Think of your client's business like a fortress. You've built the walls and set up the guards. But how do you know if there are any secret tunnels or unlocked gates you missed?
A network penetration test, or pentest, is how you find out. It’s like hiring a team of professional, ethical "burglars" to test your defenses. They simulate a real cyberattack to find vulnerabilities, then give you a clear plan to fix them.
What is Network Penetration Testing?
To understand what a network pentest covers, it helps to start by understanding the distinction between network security and cybersecurity. Cybersecurity is the whole castle, but network security is the walls, gates, and roads. A penetration test is where we check if that security strategy actually works.
This isn’t just running a scanner. A true manual pentest is a hands-on attack where our certified pentesters—holding top certifications like OSCP, CEH, and CREST—act just like real attackers. They don't just find potential weaknesses; they actively try to break them. For any MSP or vCISO, this is the only approach that provides real security value.
Your clients are catching on. The demand for network penetration testing is huge. Offering white label pentesting is no longer a "nice to have"—it's a major growth opportunity for your MSP.
A proper pen test is also a business driver. It gives your clients the evidence they need for auditors and to meet compliance rules they depend on, like SOC 2, HIPAA, PCI DSS, and ISO 27001. When you offer an affordable, fast, and manual penetration testing service, you become a core security partner. Our channel-only model is built for this. We are your behind-the-scenes team, delivering reports under your brand. You own the client relationship; we do the heavy lifting.
If you want a deeper dive, check out our guide on what is penetration testing.
Defining the Scope of a Pen Test
So, what are we actually testing? The scope of a pen test depends entirely on what you're trying to protect. We can break it down into a few main types to help you match the right test to your client's needs.
Each penetration test answers a different question about your client's security. Whether you're worried about an outside attacker or an inside threat, there's a test designed to find those risks.
The Five Phases of Network Penetration Testing
A real penetration test is a structured, five-phase mission. Think of it like a planned military operation, not a random attack. This process allows our certified experts to find vulnerabilities that automated scanners always miss.
This approach guarantees every pen test is thorough and gives you actionable results. It’s the difference between checking a compliance box and actually hardening a network against real attackers.
Phase 1: Reconnaissance (Information Gathering)
First up is Reconnaissance, which is all about gathering information. Before launching an attack, a hacker spends time learning about their target. Our testers do the same, using public information to map out your client's digital footprint.
They look for things like IP address ranges, employee names from social media, and details about the company’s technology. This step is critical for finding potential entry points and shaping the attack strategy.
Phase 2: Scanning (Probing the Network)
Next, we move to the Scanning phase. With the intel from reconnaissance, our pentesters use special tools to probe the target network. This is more than a simple vulnerability scan; it’s a focused effort to find live systems, open ports, and running services.
The goal here is to find an open "door." We’re looking for outdated software, unpatched systems, and sloppy setups an attacker would love to exploit. This phase helps us zero in on the best targets for the hands-on part of the penetration testing process.
This visual shows how we apply these phases in the two main testing environments—from both outside and inside the network.
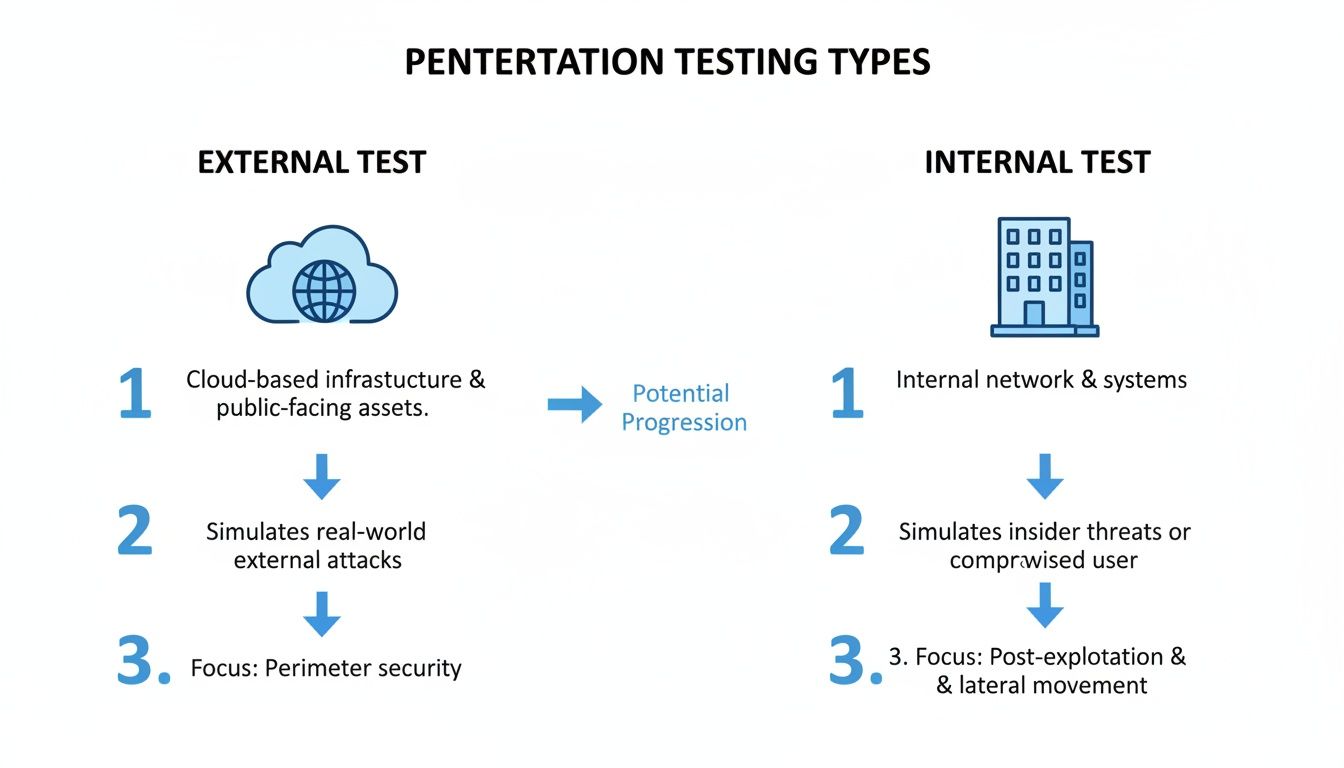
Whether we're testing from the outside like a hacker or from the inside like a rogue employee, our methodical approach doesn’t change.
Phase 3: Gaining Access (Exploitation)
This is where the "hacking" begins. During the Gaining Access phase, our OSCP, CEH, and CREST certified pentesters exploit the vulnerabilities we found. This is where manual pentesting proves its worth.
Our experts use creative thinking and advanced techniques to bypass security controls, just like a determined attacker. A win here means we have a foothold inside the network, proving a vulnerability is a real, exploitable risk.
Phase 4: Maintaining Access (Lateral Movement)
Getting in is just the first step. The Maintaining Access phase is about figuring out the real-world impact of a breach. Our testers try to move through the network—a technique called lateral movement—to see how far they can get.
The goal is to understand the "blast radius." Can an attacker become an administrator? Can they access sensitive data? This phase shows the potential business impact of a successful attack and is critical for any risk assessment.
Phase 5: Analysis and Reporting
Finally, we have Analysis and Reporting. A pen test is only as good as its report. We compile our findings into a clear, no-fluff document that's easy for you and your client to understand.
We break down the vulnerabilities, the methods used to exploit them, and the evidence of our access. Most importantly, we provide practical steps to fix the problems. As your channel-only partner, we deliver this report to you, ready to be white-labeled, solidifying your role as the trusted security advisor.
Uncover Insider Threats with Internal Pentesting
Your client's firewall might be strong, but what happens when the threat is already inside? An internal network penetration testing service answers that exact question. It simulates what a disgruntled employee or a hacker with a stolen password could do.
The goal is to see what damage they could do once they're past the perimeter. This kind of pen test shows how a bad actor could move through the network and get to critical data. For MSPs and vCISOs, this isn't just a problem—it's an opportunity to deliver serious security value.

An external test checks the front door. An internal penetration test checks if the doors inside the house are locked. It answers the question: "What's the worst that could happen if someone gets in?"
Our certified pentesters, holding qualifications like OSCP, CEH, and CREST, conduct this manual pentesting with the same access an average employee has. From there, they hunt for common but dangerous issues.
- Weak Passwords: How easy is it to crack passwords for other users or servers?
- Missing Patches: Are there unpatched systems on the network that offer an easy backdoor?
- Poor Segmentation: Can someone from marketing access sensitive HR or finance servers?
- Excessive Permissions: Does a standard user account have admin-level privileges it shouldn't?
By simulating these real-world attacks, we show you exactly how a small oversight can become a data breach. This is a crucial part of any legitimate risk assessment.
Demand is exploding for a reason. You can dig into more data about this growing market on dimensionmarketresearch.com. The need for affordable and effective services is urgent.
For any CPA, GRC firm, or MSP, offering internal pen testing is a game-changer. You're not just advising on compliance; you're helping clients achieve it. Our fast and affordable manual approach makes this possible. You can learn more about our internal penetration testing process.
Secure the Perimeter with External Pentesting
Every server, application, and cloud service your client connects to the internet is a potential door for an attacker. An external network pen test is how you check the locks on that digital perimeter. It's a simulated attack from an outsider, just like a real hacker.
Our certified pentesters probe your client's internet-facing assets, like web servers, VPNs, and firewalls, to find weaknesses. This is your client's first line of defense and a vital step for proving their security is up to par.

During an external network penetration testing engagement, our team acts just like a real-world adversary. With no prior knowledge of the network, it's a true blind test. The goal is simple: find and exploit vulnerabilities before a bad guy does.
Our OSCP, CEH, and CREST certified testers focus on common entry points attackers love, including:
- Misconfigured Firewalls: Rules that accidentally leave a door wide open.
- Outdated Software: Unpatched systems with known, easy-to-exploit flaws.
- Weak Credentials: Easy-to-guess passwords on public login portals.
- Exposed Services: Unnecessary services running on servers that widen the attack surface.
Finding and fixing issues like critical security vulnerabilities in network devices is exactly why this testing exists. It gives you proof that your client's most exposed assets are locked down.
Offering external pentesting is a smart move for any MSP or vCISO. It shows immediate value by securing the assets clients worry about most. For many, it's a requirement for compliance frameworks like PCI DSS, which mandates regular external testing.
Yet, many companies skip these tests because they think they're too expensive. With the average pentest costing thousands, our affordable, manual pentesting model fills a huge gap for your clients. This is a major opportunity for you to offer a high-value security service without the sticker shock.
In security, speed matters. A vulnerability left open is an invitation for an attack. The traditional pen testing industry is known for long lead times. We're different. Our process is built for speed. We deliver comprehensive, white-labeled reports within one week of the test. This means you can get to work fixing things right away.
By partnering with us, you can provide expert-led, manual penetration testing that is both affordable and fast. You own the client relationship; we provide the technical skill under your brand. Ready to learn more? Check out our guide on external network penetration testing.
Meeting Compliance with Network Penetration Testing
For many of your clients, a penetration test isn't just a good idea—it's mandatory. Compliance frameworks are the rules for data security, and auditors want proof that clients are actively looking for risks. A formal pen test is that proof.
This isn't about just checking a box. A real network penetration testing engagement shows your client is serious about security. It changes the conversation from "Are we compliant?" to "Are we secure?" That’s a huge value-add for any MSP, CPA, or GRC firm.
Think of a penetration test as the practical exam for compliance. Frameworks like SOC 2, ISO 27001, PCI DSS, and HIPAA all require vulnerability management and risk assessment. An automated scan doesn't cut it anymore. Auditors want you to simulate a real attack to see how security holds up.
Our detailed reports are built for this. They map our findings to the specific controls auditors look for, making compliance smoother. For a reseller, this means you can stop just advising on compliance and start selling the solution that gets them there.
A manual penetration test is critical for compliance because it finds what scanners miss. It shows a good-faith effort to find and fix vulnerabilities, proving due diligence.
By offering white label pentesting, you change the client relationship. You’re no longer just the "IT guy." You become their strategic security partner. In a crowded market, that’s a game-changer.
Our channel-only model makes this easy. We supply the expert pentesters—all certified with OSCP, CEH, and CREST—and the audit-ready reports. You bring the client relationship. We handle the complex testing, and you deliver a high-value service under your brand, building trust and loyalty.
Ultimately, offering this service transforms you from a vendor into an indispensable advisor. You can guide your clients through their compliance journey with an affordable, fast, and effective solution.
Partner With Us for White Label Pentesting
Building an in-house pentesting team is hard. It means finding expensive, certified talent and struggling to keep them busy. There’s a smarter way for Managed Service Providers (MSPs), vCISOs, and other IT resellers to offer this service.
We built our channel-only white label pentesting model for partners like you. We work completely behind the scenes, becoming your dedicated security team. You keep control of the client relationship, and we handle the manual pentesting under your brand. We will never compete with you for your clients.
You know the problems in the compliance industry: high prices, weak testing methods, and long waits for reports. This is an opportunity for you to step in with a real solution. Our partnership model was designed to fix those issues.
When you partner with us, you add a high-margin service to your lineup with zero overhead. No salaries, no certifications. You bring the client, and we deliver the expert-led penetration testing. It’s the simplest way to grow your business.
Our model is the solution. We offer affordable, expert-led pentesting with reports delivered in about a week. This lets you close deals faster and helps your clients fix risks without waiting.
Your clients and their auditors expect real expertise. They don't want a scan dressed up as a pentest. When you partner with us, you get our whole team of security pros on your side, giving you instant credibility.
Our pentesters hold the certifications that matter:
- OSCP (Offensive Security Certified Professional): The gold standard for hands-on hacking skills.
- CEH (Certified Ethical Hacker): Shows broad knowledge of attack vectors.
- CREST (Council of Registered Ethical Security Testers): A globally recognized cert that proves our team tests methodically.
You can tell your clients their pen test is being handled by top-tier professionals.
We’ve made it easy to start selling network penetration testing. Our process is clean, simple, and built to get you answers—fast.
Here's how it works:
- Get a Quote: Send us the project details. We'll help you scope the work and give you a clear, affordable price.
- We Perform the Test: Our team conducts a thorough manual pentesting engagement.
- Receive Your Report: In about a week, you get a detailed, white-labeled report with your brand on it, ready for your client.
This simple model frees you up to focus on what you do best—managing client relationships.
Your Network Penetration Testing Questions Answered
We get it. Diving into network penetration testing can bring up a lot of questions. Here are the straight answers to the most common things our partners ask.
What’s the difference between a scan and a pentest?
Think of it like this: a vulnerability scan is like jiggling doorknobs to see if any are unlocked. It’s an automated check for potential weak spots.
A penetration test is when a security expert actually tries to pick the lock and see how far they can get inside. Our OSCP and CREST certified experts manually exploit weaknesses to confirm if they're real risks. It’s a hands-on test that gives you much deeper insight.
How long does a network penetration test take?
This depends on the scope, but our process is built for speed. Forget vendors who take weeks to even start. We typically complete the test and deliver your white-labeled report in about a week.
This fast turnaround means you get actionable results to clients quickly. No more waiting around while critical issues for SOC 2 or HIPAA go unfixed. Our goal is to make this process efficient for you as a reseller.
How much does a penetration test cost?
The security industry has a problem with inflated pricing, making a real penetration test seem out of reach. Our model is different. We provide affordable, high-quality manual pentesting without the huge price tag.
Because we’re a channel-only partner, our pricing is designed for you to add a healthy margin while still giving your clients a great deal. The final cost depends on the scope, but our mission is to make top-tier security accessible.
What do I get at the end of the pen test?
You get a professional, detailed report ready for you to white-label with your own brand. It’s not just a data dump; it’s a clear roadmap.
The report lays out what we tested, what we found, and step-by-step guidance on how to fix it. We write it for both your technical team and the C-suite, making it a powerful tool to show your value and guide your client's risk assessment strategy.
Ready to add a high-margin, in-demand security service to your offerings? Partner with us for affordable, fast, and expert-led white label pentesting.


.png)
%202.png)

.avif)
.png)
.png)
.png)

