An attestation letter is like a formal handshake (with a letter) that proves your client’s security work is done right. For Managed Service Providers (MSPs), vCISOs, and GRC companies, this is more than just paper. It’s a formal declaration that turns security claims into solid proof, especially after a penetration test. This document transforms a technical report into a business asset that auditors and clients trust.
What An Attestation Statement Means For Your MSP

An attestation statement is a professional opinion backed by solid evidence. In cybersecurity, it's the document that says, "Yes, we've audited the security, and this is what we found." It's not just a summary; it's an assurance that gives your clients peace of mind.
This document is critical for any MSP or vCISO. When your client faces an audit for SOC 2, HIPAA, or PCI DSS, a simple checklist isn't enough. They need proof that can be verified. An attestation statement, especially one built on a thorough penetration test, delivers exactly that.
How Attestation Statements Turn Data Into Trust
A standard pentest report is full of technical details about vulnerabilities. That’s useful for your tech team, but it won’t prove compliance to a CEO or an auditor. They would be lost in the technical jargon.
This is where the attestation statement is so valuable. It translates those dense technical findings into a clear, concise statement of assurance. It’s a bridge between a technical risk assessment and the business's need for trust.
As a channel-only partner, we understand your role. You own the client relationship, and our job is to provide tools that strengthen it. Our fast, affordable, and manual pentesting services are designed specifically for this purpose. We never compete with you for your clients.
Our pentesters, holding certifications like OSCP, CEH, and CREST, perform deep-dive penetration testing. The detailed report we provide, often in under a week, is the solid evidence you need to back up a strong attestation. It helps you prove to clients that you're not just managing IT; you're securing their business and guiding them through compliance.
Understanding Your Role In The Attestation Process
Compliance frameworks like ISO 27001 and SOC 2 are built on independent verification. They require a third party to examine the evidence and attest to the state of security. An automated scanner might find some common issues, but it lacks the human intelligence to spot complex business logic flaws that lead to major breaches.
This is why manual pentesting is essential for credible attestations. Our hands-on approach provides the robust evidence auditors demand. It proves that a real, thinking attacker has tried to break in, or that found vulnerabilities have been fixed. For more context, it's helpful to see how this fits into broader Managed Service Provider best practices. This process transforms your security service from a cost into a business enabler for your clients.
The Role Of Attestation In SOC 2 and HIPAA
In the compliance world, attestation statements are the final word. For any MSP, vCISO, or GRC company guiding a client through an audit, you know it’s not enough to say security controls are in place. You have to prove they work.
Attestations are that proof. They are the official, signed declarations that confirm security measures are effective. For a SOC 2 audit, the auditor's opinion is the attestation. Without it, the entire audit process is incomplete.
For frameworks like SOC 2 and HIPAA, the attestation statement is everything. It’s the formal verification that an organization has done the work to protect sensitive data. These aren't "trust me" exercises; they demand independent validation. The best way to get that validation is through a real-world test. A rigorous penetration test delivers the evidence that makes an attestation defensible.
The findings from a manual pentesting engagement show that security controls were not just designed well, but that they held up against a determined attacker. This is where we come in. Our fast, manual pentest reports—backed by our OSCP, CEH, and CREST certified experts—give you the concrete data you need. This is the evidence that underpins a rock-solid attestation statement, empowering you to guide clients through audits with confidence.
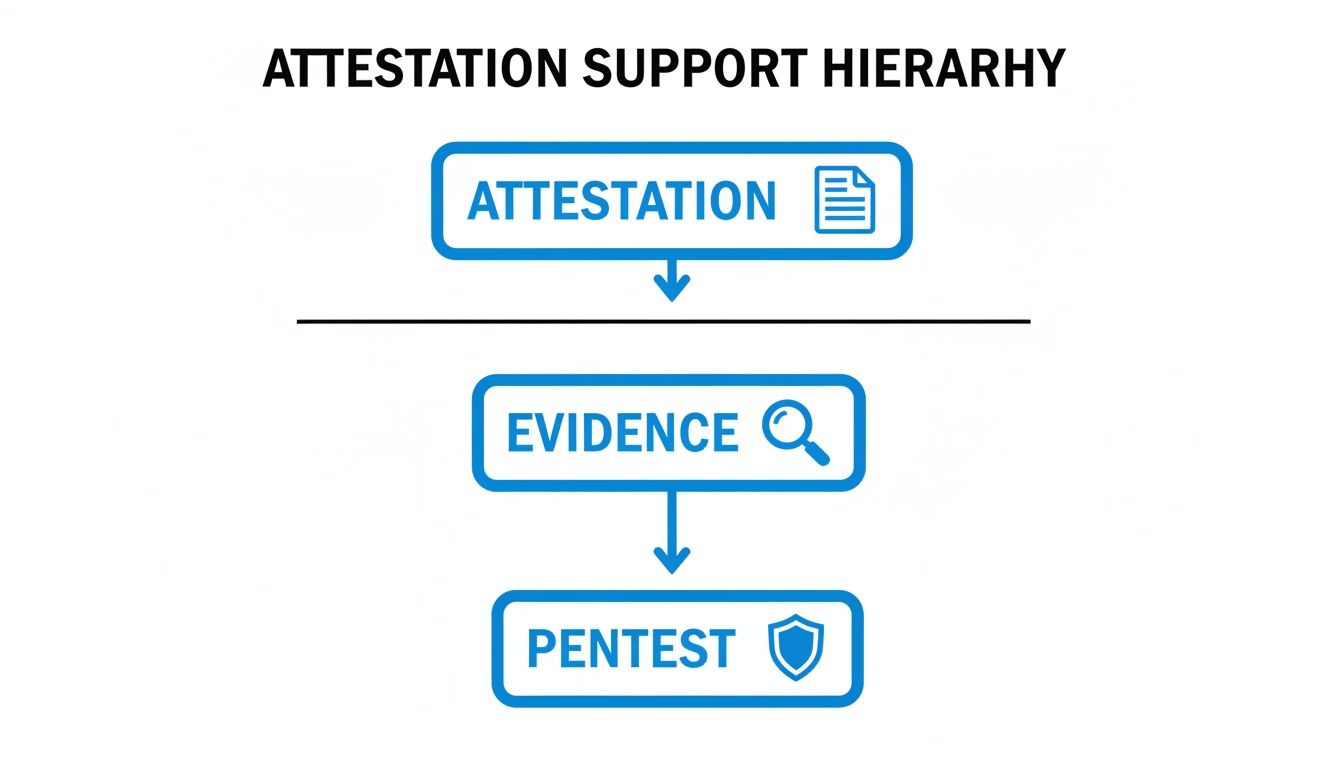
How Penetration Testing Supports Your Attestation
An attestation statement without solid evidence is just an empty promise. A manual penetration test is that proof, turning your client’s security claims into credible, verifiable facts. A pen test simulates a real-world attack on a client's systems. The findings become the backbone of your attestation.
For example, you might state, "A qualified third party conducted a penetration test on our external network, and no critical vulnerabilities were found." That sentence only has power if a thorough, expert-led pen testing engagement is backing it up. This is where auditors separate the pros from the amateurs. Automated scanners are fast but have blind spots. They miss the business logic flaws and creative attack chains that real hackers exploit.
Our OSCP, CEH, and CREST certified pentesters are trained to think like those attackers. We go beyond what scanners can do, using a hands-on, manual pentesting approach to find the subtle vulnerabilities that lead to major breaches. This is the only way to get the validation needed for a risk assessment that stands up to an auditor's scrutiny.
In regulated industries like healthcare or finance, the link between pentesting and attestation is a requirement. For HIPAA, an MSP must ensure the infrastructure handling protected health information (PHI) is secure. Attestations are the final word, but they're built on rigorous pentesting. For a deeper dive into the audit process, you can find more information about the specific regulations around uses and disclosures of protected health information. And when you're talking about compliance, understanding topics like HIPAA compliance for email is crucial for identifying where protections are needed most.
This is where we come in for our MSP, vCISO, and GRC partners. Your clients depend on you for complex audits for SOC 2, PCI DSS, and ISO 27001. Our job is to be your dedicated, channel-only partner, giving you the evidence to make that happen. We deliver fast, affordable reports that are clear, actionable proof you can use to build an attestation statement that builds real trust.
Essential Elements Of A Strong Attestation Statement
A solid attestation statement is your client's proof of security. For MSPs and vCISOs, knowing what makes it hold up under scrutiny is what separates you from the competition. A weak attestation will get torn apart by an auditor, but a well-built one is proof you’ve done your due diligence.
Think of it like building a legal case. You can't just say, "Trust me, we're secure." You need specific claims, hard evidence, and an expert to back it up. A proper attestation statement pulls all those elements together to tell a convincing story about your client's security.
First, a credible attestation statement must define what was tested. Be precise about the "subject matter," whether that’s a public network, a specific web app, or cloud assets. This "scope" section must answer questions like what was tested and what was not. Getting this right protects you and your client. As a reseller, our detailed penetration testing reports give you this information, making it simple to define the scope.
Next, the statement has to lay out the "criteria" for the assessment, like the NIST Cybersecurity Framework or the OWASP Top 10. Once the rules are clear, the "responsible party's assertion" comes next. This is where your client's management states that their security controls are effective. Finally, the practitioner—the auditor or pentester—gives their conclusion. This is the expert opinion that turns your client's claim into a verified fact.
This is where we make you look good. As a channel-only partner, our manual pentesting services, conducted by OSCP, CEH, and CREST certified pros, produce the undeniable evidence you need. We deliver a fast, affordable, and thorough penetration test that gives you a report to build a bulletproof attestation statement, cementing your position as your client’s trusted GRC guide.
Using White Label Pentesting To Bolster Your Brand

For an MSP, vCISO, or GRC firm, your brand is built on trust. White label pentesting lets you offer high-quality, manual penetration testing under your own name, so you look like the full-service security partner you are.
Instead of sending your client to another company for a critical pen test—and risking that vendor poaching them—you deliver the solution yourself. You own the relationship from start to finish. Our white label pentesting service was built for this. We stay completely behind the scenes, so your client only ever sees you as the hero.
How White Labeling Fixes Industry Problems
The security testing industry has problems like inflated prices, long lead times, and poor testing methods. We built our model to fix this. Our affordable, manual-first approach means you get a real penetration test without the sticker shock or the long delays.
Here’s how our white-label service solves these headaches for you as a reseller:
- Affordability: We provide pentesting at a price that works for a reseller model, leaving room for you to build in healthy margins.
- Speed: Forget waiting weeks for a report. Our certified pros deliver detailed reports in under a week, so you can get that attestation into your client's hands.
- Quality: Our reports come from OSCP, CEH, and CREST certified experts doing real manual pentesting. This provides the evidence you need for a rock-solid attestation statement.
A successful penetration test with a clean, professional report is a powerful sales tool. When you hand your client a clean report and help them write an attestation statement, you’re delivering tangible proof of security. Your clients chasing SOC 2, HIPAA, and PCI DSS compliance see that you have their backs. You become essential. By offering a white label pentesting service, you’re turning a compliance headache into a strategic advantage. You deliver peace of mind, all under your own brand.
Our model lets you expand your services and boost your revenue. We handle the expert testing and reporting you need for a credible risk assessment and attestation statement. You deliver the results and own the client relationship. For a deeper look at the benefits, you can learn more about white label penetration testing in our article.
Common Attestation Mistakes and How to Avoid Them
An attestation statement can be a huge asset for your client, but getting it wrong is a compliance nightmare. A bad attestation can give a false sense of security that shatters the second an auditor starts asking hard questions. Your credibility with your client could be damaged.
These mistakes almost always happen when corners are cut. Let's walk through the common pitfalls so you can guide your clients and prove you're the long-term partner they need. The biggest mistake we see is using vague, imprecise language. Auditors have no patience for phrases like "the system is secure" or "all risks have been mitigated." These are empty claims without specific, verifiable proof.
A solid attestation statement needs details. It must define the exact scope of the assessment, name the framework used (like the NIST Cybersecurity Framework), and give a clear summary of what was found. Another classic mistake is claiming a system is "100% secure" or "unhackable." Any security pro knows that's impossible. Every system has some level of risk. Making such claims destroys credibility. The point of a risk assessment and its attestation is to show due diligence, not perfection.
An attestation statement is only as good as the proof behind it. Just running an automated vulnerability scan and calling it a day is a rookie mistake. Scanners provide weak evidence for a real attestation. Auditors know automated tools are blind to complex business logic flaws and can't mimic the creativity of a human attacker. That's why manual pentesting is essential for serious compliance.
A thorough, hands-on pen test from certified experts delivers the rock-solid evidence you need to back up attestations for frameworks like SOC 2, HIPAA, and PCI DSS. As your channel-only partner, this is exactly what we provide. Our OSCP and CREST certified team delivers the proof you need to build an attestation that holds up under pressure.
Your Questions on Attestation Statements Answered
As an MSP or vCISO, you need straight answers about attestation statements to give your clients confidence. Here are the answers to the most common questions we hear from our partners.
Who Signs An Attestation Statement?
Think of it as a two-person job. The first signature comes from your client’s management—the “responsible party.” They formally state that their security controls are in place. The second signature is from the independent auditor or pentester—the “practitioner.” That’s where we step in. Our role is to provide the expert, third-party validation that turns your client’s claim into a verified fact. Our detailed penetration testing reports, built by pros with OSCP, CEH, and CREST certifications, deliver the hard evidence needed for an auditor to sign.
How Long Is A Penetration Test Attestation Valid?
There’s no universal expiration date. It depends on the compliance framework and how often the client's environment changes. For PCI DSS, you’re looking at an annual pentest requirement. For SOC 2 or HIPAA, an attestation statement is more of a point-in-time assessment. A good rule of thumb is that an attestation is valid until something major changes. If your client overhauls their network or pushes a new application live, you need a new penetration test and a new attestation.
Can I Use An Automated Scan For An Attestation?
You can, but you really shouldn't. It's a risky move. Automated scanners are fine for spotting common issues, but they are weak evidence for a formal attestation statement. Auditors know these tools miss the complex, business-logic vulnerabilities that lead to the worst breaches. Trying to get by with just a scan report often falls flat for rigorous frameworks like SOC 2 or ISO 27001. Manual pentesting is the gold standard because it provides the deep, human-led analysis required for a credible attestation.
What Is The Difference Between An Attestation And A Certification?
It's a matter of scope. An attestation is a specific conclusion about a point-in-time assessment, like a pen test. It’s a signed statement saying, "We checked this system on this date, and here is what we found." A certification is a much broader validation of an entire program against a recognized standard, usually valid for a set period like one or three years. Our penetration testing report backs up an attestation statement, which then becomes critical evidence to help your client achieve their larger goal, like an ISO 27001 certification.
Ready to provide your clients with the credible evidence they need for their next audit? The team at MSP Pentesting is your dedicated, channel-only partner for fast, affordable, and manual pentesting services.
Contact us today to learn more about our white label pentesting services.



.avif)
.png)
.png)
.png)

