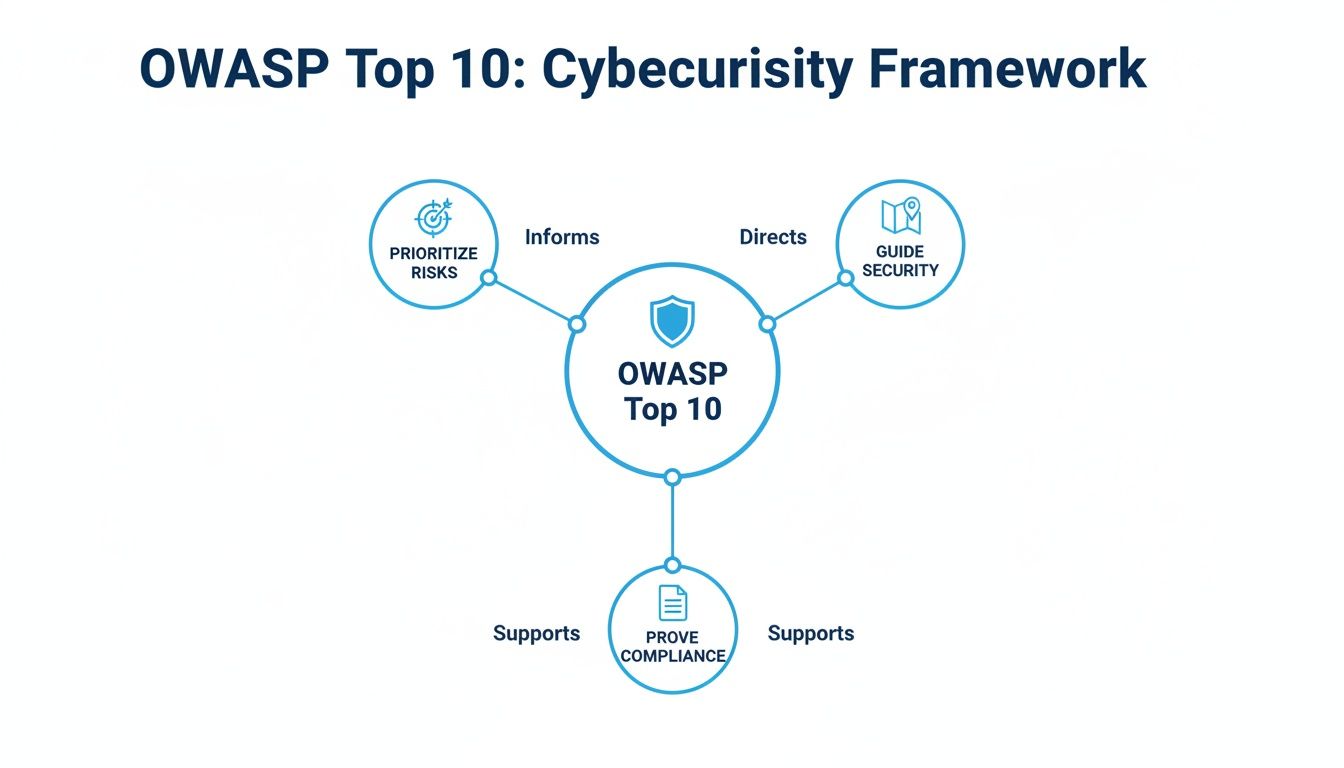
The OWASP Top 10 is the security world’s most-wanted list for web application vulnerabilities. For Managed Service Providers (MSPs) and vCISOs, it’s a clear roadmap for protecting your clients from the attacks that are happening right now. Think of it as the ultimate cheat sheet for application security. This guide explains what the OWASP Top 10 is and why it matters for your clients’ compliance and security.
What Is The OWASP Top 10 List?
Imagine you’re building a fortress. Instead of guessing where to put your guards, an intelligence report tells you the top ten ways invaders try to break in. That's exactly what the OWASP Top 10 is for web applications. It's a globally recognized standard that helps you focus your defenses where they’ll have the biggest impact.
Understanding these risks is critical for hitting compliance goals like SOC 2, HIPAA, and PCI DSS. Auditors want proof that you're actively managing these specific vulnerabilities. An OWASP-aligned penetration testing report from our certified team is the hard evidence they need to see. Our pentesters hold top certifications like OSCP, CEH, and CREST.
The OWASP Top 10 isn’t a law. It’s a consensus list of the ten most critical web application security risks, updated every few years. For example, the 2021 update pushed Broken Access Control to the #1 spot after it was found in a staggering 94% of tested applications. This shows you how common even basic flaws are.
As a trusted MSP or vCISO, this framework helps you have smarter security conversations with clients. Instead of talking about abstract threats, you can point to a global standard and explain the real dangers. This gives you a solid business case for recommending services like our affordable and fast manual pentesting.
How the Top Three OWASP Risks Affect Your Clients
To help you and your clients quickly understand what matters most, here's a quick look at the top three risks. These examples show why they are so critical to address for both security and compliance.
This table just scratches the surface, but it highlights how these aren't just theoretical problems. They have direct, painful consequences for your clients' businesses. The OWASP list is the foundation of any credible web application penetration testing engagement.
We deliver affordable, fast, and thorough white-label pentesting so you can provide these essential security services to your clients. You won't have the overhead of building an in-house team. Our channel-only model means we never compete with our MSP partners.
Explaining the Top Five OWASP Vulnerabilities
Let’s translate the top five risks into clear scenarios you can easily walk your clients through. Our certified OSCP, CEH, and CREST pentesters are experts at finding these flaws through hands-on, manual pentesting. This is how you get a risk assessment with real depth, something an automated tool will never give you.
A01 Broken Access Control
Broken Access Control is holding the top spot for a reason. Think of it like a hotel key card that mysteriously opens every single room. In the digital world, this means a user can see or do things they absolutely should not have permission for. A low-level employee might be able to simply change a user ID in the web address and suddenly get full admin access.
A02 Cryptographic Failures
This one is all about keeping secrets. Cryptographic Failures happen when sensitive data like passwords or credit card numbers are sent in the clear. Proper encryption scrambles this information, turning it into a secret code. Imagine a client's e-commerce site stores all its customer passwords in plain text. A breach would be a disaster.
This is exactly why the OWASP framework was created—to help prioritize these kinds of risks and prove compliance.
A03 Injection
Injection is like tricking a vending machine into giving you free snacks by feeding it a counterfeit coin. An attacker "injects" malicious commands into an application, fooling it into doing something it was never designed to do. A classic example is SQL Injection, where an attacker types a malicious command into a website's search bar to dump the database. You can learn more in our guide on how to test for SQL Injection.
A04 Insecure Design
Insecure Design is a newer category, but it gets to the heart of a huge problem: building security in from the start. It’s like building a house without thinking about where the locks go until after it’s finished. A real-world example is a "forgot password" feature that emails a user's old password back to them in plain text. The feature works, but the design is fundamentally insecure.
A05 Security Misconfiguration
This is one of the most common risks we find and is basically the digital equivalent of leaving the front door wide open. Security Misconfiguration happens when security settings are left on their easily guessable defaults. A perfect example is an admin forgetting to change the default password from "admin" on a new server. Our affordable and fast pentesting services focus heavily on finding these simple but critical errors.
Understanding Other Critical Security Risks
The OWASP Top 10 has more threats lurking just below the surface. The rest of this list covers risks that are just as damaging but often missed by automated scanners. This is why a real, hands-on penetration testing engagement from a certified expert is non-negotiable for your clients.
Our OSCP, CEH, and CREST certified pentesters don’t just run down a checklist. They think like attackers to root out hidden flaws. This manual approach delivers a true risk assessment that keeps clients safe and satisfies auditors for frameworks like SOC 2 and ISO 27001.
A06 Vulnerable and Outdated Components
This one is a massive headache for every MSP and vCISO. It’s like building a fortress with state-of-the-art walls and then using rusty, off-the-shelf locks. These "locks" are the third-party software and libraries developers use to build apps faster. If just one of those components has a known flaw, the whole application is now vulnerable.
Breaches often map directly back to these OWASP categories. A review of major data breaches found that many were caused by using components with known vulnerabilities, injection flaws, and broken authentication. This is how OWASP flaws lead to massive data breaches and eye-watering fines.
This is where our manual pentesting really shines. Our experts dig deeper to find vulnerabilities buried deep in the software stack.
A07 Identification and Authentication Failures
This is all about one simple question: are you really who you say you are? Think of it like a lazy security guard who waves someone into a secure building without actually checking their ID. These failures let attackers impersonate legitimate users, including administrators. This can happen when an application allows terrible passwords like "Password123!" or fails to stop brute-force attacks.
For compliance, this is a huge deal, especially for regulations like HIPAA and PCI DSS that have strict rules about authentication.
A08 Software and Data Integrity Failures
This is a newer category that addresses a critical modern risk: blindly trusting software without checking if it’s been tampered with. Imagine you download a software update you think is from a trusted vendor, but an attacker secretly swapped it with a malicious version. This can happen if an attacker sneaks malicious code into an automated software deployment pipeline.
A09 Security Logging and Monitoring Failures
This is the digital equivalent of installing a top-of-the-line alarm system and then forgetting to plug it in. Failures in logging and monitoring happen when an organization doesn’t record or review security events. Without good logs, you have no idea if you're under attack, how an attacker got in, or what they did once they were inside. For any GRC professional, having no logs during a breach is a nightmare.
A10 Server-Side Request Forgery (SSRF)
Server-Side Request Forgery, or SSRF, is a sneaky but powerful attack. It's like tricking a company's mail clerk into sending a malicious package to another department for you. An attacker finds a flaw in a web server and forces it to make requests to internal systems that are normally firewalled off. Uncovering these kinds of flaws requires creative, manual testing—exactly what defines our affordable and fast penetration testing services, built for the reseller channel.
How OWASP Top 10 Drives Client Compliance
For your clients, the OWASP Top 10 isn't just a technical list—it's a list of real threats that can derail their business. This is where you, as their trusted MSP or vCISO, can connect the dots between security and strategy. A penetration testing report built around the OWASP framework is the hard evidence auditors for frameworks like SOC 2, HIPAA, PCI DSS, and ISO 27001 demand.
When an auditor walks in, they want proof that application security is being actively managed. Handing them a report from one of our OSCP, CEH, or CREST certified pentesters shows you’ve done your homework. It proves you've systematically hunted for the industry’s most critical risks.

Offering penetration testing strengthens your Governance, Risk, and Compliance (GRC) offerings and makes you an essential partner. This proactive approach turns security from a cost center into a business enabler. You're not just fixing problems; you're helping clients hit their strategic goals. Weaving the OWASP Top 10 into a broader organizational cybersecurity framework is key to better protection.
Addressing the OWASP Top 10 is a direct line to satisfying major compliance requirements. The table below shows how tackling these common risks provides the tangible evidence auditors need.
A single pentest report can knock out evidence requirements across multiple frameworks, making it an incredibly efficient tool for any GRC program. Automated scanners find the easy stuff, but they will never satisfy a sharp auditor. Auditors want to see proof of a thorough risk assessment, which requires a human brain. Our manual pentesting process delivers exactly that.
The detailed report you get from us is the indisputable proof your clients need. You can get the full rundown in our guide to SOC 2 penetration testing. By partnering with us for affordable, fast, and white-label pentesting, you deliver this critical value under your own brand.
Offer Pentesting Services Without The High Overhead
Building an in-house penetration testing team is a massive, expensive headache. You have to hire and retain talent with specialized certifications like OSCP, CEH, and CREST. The overhead for salaries and tools can easily spiral into hundreds of thousands of dollars. For most MSPs and vCISOs, it's just not practical.
This is the exact problem we built our business to solve. We're a strictly channel-only partner, which means we exist to support you, the reseller. We will never compete with you. Our model is designed to let you offer high-demand pentesting services without the operational drag or the high costs.
The managed service and GRC world has been stuck with the same problems for years: sky-high prices, long waits for reports, and testing that is little more than an automated scan. We saw this gap and built a service specifically for partners like you.
Our approach is simple and direct:
- Affordable: We provide cost-effective manual pentesting that lets you keep healthy margins.
- Fast: Our process is streamlined to get you detailed, actionable findings quickly to meet tight compliance deadlines.
- Manual and Thorough: Our certified experts go beyond what automated scanners can find to uncover complex flaws.
Our white label pentesting program is designed to be simple. You sell the service under your own brand, and our team does the work behind the scenes. To your clients, you’re the security expert providing a critical service. You get to add a high-demand revenue stream without the operational burden.
To remediate the OWASP Top 10, you need regular assessments, including a thorough vulnerability assessment and penetration testing. By partnering with us, you can deliver this crucial service and help your clients meet compliance requirements with confidence. It’s a model that empowers you to scale your security offerings instantly. Adding pentesting to your portfolio deepens client trust and boosts retention.
Let's Build Your Pentesting Practice Together
The OWASP Top 10 isn't just a list—it's the industry standard for application security and a core piece of most compliance frameworks. For MSPs and vCISOs looking to add these crucial services, MSP Pentesting offers the simplest, most affordable way to get started. Our model was built to solve the problems that hold partners back by providing a solution that is affordable, manual, and fast.
Our team is stacked with certified OSCP, CEH, and CREST pentesters. That expertise, combined with our rapid reporting and in-depth manual pentesting methodology, sets you and your clients up for success. We find the critical vulnerabilities that automated scanners always miss, giving you the hard evidence needed for any risk assessment or audit.
We’re a channel-only company. Your growth is our only goal. We will never compete with you for business. Think of us as a seamless, expert extension of your own team, delivering the white label pentesting services that make your security offerings stronger and build real trust with your clients. Let us worry about the technical heavy lifting so you can focus on the client relationship.
Ready to grow your security practice? Contact us today to learn more about our reseller program and see how we can help your business win.
Your Top Questions About The OWASP Top 10
We talk to MSPs, vCISOs, and GRC pros every day, and a lot of the same questions about the OWASP Top 10 come up. Here are the straight answers to the most common ones we hear.
How Often Is an OWASP Pentest Needed for Compliance?
For most frameworks like SOC 2 or HIPAA, the simple answer is at least once a year. But that's the bare minimum. You should also be testing after any major application change—like a new feature launch. This keeps your client's risk assessment fresh and accurate. Our affordable, fast testing makes it painless to stick to this schedule.
What is the Difference Between a Scan and a Manual Pentest?
This one is critical. An automated scanner is like a spell-checker that catches the obvious, low-hanging fruit. Manual pentesting from one of our certified OSCP, CEH, and CREST experts is like having a seasoned editor review a document. They analyze context, question logic, and find the subtle, complex flaws a machine would miss.
How Do I Explain the Value of Pentesting to My Clients?
The best way is to tie it directly to what they care about: passing audits and building trust. A penetration testing report isn't just a technical checklist; it's the proof they need to satisfy auditors for SOC 2, HIPAA, or PCI DSS. You can say, "Think of an OWASP-focused pentest as a fire inspection for your digital business. It finds the hazards before they burn you down and proves to regulators you’re operating safely."
What Does a Typical Pentesting Engagement Look Like?
We designed our entire process around our reseller partners to be simple and fast. It starts with a quick scoping call. From there, our team gets to work hunting for vulnerabilities. The final step is a comprehensive, white-label report you can put your own logo on, filled with clear findings and practical steps for remediation.
Ready to add affordable, expert pentesting to your security offerings? The team at MSP Pentesting is here to help you grow. Learn more about our channel-only partnership at https://msppentesting.com.



.avif)
.png)
.png)
.png)

