PCI DSS 4.0 isn't just a small update. It's a completely new way of thinking about security. The old routine of running a "check-the-box" annual penetration test and calling it a day is officially over.
Version 4.0 requires a continuous, risk-based approach to finding vulnerabilities. This makes the entire pen test process more important and more frequent than ever before. For Managed Service Providers (MSPs) and vCISOs, this is a big opportunity.
Why PCI DSS 4.0 Penetration Testing Changes Everything
The compliance industry has a problem. You see it in inflated prices, bad testing methods, and long wait times. Your clients are struggling with these stricter rules for PCI DSS, SOC 2, and HIPAA, and they need a guide. That guide can be you.
This is your chance to offer the security testing your clients desperately need. You solve their compliance headache and build a new revenue stream, all without hiring an expensive in-house security team. We provide the fast, affordable, and completely white-labeled manual pentesting that makes it possible. We are a channel-only partner, so we never compete with you.
Understanding the New PCI DSS 4.0 Pentest Rules
The old way was simple, but it left huge security gaps. Running a single penetration test once a year doesn't work because attackers don't operate on an annual schedule. PCI DSS 4.0 finally fixes this by requiring a more active approach.
The biggest change is in Requirement 11.4. The rigid, once-a-year pen test is gone, replaced by a schedule based on risk. A penetration test is still required at least annually, but it also has to be done after any big change to the system. For a client who is always updating their apps or network, that could mean quarterly tests.
Defining Your PCI DSS 4.0 Pentest Scope Correctly
Getting the scope right for a PCI DSS 4.0 penetration test is the most important step. If you get it wrong, your client could fail an audit and have a false sense of security. This isn't just about scanning a few public IPs anymore.
Think of your client's Cardholder Data Environment (CDE) like a bank vault. An old-school pen test might have just checked the main vault door. PCI 4.0 demands you check the door, the walls, the air vents, and any connected tunnels. If a system can touch the CDE, it’s in scope.
What's Included in the Cardholder Data Environment (CDE) Scope?
Defining the CDE is where it all begins. It includes every piece of tech that stores, processes, or transmits cardholder data. It also includes any system that could impact the security of the CDE, even indirectly.
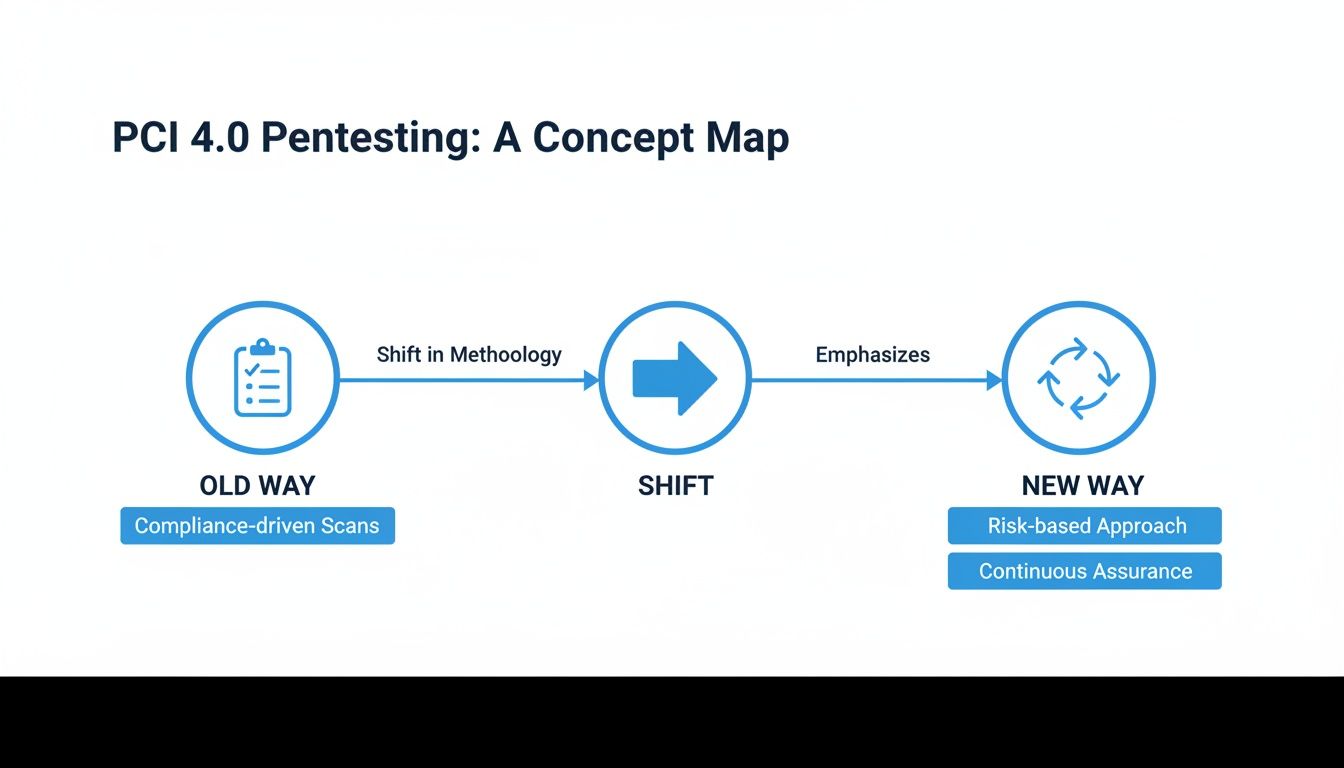
Your pentest scope must cover internal and external networks, web applications, cloud infrastructure, and all connected systems. This image shows how much things have changed. We've moved from a simple checklist to a continuous, risk-focused approach where frequent penetration testing is key.
As an MSP or vCISO, having a specialist partner is a game-changer. Proper scoping requires deep network knowledge and a solid risk assessment. You can find more details in our guide on PCI compliance tests. Working with our OSCP, CEH, and CREST certified pentesters ensures you design a scope that satisfies PCI DSS and actually makes your client more secure.
Different Penetration Tests Required for PCI DSS 4.0
Your clients can’t just run one generic penetration test for PCI DSS 4.0. To get compliant, they need to show they’ve tested their defenses from multiple angles. As their trusted MSP or vCISO, you need to know these tests to guide them.
It's like securing a fortress. You check the main gate, the walls, the tunnels, and the supply routes. Each pen test covers a different attack path, building the complete security picture that auditors and other frameworks like HIPAA and SOC 2 demand.
The classic external penetration test simulates a hacker on the internet. Then you have internal penetration testing, which assumes the attacker is already inside. Both are crucial for a complete risk assessment.
Web applications are a huge target, which is why application layer penetration testing is required. This is a deep, manual pentesting engagement where our certified experts find flaws that automated scanners miss. The test that often trips people up is the segmentation test. It proves that the CDE is truly isolated from the rest of the network. A failed segmentation test is an automatic audit failure.
Why Methodology and Qualified Pentesters Are So Important
Not all penetration testing is the same. For years, many providers sold a simple automated scan and called it a pen test. PCI DSS 4.0 now requires a documented methodology and a qualified, independent tester. This is about real security, not just checking a box.
This means you can no longer just find the cheapest option. An auditor will demand proof that your client's pen test followed a recognized industry standard. The methodology is the tester's game plan, ensuring the test is thorough and repeatable. For MSPs, understanding the right methodology for penetration testing is vital.
PCI DSS 4.0 also demands that the penetration test be done by a "qualified" and "independent" tester. While PCI doesn't list specific certifications, auditors use them as proof of a tester's skill. This is where credentials like OSCP, CEH, and CREST make a huge difference. These certifications prove our pentesters can think like real attackers and find vulnerabilities manually.
Our commitment is to 100% manual pentesting performed only by testers holding these top certifications. As a reseller, this is your advantage. You can confidently tell your GRC and vCISO clients that your white label pentesting services are backed by verified experts. This gives them peace of mind that their compliance is in good hands.
How To Sell White Label Pentesting For Your MSP
This PCI DSS 4.0 compliance challenge is a massive opportunity for your MSP or vCISO practice. Your clients are already looking for PCI DSS 4.0 penetration testing. If you don’t sell it to them, someone else will.
The key is to stop talking about technology and start talking about business risk. Your clients care about avoiding fines, protecting their brand, and meeting compliance for PCI, SOC 2, and HIPAA. A real manual pentesting engagement isn't a cost; it's an insurance policy.

As an MSP or vCISO, you’ve already earned their trust. Our white label model lets you be the hero. You own the relationship, and our team of OSCP, CEH, and CREST certified pentesters do the work. We give you partner pricing, and you sell it at a margin that works for you.
We are a channel-only company. We never sell directly to your clients or compete with you. We help you grow your business without the cost of hiring an in-house pentesting team. You can get more details in our guide on white label penetration testing.
Partner With Us For Fast and Affordable Pentesting
The compliance industry is known for high prices, slow service, and weak penetration testing. We built our business to fix this problem for MSPs, vCISOs, and IT resellers. You need a partner who makes you look good.
We deliver affordable, 100% manual penetration testing from a team of certified experts (OSCP, CEH, and CREST). This is proof our team can uncover vulnerabilities that automated scanners miss. For meeting the demands of PCI DSS 4.0, this is critical.
Our model is simple: we are a channel-only partner. We will never compete with you. Partner with us, and you can immediately start offering a full suite of pentesting services under your own brand for frameworks like PCI DSS, SOC 2, and HIPAA.
Nothing kills a deal faster than a long wait. While other providers take months, we deliver a comprehensive report in about a week. This speed helps you solve your client's compliance problem now. It’s time to offer the expert pen test services your clients are searching for, all under the brand they already trust.
Contact us today to learn more about our reseller program.
Your Clients' Top PCI DSS 4.0 Pentesting Questions
Your clients have questions about PCI DSS 4.0 penetration testing, and they expect you to have answers. Here are some of the most common questions our MSP and vCISO partners hear, with the answers you need.
How often does PCI DSS 4.0 require a pentest?
Under Requirement 11.4, clients need a penetration test at least once a year and after any "significant change" to their Cardholder Data Environment (CDE). For service providers, segmentation testing is required at least every six months. For many businesses, an annual pen test is just the beginning.
Can we just use an automated scanner for our pentest?
No. While automated vulnerability scanning is a separate PCI requirement, penetration testing (11.4) must be a manual pentesting process. The goal is to mimic a real-world attacker, which requires a human expert. Relying on an automated tool alone will leave your client non-compliant and at risk.
What makes a pentester "qualified" for PCI DSS 4.0?
PCI DSS 4.0 is clear: the tester needs to be independent and have verifiable skills. Auditors look for certifications as proof of expertise. Certifications like OSCP, CEH, and CREST are the gold standard. They prove a tester has the advanced, hands-on skills to satisfy an auditor and find real risks.
This is why we only use certified professionals for our white label pentesting services. It ensures you can confidently deliver high-quality, affordable testing for clients who need to meet compliance for PCI, SOC 2, or HIPAA.
Partnering with us gives you an instant, high-margin service that solves a major problem for your clients. Contact us today to learn more about our reseller program.


.avif)
.png)
.png)
.png)

