[Operational Level Agreement for MSPs and vCISOs]
You promised a client a fast penetration test for an urgent SOC 2 deadline. Sales said the scope was simple. The technical team found missing credentials. Scheduling assumed the client wanted next week. Compliance expected a draft report almost immediately.
Nobody lied. Everyone just worked from a different set of assumptions.
That’s how MSPs lose trust. Not because they can’t sell security. Because their internal process breaks when a client needs speed, clean handoffs, and a report that supports compliance. If you resell white label pentesting, your internal mess becomes the client’s problem fast.
Stop Internal Chaos From Ruining Client Trust
An operational level agreement fixes the stuff clients never see but always feel. It creates internal rules between sales, project management, certified pentesters, compliance teams, and support so a pentest or pen test doesn’t get stuck in limbo.

One common failure looks like this. Your account manager closes a penetration testing deal for a web app and external network. The client expects a quick kickoff because their auditor is waiting. But your internal team still hasn’t confirmed test windows, business hours, emergency contacts, or who owns the first review of findings.
The result is predictable.
- Sales gets blamed because scope wasn’t documented cleanly.
- The pentest team gets blamed because delivery slipped.
- The client gets nervous because silence feels like incompetence.
- Your margin gets hit because rework and status chasing eat hours.
An SLA tells the client what they’ll get. An OLA tells your own people how to make sure it actually happens.
This is bigger than one delayed report. It’s part of building strong operational resilience. If your process falls apart under pressure, the client won’t care whether the bottleneck was scheduling, scoping, or a slow internal handoff. They’ll remember that you missed the moment.
OLA vs SLA What MSPs Need to Know
Most MSPs confuse an operational level agreement with a service level agreement. They’re related, but they’re not the same thing.
The easiest way to understand it is a restaurant. The SLA is the promise made to the customer that dinner will hit the table on time. The OLA is the agreement between the kitchen, server, and expeditor on who does what, in what order, and by when.
The restaurant analogy works
If the customer is told the meal arrives in 20 minutes, the kitchen can’t start cooking whenever it feels like it. The server can’t wait around before placing the order. The expeditor can’t forget to call pickup. The customer only sees one promise, but several internal teams have to keep it.
That’s exactly how a pen test engagement works for an MSP, vCISO, CPA, or GRC firm.
AgreementWho it’s forWhat it coversSLAExternal clientDelivery promise, turnaround, service expectationsOLAInternal teams and partnersHandoffs, ownership, response targets, escalation rules
What this means in pentesting
Your client-facing SLA might promise a fast pentest report for a PCI DSS or HIPAA project. Your OLA should spell out how internal teams support that promise.
That usually means defining things like:
- Scope approval ownership so sales doesn’t pass half-baked requirements
- Scheduling rules so the tester knows when access will be ready
- Internal escalation paths when credentials, whitelisting, or target access are missing
- Review responsibilities so draft reports don’t stall in someone’s inbox
If your agreements are scattered across email, Slack, and memory, they aren’t agreements. They’re wishful thinking. Good teams treat documentation as part of execution, which is why disciplined shops invest in effective agreements management instead of relying on tribal knowledge.
How OLAs Drive MSP Profitability and Growth
A lot of MSPs hear “operational level agreement” and think bureaucracy. That’s a mistake. A strong OLA protects margin.
If you resell penetration testing, you already know where profit disappears. It disappears in unclear scope. It disappears in rescheduled kickoff calls. It disappears when a tester waits for access while your PM sends reminders and your client asks for updates. Those aren’t technical problems. They’re operating problems.

One underserved angle in existing OLA content is the lack of specific guidance on integrating OLAs into cybersecurity services for MSPs, particularly for penetration testing workflows, despite MSPs handling critical security SLAs with clients. A 2025 Gartner report notes that 68% of MSPs miss security SLAs due to poor internal coordination, with only 22% using formalized OLAs for red teaming dependencies like cloud infrastructure and social engineering tests (reference).
Where the money leaks
Without an OLA, your team keeps solving the same avoidable problems:
- Scope creep from vague statements of work
- Slow partner handoffs when no one owns next action
- Rework because findings weren’t reviewed the right way
- Client frustration when updates are late or inconsistent
That hurts more in security than in basic IT support. A missed deadline on a routine ticket is annoying. A missed deadline on a manual pentesting engagement tied to SOC 2, ISO 27001, or a lender’s risk assessment can cost you renewals and referrals.
Why growth depends on internal discipline
Fast growth exposes bad process. The more web apps, internal networks, mobile apps, cloud reviews, and social engineering projects you take on, the more important internal consistency becomes.
Practical rule: If your white label service depends on speed, your internal handoffs need more discipline than your external sales pitch.
An OLA helps you standardize delivery across account managers, PMs, vCISO advisors, and technical resources. That gives you cleaner forecasting, fewer status meetings, and more room to sell profitable follow-on work instead of apologizing for delays.
Key Components of a Strong Pentesting OLA
A good operational level agreement for pentesting shouldn’t be long. It should be clear. If your team can’t read it and know exactly what to do, it’s too vague.
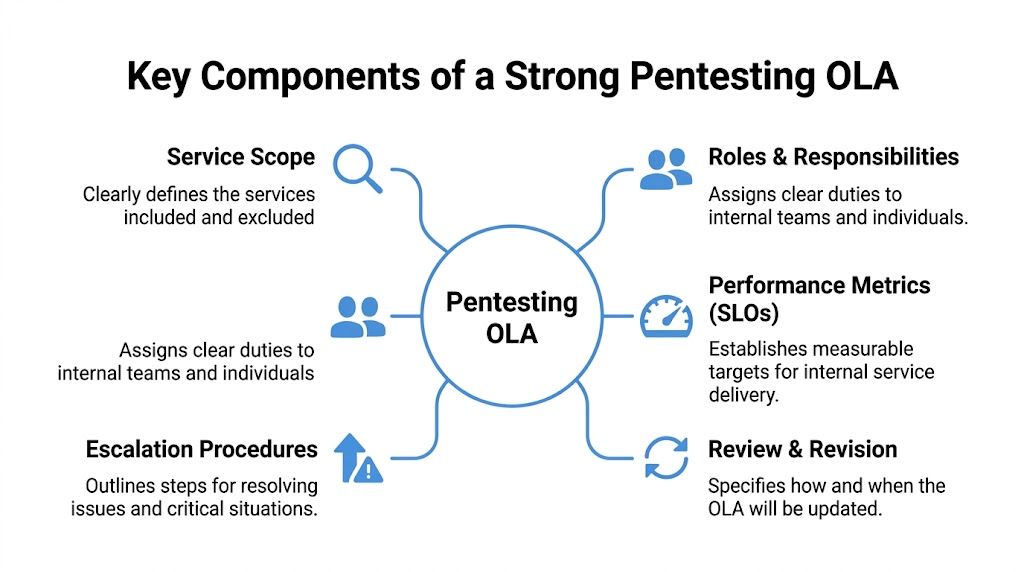
In MSP pentesting operations, an OLA establishes precise internal benchmarks between teams. Key specifications include Service Level Objectives such as response times under 4 hours for high-priority vulnerability escalations, 95% of critical findings mitigated within 48 hours, and 99.5% uptime for red teaming tools. The same source notes that a 2-hour delay in handoffs can extend a 5-day pentest to 8 days, which can push you into an SLA breach (ManageEngine guidance).
Start with service scope
Your OLA must say what service is being supported. Don’t write “security testing.” Write the actual service.
Examples include:
- Web application penetration testing
- External network pen testing
- Internal network pentest
- Mobile application testing for iOS and Android
- Physical penetration test support
- Social engineering engagement handoffs
Also define what isn’t included. If beta apps, custom IoT testing, or after-hours retesting aren’t covered, say so.
Assign names and ownership
Roles matter more than broad teams. “Security” is too vague. “OSCP-certified lead tester reviews findings before draft release” is useful.
Include:
- Who approves scope
- Who confirms scheduling
- Who validates client access and credentials
- Who reviews false positives
- Who owns final report QA
- Who updates the client-facing team
Certified talent is essential. If you’re running a serious penetration testing practice, note whether the assigned resource is OSCP, CEH, or CREST qualified for the engagement type.
Define measurable service levels
Most MSPs fail here because they use soft language. Don’t say “respond quickly.” Say exactly what internal success looks like.
Good OLA metrics often include:
- Internal acknowledgement targets for urgent findings
- Draft report review windows
- Retest scheduling expectations
- Tool availability requirements
- Escalation trigger points when a blocker sits too long
If the metric can’t be tracked, the team won’t manage it consistently.
If you need a clean model for the reporting side, this pen test report template is a useful reference for aligning report workflow with internal ownership.
Build escalation into the document
Escalation shouldn’t be emotional. It should be automatic.
If a client hasn’t provided access, the PM should know when to escalate. If a critical finding needs review before client delivery, the vCISO or technical lead should know who gets pulled in. If a report is blocked in QA, there should be one owner, not five people “checking on it.”
A strong OLA usually answers these questions:
SituationInternal responseMissing credentialsProject manager escalates to account ownerHigh-priority finding needs reviewAssigned technical lead acknowledges and routesDraft report stuck in approvalEscalate to delivery managerTest window changes lateNotify sales and client success immediately
Review and revise it
Your OLA should evolve with the services you sell. If you add cloud pentests, mobile app reviews, or broader compliance support tied to SOC 2 or PCI DSS, update the document.
A stale OLA creates the same chaos as no OLA. It just hides the problem behind a file nobody follows.
Sample OLA Clauses for Reselling Pentesting
Theory is nice. Clauses are better.
BMC notes that core OLA components for MSPs include listing responsible parties, working hours, and contacts. It also recommends metrics such as MTTA under 30 minutes for internal alerts and MTTR under 24 hours for false positive triage, while noting that poorly defined dependencies cause 40% of SLA misses (BMC analysis).
Client onboarding and scoping handoff
Sample clause: Upon receipt of a signed statement of work for a penetration test, the account manager will submit finalized scope, target list, testing window, client contacts, and special constraints to the delivery coordinator. The delivery coordinator will confirm completeness before scheduling the assigned tester. Missing access details or undefined assets will be escalated internally before the engagement start date.
This clause stops the classic sales-to-delivery mess.
Critical vulnerability reporting workflow
Sample clause: For a critical finding identified during manual pentesting, the assigned tester will notify the internal technical lead according to the agreed internal alert path. The internal client owner will coordinate external communication to the client’s security or IT team, document the handoff, and track remediation status until closure or formal acceptance.
This protects the relationship. It keeps technical urgency from turning into communication confusion.
Draft and final report delivery
Sample clause: The assigned tester will submit the draft report for internal quality review after test completion. Internal reviewers are responsible for validating severity, business context, and false positive concerns within the defined review window. Final delivery to the reseller or client-facing partner will occur only after QA approval and formatting review for white label consistency.
If you sell under your own brand, your process has to support that brand. A real white label penetration testing workflow is therefore essential.
- Use names, not departments. Ownership gets fuzzy when everyone assumes someone else has it.
- Write business-hour assumptions down. If your partner thinks after-hours testing is included and your delivery team doesn’t, the argument starts before the pentest does.
- Document exception handling. Retests, out-of-scope findings, and rushed audit deadlines need predefined rules.
Implement Your OLA and Partner for Success
An operational level agreement won’t make a weak service strong. It will make a good service repeatable.
That’s the real point. MSPs, vCISOs, resellers, CPAs, and GRC firms need a delivery model that can handle fast-moving penetration testing projects without burning margin or damaging trust. Clear internal ownership gives you that. It helps you move faster, reduce confusion, and support audit-driven work like SOC 2, HIPAA, PCI DSS, and ISO 27001 without constant fire drills.
You also need the right delivery partner behind the workflow. If your internal process is tight but your pentest provider is slow, overpriced, or sloppy, the OLA won’t save you. Partner with a team that fits the model. Fast turnarounds, affordable pricing, manual pentesting, and certified testers aren’t nice extras. They’re the baseline for a scalable reseller service.
If you’re building or cleaning up your reseller process, start with your handoffs. Then align them with a real pentest partner program that won’t compete with you.
If you want a channel-only team for fast, affordable, white-labeled pentests delivered by OSCP, CEH, and CREST certified pentesters, talk to MSP Pentesting. We help MSPs, vCISOs, and resellers offer manual pentesting under their own brand without the inflated pricing, weak methodology, or long lead times that kill client trust. Contact us today.



.avif)
.png)
.png)
.png)

