A real network security assessment is more than a quick nmap or ai powered scan. It’s a deep, hands-on dive to test a client's defenses using the same tricks attackers use. For any MSP, a proper network penetration test is the best way to find hidden gaps before the bad guys do, keeping your clients compliant and showing your value.
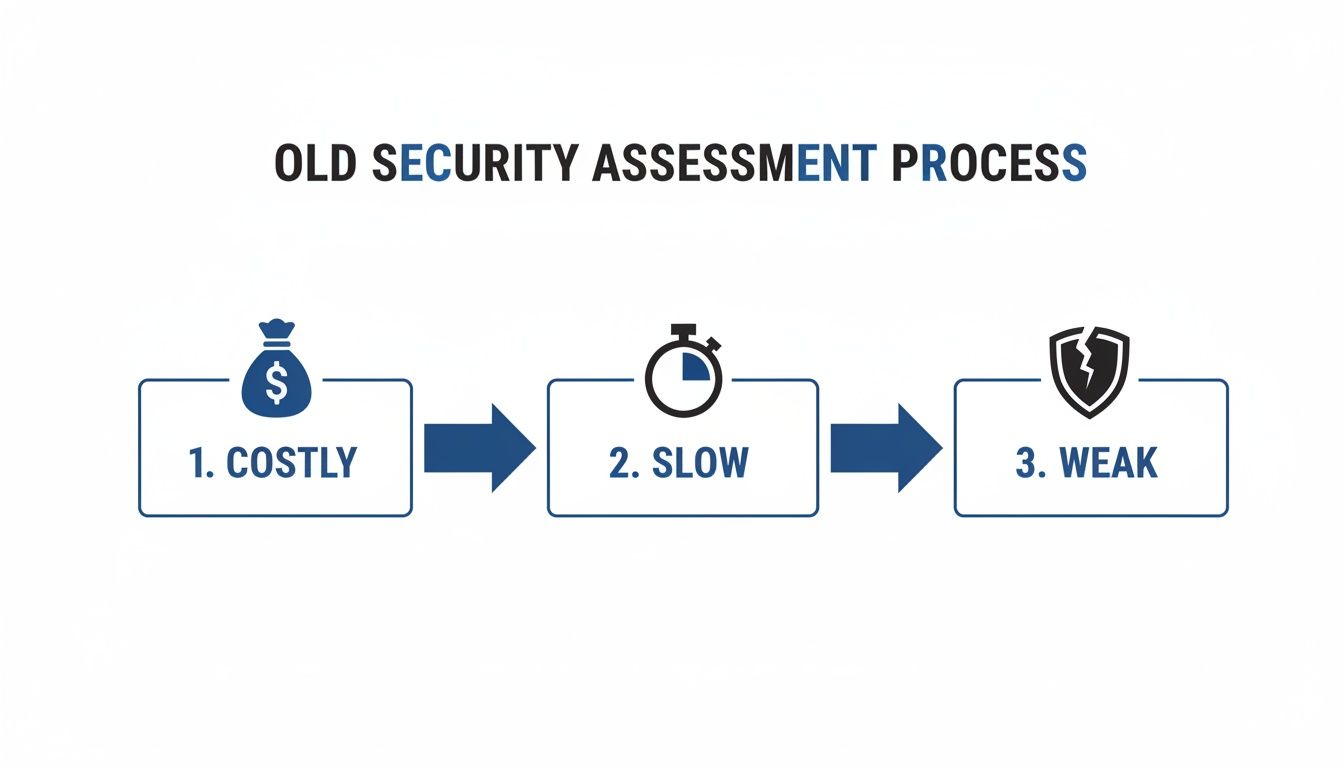
Why Traditional Network Security Assessments Fail
Your clients face threats that get smarter every day. But many MSPs and IT resellers are stuck with old-school penetration testing partners who just don't get it. They promise a thorough risk assessment but deliver slow, overpriced, and automated reports that barely scratch the surface.
That old model is broken. Most pentesting firms were built for huge companies, not MSPs. This leaves you and your clients with two bad choices: pay a fortune for a pen test or settle for a cheap scan that misses dangerous vulnerabilities. Either way, you're in a tough spot.
The High Cost of Slow and Ineffective Pen Testing
The old way of assessing network security is painfully slow and expensive. It's common for an MSP to wait weeks just to get a report back. That delay is a deal-breaker when your client is on a tight deadline for SOC 2 or HIPAA compliance.
On top of that, the pricing is often inflated. Inefficient processes mean high overhead costs, and you end up paying for it. You're forced to either absorb the cost or pass an uncompetitive price to your client, risking the entire relationship. This slow approach ignores modern threats. You can dig into the global data breach trends to see just how bad it has become.
Over-Reliance on Automation Misses Human-Centric Flaws
Here's another issue: the old model relies heavily on automated scanners. Automated scanners find low level findings, but they are blind to business logic flaws and complex issues a real attacker would exploit. A simple scan can't think creatively or chain together a few low-risk findings to create a huge breach.
This is where manual pentesting from a certified pro makes all the difference. Our affordable and fast pentesters hold certifications like OSCP, CEH, and CREST. This proves they know how to think like an attacker. They go beyond the automated checklist to find the vulnerabilities that actually lead to breaches, giving your clients a true picture of their security.
A Broken Partner Model That Creates Competition
The biggest problem for any reseller is partnering with a firm that might steal your client. Many security companies will take your referral, then try to sell their own managed services directly to your client. That’s not a partnership; it’s a conflict of interest.
We are a channel-only partner, meaning we are 100% committed to your success. We provide white label pentesting, so our team works under your brand. We never talk to your clients and we never compete with you. Our goal is simple: deliver affordable, fast, and thorough penetration testing that helps you secure client relationships and grow your business.
Understanding a Manual-First Penetration Test
A real penetration test isn't just pushing a button on a scanner. It’s a hands-on process by a human expert who thinks and acts just like a real-world attacker. For MSPs, explaining this process shows your value. It proves you're not just checking a box for compliance frameworks like SOC 2 or HIPAA; you're providing a genuine risk assessment.
Think of it like this: an automated scanner is a security guard with a checklist. A manual pentester is the detective who jiggles every door handle, peeks in windows, and tries to talk an employee into letting them inside. One is a simple check; the other is a true test of defenses.
Finding Security Flaws Only a Human Can
The biggest issue with automated tools is they lack creativity. They can't understand business logic or combine small vulnerabilities to create a disaster. That's where a certified pentester comes in.
Our team holds top-tier certifications like OSCP, CEH, and CREST. These aren't just acronyms; they represent thousands of hours of training. Our experts find critical flaws scanners always miss, like business logic errors or chained exploits. These are the attacks that lead to major data breaches, and only a manual penetration test can find them before it’s too late.
Defining the Scope for an Effective Pen Test
Every good pen test starts with a clear scope. This is where we work with you, the reseller, to define the rules of engagement. We figure out what parts of your client's network and apps we can test and what methods we can use.
A well-defined scope keeps the penetration testing safe and effective. It prevents disruption to your client's business while letting our pentesters simulate realistic attacks. This step is also crucial for compliance frameworks like PCI DSS and ISO 27001. You can learn more about the specific phases of a penetration test in our article.
Turning Pen Test Findings into Actionable Reports
A penetration test is only as good as its report. For an MSP or vCISO, that document is your final product. It's proof of your expertise and the client's roadmap for getting secure. A confusing, jargon-filled report is useless if the client can't understand it.
Many security providers fail here. They dump a huge technical document on the client that creates more confusion than clarity. The goal isn't to scare them with vulnerabilities; it's to give them a clear, prioritized plan for fixing what matters.

As a reseller, offering a clean, branded white label pentesting report reinforces your value. It shows you’re a strategic partner. The report has to speak to both the technical team that needs to fix things and the executives who need to understand the business risk.
Building a Security Report That Speaks to Everyone
A great report starts with a simple executive summary for the C-suite. It skips the technical details and clearly states the risk level and business impact in plain English. After the summary, you dive into the details, documenting every finding with evidence like screenshots.
A report that just lists problems without offering solutions is a dead end. Every finding must be paired with clear, step-by-step guidance. Our reports, which you can brand as your own, are built to be actionable. Our OSCP, CEH, and CREST certified pentesters don't just find problems; they explain exactly how to fix them.
Mapping Vulnerabilities to Compliance Frameworks
For your clients in the GRC world, a penetration testing report is critical evidence for auditors. It can make or break a compliance audit for frameworks like SOC 2, HIPAA, PCI DSS, and ISO 27001. The key is to map technical findings directly to specific compliance controls.
This connects the dots for everyone. It proves to an auditor that the client is proactively managing risk. An affordable and manual pentesting engagement provides the concrete evidence they need. You can see how to structure these reports by checking out our penetration testing report template guide.
Making the Financial Case for Proactive Pentesting
Business decisions always come down to numbers. When assessing network security, you have to frame it as a smart investment, not just an expense. Pit the cost of being proactive against the massive cost of cleaning up after a breach.
A penetration test is proactive, like changing the oil in your car. Incident response is reactive, like calling a tow truck after the engine blows up. One is a predictable cost; the other is a disaster. The numbers tell a powerful story. You can dig into more of the staggering costs of data breaches on varonis.com.
Positioning Pen Testing as an Insurance Policy
Think of a pen test as a form of insurance. You pay a small, predictable premium now to avoid a catastrophic loss later. Our affordable, fast, and white label pentesting services make this an easy decision for your clients.
A proactive penetration test shifts the conversation from "How much does this cost?" to "How much risk are we willing to accept?" As an MSP or vCISO, this approach solidifies your role as a strategic partner. We give you clear, predictable costs upfront so you can build a strong case. Check out our penetration testing price sheet for MSPs.
How White Label Pentesting Helps MSPs Win
How do you offer expert-level penetration testing without the high salaries and headaches of an in-house team? The answer is a channel-only partnership. A white label pentesting model, built for resellers like you, is the smartest way to scale your security offerings without the overhead.
Our promise is simple: we are your silent, expert partner. We never compete for your clients or speak to them. Our job is to make you look like the security expert.

This partnership lets you expand your services, boost revenue, and solidify client trust without adding overhead. You get all the credit for a top-tier pen test, and we handle the technical work behind the scenes.
Instantly Add Certified Experts to Your Security Team
Building a credible pentesting team is hard and expensive. You have to find, hire, and retain experts with elite certifications. A white label partner lets you skip that entire struggle.
The moment you partner with us, your team includes OSCP, CEH, and CREST certified pentesters. These certifications represent the industry's highest standards. You can confidently tell your clients their network is being assessed by the best in the business. This immediate access to expertise means you can start selling high-margin security services tomorrow.
The Speed and Affordability That Wins Deals
The traditional pentesting industry is slow and overpriced. We built our model to solve this. Our process is designed for speed without sacrificing quality. We deliver comprehensive penetration testing reports in just one week. That rapid turnaround is a game-changer for clients facing tight deadlines for SOC 2 or HIPAA compliance.
Plus, our affordable pricing is built for the channel. We understand you need to maintain healthy margins. Our manual pentesting services are priced to be an easy addition to your offerings, providing immense value without a painful budget discussion for your clients.
Expand Services and Deepen Client Trust
Offering a robust risk assessment service like penetration testing changes your client relationships. You're no longer just "the IT guy"; you become a strategic security advisor. This makes your services stickier and more valuable.
With a white label partnership, you can confidently offer a full suite of security testing services. Every pen test you deliver deepens the trust your clients have in you. Contact us today to see how our white label partnership can help you win.
Common Questions About Network Security Assessments
Clients will have questions about security assessments. You need to have solid answers ready. Here are a few common questions our MSP and vCISO partners hear, so you can lead the conversation with confidence.
Manual Pentesting vs. an Automated Scan?
Think of an automated vulnerability scan like a spell checker. It’s a good first pass that catches obvious mistakes but isn't very smart. Scanners often produce false positives and miss creative vulnerabilities.
Manual pentesting is completely different. It's done by a real person with certifications like OSCP, CEH, and CREST who thinks like an attacker. Our team doesn't just run a tool. They find issues scanners are blind to. It’s the difference between a simple checklist and a true risk assessment.
Does a Penetration Test Meet Compliance Requirements?
Absolutely. A thorough penetration test is either required or highly recommended for nearly every major compliance framework. The final report is the proof you give auditors to show you are protecting sensitive data.
We build our pentesting reports to map directly to these requirements, making your client's audit process much easier for frameworks like SOC 2, HIPAA, PCI DSS, and ISO 27001. When you offer a pen test, you are selling a direct solution to their GRC problems.
How Does the White Label Pentesting Process Work?
Our process is seamless for you. You own the client relationship from start to finish. We act as your expert technical team behind the scenes. It's a simple partnership that works.
You bring us the project, and we handle the hard work. We work with you on scoping, our team performs the manual penetration test, and then we write a detailed report. The final document gets your logo and branding. We hand it back to you, and you present it to your client as your own team's work.
Why Partner With a Channel-Only Provider?
It’s simple: you never have to worry about us competing with you. A channel-only partner's success is directly tied to yours. Our business model is 100% committed to our resellers, so we will never sell directly to your clients.
This model creates a foundation of trust and aligns our goals. We only win when you win. That's why we deliver affordable, fast, and high-quality services. We provide the expert-level penetration testing that helps you grow your business.
Learn more about our channel-only partnership program.


.png)
%202.png)

.avif)
.png)
.png)
.png)

