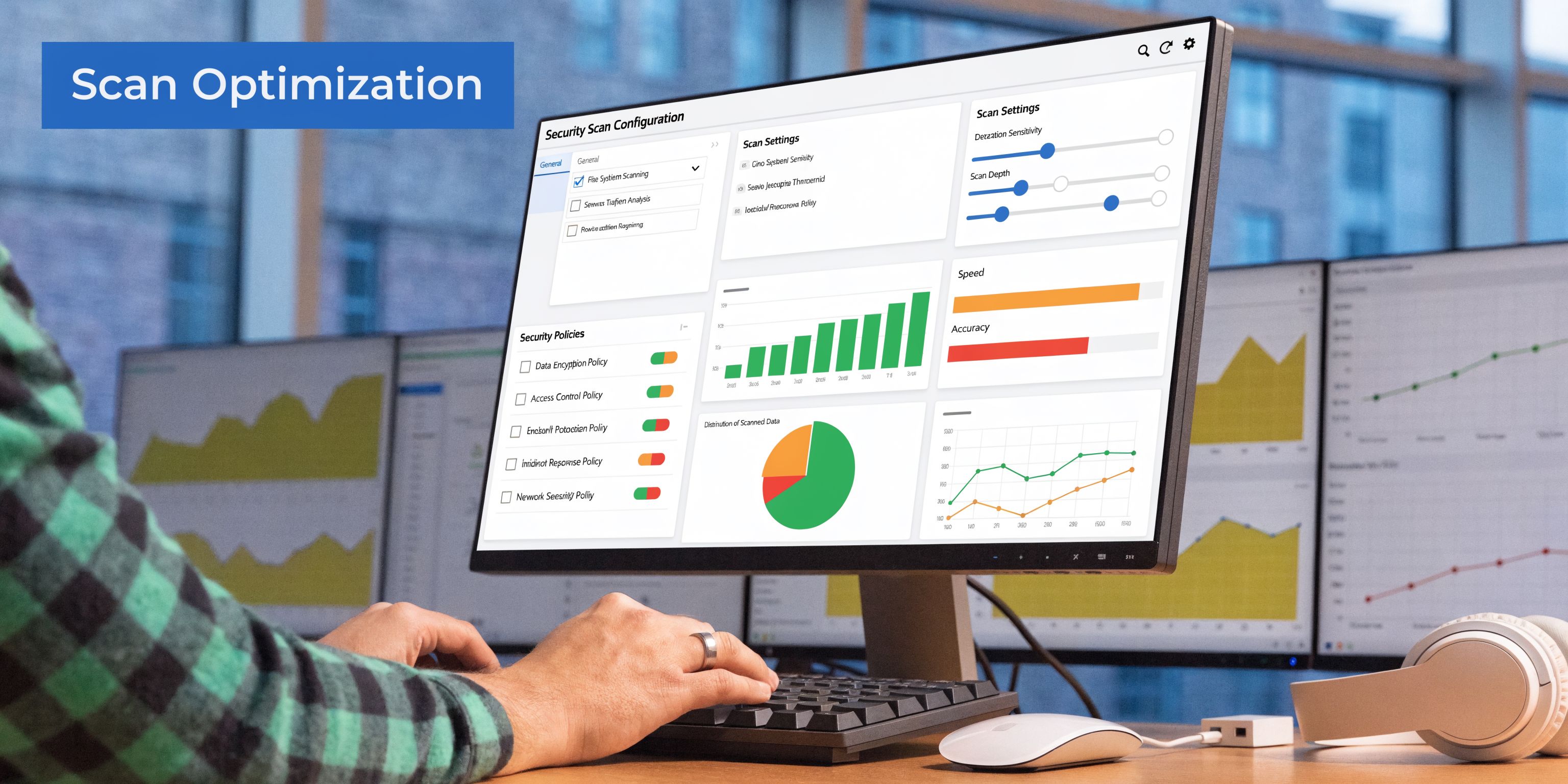
Match the scan profile to the job
Not every engagement needs the same scan depth. A production-facing client portal is different from a staging app used for an internal review. Burp supports different scan profiles, and the choice affects both speed and safety.
Consider this practical approach:
| Scan approach | Best fit | Tradeoff |
|---|---|---|
| Lighter active settings | Production-like environments | Lower risk of disruption, less depth |
| Deeper crawl and audit | Staging or tightly scoped app reviews | More coverage, more time and more care needed |
| Focused request-level testing | Known problem areas | Fast and efficient, but not broad |
If you are comparing options, this guide to web application security testing tools helps place Burp in context.
Hardware is not optional
A lot of MSPs underestimate the infrastructure side. Burp Suite DAST needs enough compute and memory to keep scans moving. According to PortSwigger’s Burp Suite DAST system requirements, the recommended specs for one complex scan are 4 vCPUs and 8GB RAM, scaling to 40 vCPUs and 80GB RAM for 10 concurrent scans.
That is not trivia. It directly affects delivery.
Under-provisioned scanning machines can throttle the process and stretch timelines. If your service promise is fast turnaround, weak infrastructure turns into missed expectations.
Good tuning protects client relationships
For MSPs and vCISOs, speed alone is not enough. You also need controlled behavior.
Poorly tuned scans can create two bad outcomes:
- Too aggressive and the client worries you are disrupting production
- Too light and the report misses obvious problems or lacks confidence
The right move is to scope tightly, tune conservatively where needed, and let manual testers decide where to push deeper. That keeps the workflow efficient without treating every environment the same.
What experienced pentesters do differently
Certified testers do not just click “scan” and wait. They choose settings based on the application, auth flow, business function, and engagement constraints. That is one reason manual pentesting remains essential even when automation is in the stack.
A seasoned tester will usually:
- Define scope carefully so the scan stays useful
- Select a profile that fits the environment
- Watch early results for noise and missed paths
- Pivot to targeted manual testing where the app gets interesting
That is how you protect speed, cost, and report quality at the same time.
Burp Pro vs DAST for Pentesting Resellers
This is the business question many resellers eventually hit. Do you need Burp Suite Professional, Burp Suite DAST, or both?
The answer depends on whether you are trying to equip an individual tester or run automated scanning at scale across multiple client environments.
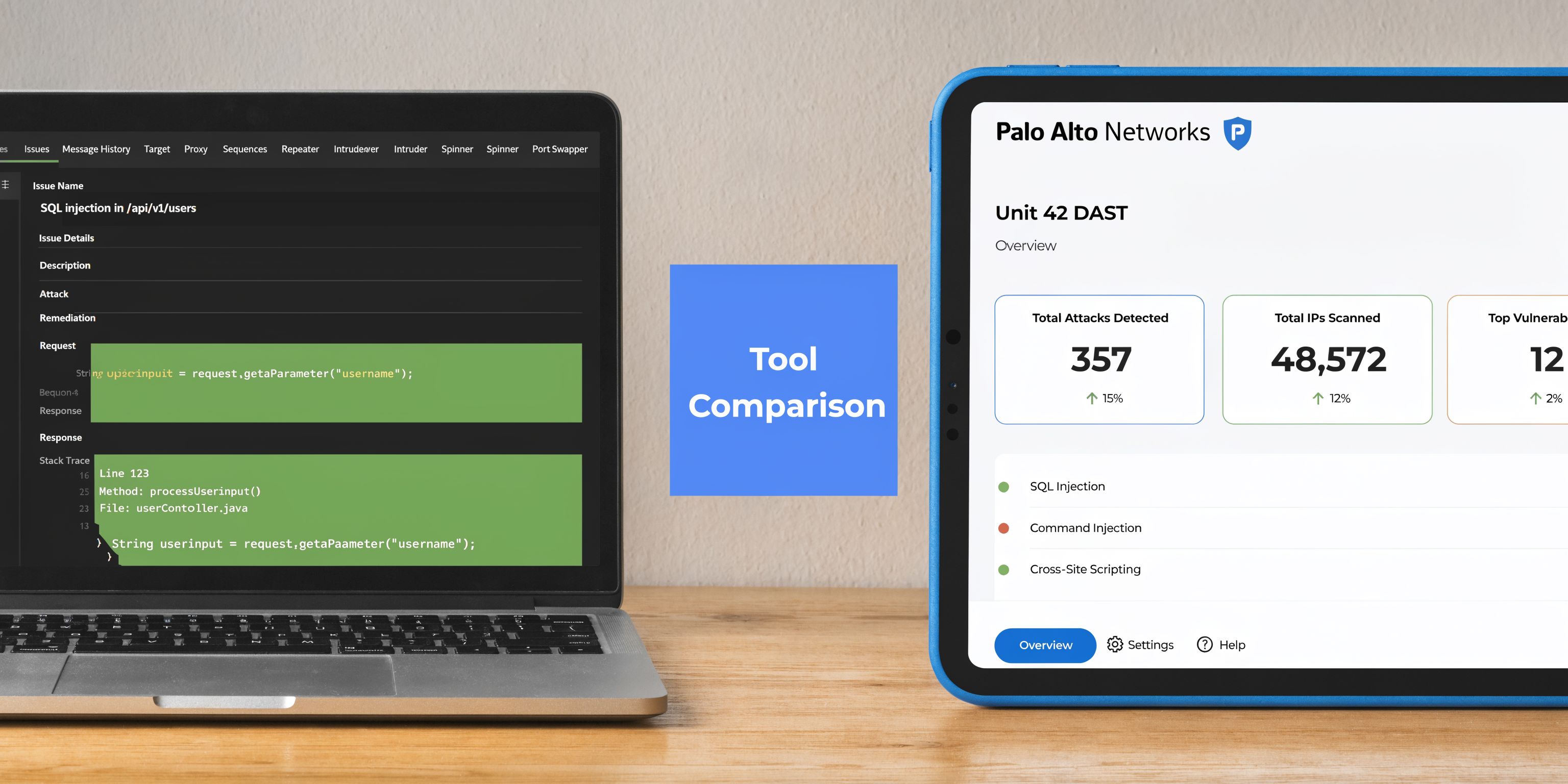
Burp Pro fits hands-on testing
Burp Suite Professional is the manual tester’s workbench. It is where a pentester validates scanner output, manipulates requests, tests edge cases, and works through logic that an automated engine will never understand cleanly.
For many smaller providers, that is the practical starting point. You get the tooling needed for real pen testing without taking on the full operational burden of a DAST deployment.
Burp DAST fits scale and process
Burp Suite DAST, formerly Burp Suite Enterprise Edition, is built for larger automated operations. According to this overview of Burp Suite DAST and the former Enterprise Edition, it can handle about 100,000 vulnerabilities with roughly 50GB of storage, supports parallel scanning of unlimited sites, and integrates with CI/CD pipelines.
That sounds attractive to an MSP, and in the right model it is. But it also means you are not just buying a scanner. You are taking on infrastructure, scan management, storage planning, workflow design, and internal expertise.
Side-by-side decision view
| Option | Best for | Main strength | Main burden |
|---|---|---|---|
| Burp Suite Professional | Individual testers and focused app work | Deep manual validation | Less built for large-scale automation |
| Burp Suite DAST | Teams running broad, repeatable scans | Parallel scanning and CI/CD workflows | More infrastructure and management overhead |
The hidden cost is operational
A lot of resellers focus on the visible product choice and ignore the invisible labor behind it. DAST makes sense if you already have the staff and process discipline to run it properly. If you do not, it can become shelfware or a source of bad reports.
That is why many white label pentesting programs are better off using a specialist partner model instead of trying to build enterprise-grade web app testing operations from scratch. The issue is not whether DAST is capable. It is. The issue is whether your business should own that complexity directly.
If your team is still solving basic delivery workflow problems, buying more scanning capacity will not fix the service model.
What most MSPs should do
If you sell compliance and security services, keep your focus on client outcomes. The client wants a credible penetration test, a clear report, and a reasonable timeline. They do not care whether you spent months standing up an internal DAST operation.
For many MSPs, the strongest model is simple:
- Use enterprise automation where it makes delivery faster
- Keep manual expertise at the center of the engagement
- Avoid turning a tooling purchase into an operations burden
- Protect margin by not overbuilding in-house too early
That approach is usually more practical than trying to become a full-time application security shop overnight.
Managing False Positives with AI and Expertise
False positives are where automated security services lose trust. A scanner flags something, the client asks a basic follow-up question, and nobody can prove the issue is real. That is how an MSP damages its reputation in one call.
A burp automated scan is useful only if somebody triages the output properly.

What Burp AI is trying to fix
Burp AI was introduced to reduce false positives, with an initial focus on Broken Access Control, which is known for high noise. This analysis of what Burp AI changes in a real Burp workflow also makes an important point. The goal is to augment, not replace, the pentester.
That is the right framing.
AI can help reduce the time spent chasing weak scanner leads. It can help a tester understand odd responses faster. It can support issue exploration. Those are good uses.
If you want a broader view of where AI belongs and where it does not, this page on automated and AI pentesting is worth reviewing.
Why human validation still matters
A real pentester does several things AI cannot own responsibly in a client-facing engagement.
First, the tester validates whether the issue is exploitable. Second, the tester decides whether the finding matters in context. Third, the tester writes remediation guidance in language a client can use.
That final piece is often ignored. A weak report says “possible vulnerability detected.” A strong report says what happened, how it was reproduced, what the business impact is, and what the client should fix first.
Where AI helps the workflow
Used properly, AI can shrink the slow parts of the loop:
- Interpreting unfamiliar responses
- Following up on noisy scanner results
- Reducing time lost on weak access control leads
- Helping testers focus on the findings that deserve manual attention
That improves speed. It does not remove the need for judgment.
For white label pentesting, unvalidated findings are worse than no findings. They create doubt about the entire report.
The compliance angle
For SOC 2, HIPAA, PCI DSS, and ISO 27001, a noisy scanner dump is not enough. Clients and auditors need evidence that somebody reviewed the results and turned them into a usable security document.
That is why the validation phase is so important in manual pentesting. It converts raw output into something credible. It strips out junk. It adds context. It gives the client a report they can act on.
What to avoid
Do not market AI-enhanced scanning as if it solved the hard part of penetration testing. It did not.
The challenging aspect remains the human element:
- deciding whether the issue is real
- chaining technical issues into meaningful attack paths
- explaining business impact clearly
- separating urgent remediation from background noise
AI is a helpful assistant. Your credibility still comes from expert review.
Integrating Scans into Your Pentest Workflow
A burp automated scan is not a full penetration test. It is one stage in a professional workflow.
That distinction matters because many buyers hear “automated scan” and assume they are getting the same value as a manual pen test. They are not. They are getting the front end of the process.
Use the scan as the map
The best workflow uses automation to map the application and surface initial findings. After that, the tester works manually.
Effective teams often use Burp’s automated output to build the site map, identify areas worth investigating, and then move into tools like Repeater and Intruder for refinement and validation. Focused manual testing launched from specific requests in the sitemap can save hours compared with broad crawling alone. That is the practical workflow described earlier in the article.
Use manual testing for depth
Significant security value appears in this stage.
Manual penetration testing is what finds the issues that matter most in many applications:
- business logic flaws
- auth weaknesses tied to workflow
- privilege problems that depend on user role changes
- exploit chains that require timing, context, or creativity
A scanner can help point a tester toward some of these areas. It cannot reason through all of them.
A simple working model
For MSPs and resellers, the cleanest delivery model usually looks like this:
- Automate first-pass discovery to save time
- Review findings manually before anything reaches the client
- Probe high-value paths with hands-on testing
- Write the final report around validated risk, not raw alerts
This is how you keep the service both affordable and credible.
Why this works commercially
Automation lowers the cost of repetitive work. Manual expertise raises the value of the outcome.
That combination is what makes white label pentesting practical for service providers. You are not paying experts to do basic site discovery by hand when a scanner can accelerate it. You are paying them to do what only skilled testers can do.
Common Automated Scanning Mistakes MSPs Must Avoid
The biggest mistake is calling a scan report a penetration test. Clients may not catch the difference at first. Security teams and auditors often do.
That mistake creates downstream pain fast.
Mistake one with raw scanner dumps
A raw report looks busy, but it often lacks proof, context, and prioritization. If a client challenges a finding and you cannot validate it, your brand takes the hit.
Mistake two with poor tuning
Some MSPs run scans too aggressively in client environments because they want quick coverage. Others go too soft and end up with shallow results.
Both are service failures. One risks disruption. The other risks low-value output.
Mistake three with no business context
Even valid findings can be badly reported. A low-level technical issue on a public login path may deserve more attention than a noisier issue buried in an unused area of the app.
Clients need business meaning, not just severity labels.
Mistake four with overreliance on automation
Automated scanning is good at repeatable checks. It is weak at understanding process abuse, role logic, and weird edge cases. Those are often the places where important app risks hide.
A good pentest report answers “so what?” not just “what was flagged?”
What disciplined providers do instead
Strong providers separate discovery from validation. They keep scope tight, tune carefully, and make sure a human reviews every material finding before the report goes out.
That protects the MSP in three ways:
- Client trust stays intact
- Compliance conversations go smoother
- The service looks professional instead of improvised
Frequently Asked Questions About Burp Automated Scanning
Can a burp automated scan replace a full manual pentest
No. It can speed up discovery and help identify likely vulnerabilities, but it does not replace manual pentesting. A real penetration test requires validation, exploitation logic, business context, and reporting that a scanner alone cannot provide.
How does this fit into PCI DSS or ISO 27001 work
A burp automated scan can support vulnerability management and help gather evidence during a security review. For PCI DSS or ISO 27001, the stronger deliverable is still the final human-reviewed report that shows what was tested, what was validated, and what should be fixed.
Is this the same as a Tenable or Qualys scan
No. Those tools are often associated with broader infrastructure or vulnerability scanning programs. Burp is a DAST tool focused on web application behavior.
That makes it useful in application-focused penetration testing, especially when paired with manual testing.
Is Burp enough for every kind of pentest
No. Burp is strong for web applications and related workflows. It is not the whole answer for every environment.
An MSP supporting clients across cloud, internal networks, mobile, physical security, and social engineering needs a wider methodology than one scanner.
What should a reseller ask before offering this service
Ask five simple questions:
- Who validates findings before the report is delivered
- How is production safety handled during scanning
- What certifications back the testers doing the manual work
- How are compliance-driven reports written
- Is the service white labeled and channel-friendly
Those questions will tell you very quickly whether you are looking at a real pentesting program or just automated output dressed up as one.
Conclusion
A burp automated scan is a strong tool. It speeds up mapping, improves coverage, and helps pentesters spend time where they add the most value.
It is not a replacement for real penetration testing. The value still comes from expert validation, manual abuse testing, and clear reporting that a client can trust. That is what supports compliance, protects your reputation, and keeps the service worth buying.
For MSPs, vCISOs, GRC firms, CPAs, and resellers, the smart model is straightforward. Use automation for efficiency. Keep certified human expertise at the center. That is how you deliver affordable, fast, and credible white label pentesting without sacrificing quality.
Stop losing deals to slow providers, inflated pricing, and weak testing methodology. Contact us today to learn more.
MSPs, vCISOs, and resellers that need fast, affordable, white label pentesting can work with MSP Pentesting. We are a channel-only partner, we never compete with our partners, and our OSCP, CEH, and CREST certified pentesters deliver expert-led manual pentests with quick turnaround. Contact us today to grow your security revenue without building the whole operation in-house.



.avif)
.png)
.png)
.png)

