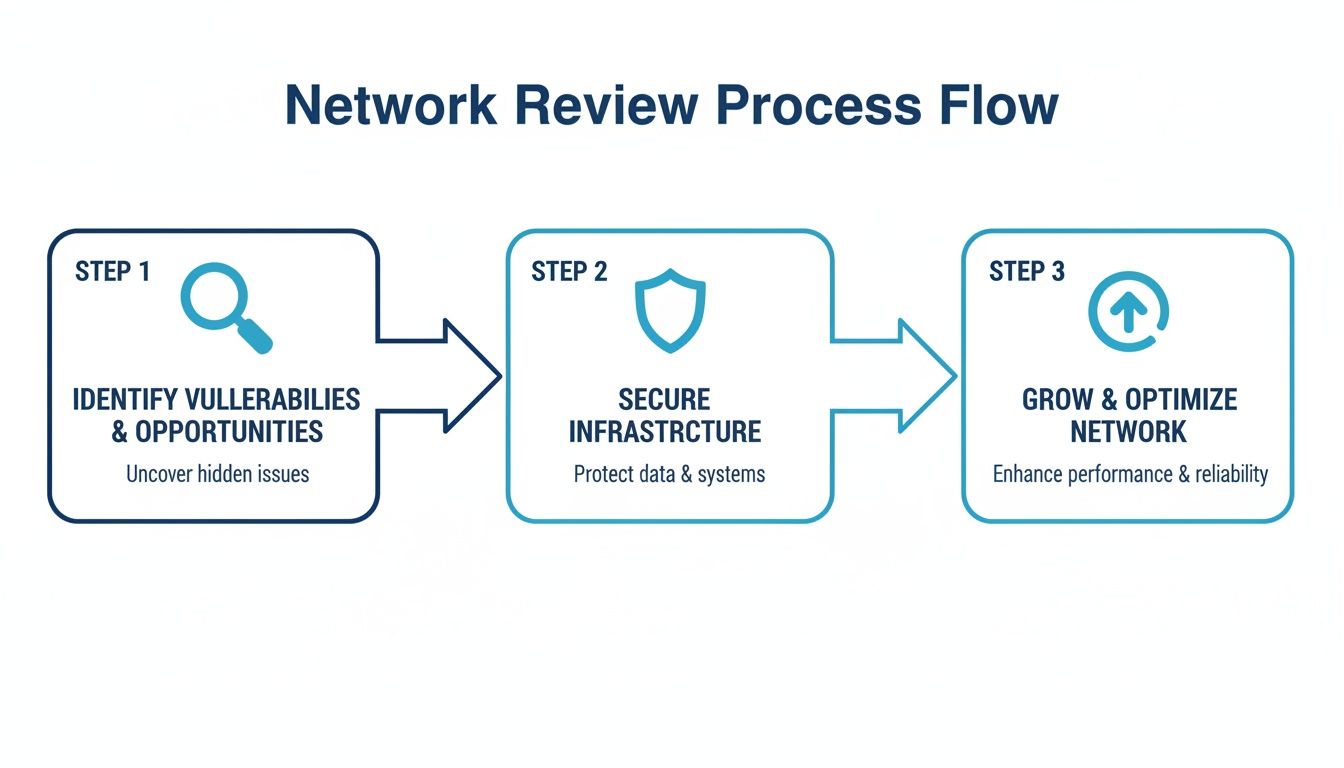
A network architecture review isn't just a technical check-up. For MSPs, vCISOs, and GRC companies, it's a critical strategy for protecting clients and landing bigger deals. In today's messy IT environments, a single hidden vulnerability in the network design can lead to a devastating breach. This process is how you find those weak spots before an attacker does, turning a potential disaster into an opportunity to build client trust.
Why A Network Architecture Review Is Non-Negotiable
If you're an MSP, thinking about network security has to go way beyond firewalls and antivirus. You need to understand the blueprint of your client’s entire digital operation. A proper network architecture review dives deep into how data flows, where it’s stored, and who can get their hands on it. This isn't just a "nice-to-have" anymore; it's a business necessity.
A solid review helps you answer the tough questions that keep clients safe and compliant. Is their network properly segmented to stop an attacker from moving laterally? Are their cloud configs actually secure, or just left on default? Are there old, forgotten access points creating a backdoor for threats? Finding these issues before an incident is what separates a reactive IT provider from a trusted security partner.
Many of your clients are scrambling to meet strict compliance standards like SOC 2, HIPAA, or PCI DSS. A network architecture review is step one for all of them. It provides the hard evidence and documentation they need to prove security controls aren't just in place, but are actually working.
By adding a penetration test into the mix, you give them tangible proof. Our white label pentesting services let you offer this advanced validation under your own brand. Our OSCP, CEH, and CREST certified pros conduct manual pentesting to find the vulnerabilities automated scanners always miss.
The Reseller Advantage With Our Pentesting Services
As a reseller, you need a partner who has your back, not one who's trying to poach your clients. We're a channel-only company. Our entire mission is to give you affordable, fast, and effective penetration testing services that you can slide right into your existing offerings.
We help you skip the sky-high costs and ridiculous wait times of traditional pentesting firms. You get expert, manual pen test results fast, proving your value and securing client environments without the headache of building your own team. This approach doesn't just make clients safer; it opens up new revenue streams.
You can use the findings from a pen test to justify new security projects, upsell managed services, and cement your role as their go-to advisor. For a deeper dive, check out our guide on assessing network security.
A network architecture review backed by a professional pen testing engagement is a game-changer for client retention and growth. It shifts the conversation from tech specs to business risk, showing clients you're proactively protecting their most valuable assets.
How We Scope The Review And Map Client Assets
Before you start poking around a client's network, you have to know what you're actually looking at. The first real step in any network architecture review is defining the scope and mapping every single asset. It’s like drawing a map of a city before you decide which streets need repairs. Without a complete map, you're just guessing.
This process sets clear boundaries for the engagement. Is this a general security checkup, or is the client focused on a specific compliance framework like ISO 27001 or SOC 2? The answer completely changes what’s in-scope, which is critical for managing expectations. It's the difference between a broad risk assessment and a targeted penetration testing engagement.
For an MSP or vCISO, getting the scope right is everything. It stops scope creep in its tracks and ensures you’re testing the systems that actually matter to the business. Start by asking some basic questions. What are the crown jewels? What data, if stolen, would crater the company? The answers immediately help you prioritize the review on high-impact areas.
Once the boundaries are set, it’s time to catalog everything inside them. A good asset inventory isn’t just a spreadsheet; it’s a living document of every single device and application on the network. We're talking physical servers, VMs, endpoints, cloud instances, and mobile devices. If it has an IP address, it belongs on the list.
A solid, manual pentesting effort always starts with this inventory. While automated tools find a lot, an experienced pentester doing a manual review almost always uncovers forgotten devices or shadow IT that scanners completely miss. Our approach puts human expertise first to make sure nothing slips through the cracks.
Relying only on automated scanners for asset discovery is a classic mistake. Sure, they're fast, but they lack context and can easily miss devices that don’t respond to standard probes. This is why our OSCP, CEH, and CREST certified pentesters always combine automation with hands-on manual techniques.
A thorough inventory is the bedrock for everything that comes next, like threat modeling and segmentation validation. For a GRC company or reseller, offering a service with this level of detail shows you’re delivering real value. This is the quality of work you get when you partner with us for white label pentesting.
Conducting Threat Modeling And Segmentation Validation
You've got a full map of the client's assets. Now it’s time to think like an attacker. This is what threat modeling is all about. Ask a simple question: "If I wanted to break this network, how would I do it?" This mindset helps you pinpoint real-world threats that apply directly to your client's architecture.
This practical approach to a risk assessment is how an MSP or vCISO provides genuine value. You look at each critical asset—a public-facing web server versus an internal database server—and imagine the different angles of attack. Their threats aren't the same, and your security strategy has to reflect that.

Thinking like an attacker naturally leads you to segmentation validation. Your client might have firewalls and VLANs, but are they actually working? The whole point of segmentation is to stop an intruder from moving across the entire network after compromising just one machine. A proper pen test is the only way to get a real "yes" or "no" answer.
For any MSP dealing with compliance mandates like PCI DSS or HIPAA, proving segmentation isn't just a good idea—it's mandatory. In today’s environments, don't forget to include a review of Kubernetes security best practices to make sure those containerized workloads are locked down tight.
This is where our white label pentesting service becomes your secret weapon. An automated scanner can't tell you if your segmentation strategy will hold up against a skilled human attacker. Our CREST, OSCP, and CEH certified pentesters can. We perform manual pentesting to actively try and break the controls you have in place.
We then deliver a clear, no-fluff report—fast—that shows you exactly where the gaps are. A penetration test is the only way to truly validate that your network segmentation is effective. It moves the discussion from "we think it's secure" to "we've proven it's secure," which is a conversation that builds immense client trust.
Offering this level of validation is a game-changer for any reseller. You don't need to hire your own expensive in-house talent. We're a channel-only partner. We provide affordable, fast, and thorough pen testing services you can sell under your own brand. You can read more in our article on network segmentation best practices.
Verifying Network Security Controls And Configurations
Once you've mapped the assets and threats, it's time to actually look at the security controls. A proper network architecture review lives or dies by how well you verify the tools meant to protect the client. This isn't just about checking if a firewall is turned on; it's about digging into the rules, policies, and configs that make or break the network's defenses.
Automated scanners are fine for catching the obvious stuff, but they completely miss the nuanced misconfigurations that a real attacker would exploit. This is where our hands-on, manual pentesting approach, led by OSCP, CEH, and CREST certified experts, makes all the difference. We find the subtle gaps that lead to a breach, and we do it fast and at a price point that makes sense.
Firewalls and Network Access Control (NAC) are the bouncers for the network. Your job is to make sure they aren't letting the wrong people or traffic sneak past. You'd be shocked how often we find outdated, way-to-permissive, or even conflicting rules that render them useless. For firewalls, "any/any" rules are a massive red flag.
With remote work being the norm, the VPN is the new front door for most companies. One bad VPN configuration can expose the entire internal network. Your review needs to scrutinize the encryption standards and check who has access. Are former employees still lingering in the VPN user group? These are exactly the kind of critical-but-overlooked findings our penetration testing services are built to uncover.
A comprehensive network architecture review naturally includes an assessment of overall security in networking to identify vulnerabilities. You're not just checking boxes for compliance; you're building a defense that works in the real world.
Cloud environments like AWS and Azure have their own digital gatekeepers, mainly Security Groups and Network ACLs. These are misconfigured all the time. One of the most common mistakes is leaving management ports like RDP or SSH open to the entire internet (0.0.0.0/0). Your review has to validate that these rules are locked down to specific, known IP addresses.
As a reseller, you can offer this expert-level validation under your own brand. Our white label pentesting service gives you the deep-dive analysis your clients need to secure their complex networks. We do the heavy lifting, and you deliver a powerful report that cements your status as a trusted security partner.
Reporting Findings And Prioritizing Remediation
Finding vulnerabilities is only half the battle. A truly great network architecture review delivers a report your client can actually understand and use. This is where you turn all that technical digging into a clear, business-focused plan that makes you look like the expert you are. For an MSP or vCISO, a powerful report is your best sales tool.
Your client's CEO probably doesn't care about an outdated protocol version. What they do care about is how that vulnerability could lead to a data breach. Your report has to translate technical risk into business impact. Instead of saying, "Cross-Site Scripting found on web app," explain why it matters. For example: "A flaw in your customer portal could allow an attacker to steal user credentials, leading to potential HIPAA violations."
This is where our service shines. We provide white label pentesting reports designed for you, the reseller. They’re clear, concise, and written to make you look good. We handle the complex penetration testing, and you deliver a polished, professional report under your own brand.
Our reports cut right to the chase: an executive summary, prioritized findings, and actionable remediation steps. This approach saves you a ton of time and reinforces your value. You’re not just a vendor; you're a strategic partner guiding them through the complex world of cybersecurity and compliance.
Not all vulnerabilities are created equal. A critical flaw on an internal server is far less urgent than a medium-level one on a public-facing payment portal. Your remediation plan has to prioritize fixes based on real-world exploitability and business impact. This is crucial for any GRC company trying to navigate SOC 2 or ISO 27001 requirements.
Our manual pentesting process, conducted by OSCP, CEH, and CREST certified experts, is built around this exact philosophy. We don't just find vulnerabilities; we assess their real-world impact on your client's specific environment. That gives you the context you need to build a smart, effective remediation plan.
As a channel-only partner, our success is tied to yours. We provide the affordable, fast, and thorough pen test results that empower you to secure your clients and grow your revenue.
How To Partner With A White Label Pentesting Firm
Finishing a deep-dive network architecture review is a huge win, but what comes next is what really matters. For MSPs, vCISOs, and GRC firms, the real struggle isn't just spotting vulnerabilities—it's delivering high-end security validation without the ridiculous price tags or month-long waits. That's where a smart partnership completely changes the game.
You don't have to build your own pentesting team from the ground up. The overhead for salaries, training, and certifications is a nightmare. Instead, you can team up with a specialist who works as an extension of your crew, giving you the firepower you need to close deals.
This is the most important thing to know about us: we are a channel-only company. We will never, ever compete with you for your clients. Our entire business is designed to make you look like the hero. This means you can bring our expert penetration testing services to any client meeting with total confidence.
Our pentesters are where the real value is. They have the top-tier certs like OSCP, CEH, and CREST, but it's their hands-on, manual approach that makes all the difference. A skilled human expert finds the complex, business-critical flaws that actually lead to major breaches. This focus on manual pentesting means you get a truly thorough risk assessment.
The traditional pen test industry is broken. It's full of inflated prices and painfully slow turnaround times. We built our model to be affordable and fast, with most reports landing in your inbox within a week. This speed means you can weave penetration testing into your regular service offerings for compliance frameworks like PCI DSS and ISO 27001.
By offering our white label pentesting services, you can expand your service catalog, make clients stickier, and drive new revenue. We handle the heavy lifting of a penetration test so you can focus on what you do best: building great relationships with your clients. To see how we can help you grow, learn more about our pentest partner program.
Ready to deliver expert security services under your own brand? MSP Pentesting is your channel-only partner for affordable, manual penetration testing that helps you win. Contact us today to learn how our white-label pentesting can help you grow at https://msppentesting.com.


.png)
%202.png)

.avif)
.png)
.png)
.png)

