A client calls on a Tuesday afternoon. They’re chasing a new contract, their CPA or auditor wants documentation by Friday, and now they need your network security policies in writing. Not a vague slide deck. Not a firewall screenshot. Actual policy language, mapped to controls, with proof it’s enforced.
If you’re an MSP, vCISO, GRC advisor, or compliance-focused reseller, this is your new sales motion whether you planned for it or not. Clients don’t just want managed IT anymore. They want a provider who can help them pass reviews, satisfy insurers, support SOC 2, HIPAA, PCI DSS, and ISO 27001, and keep them from looking careless in front of customers.
That creates a risk and an opening. If you can’t deliver policy guidance and validation, someone else will. If you can, you become much harder to replace.
Why Your Clients Suddenly Demand Security Policies
A lot of MSPs still treat security policies like paperwork. That’s a mistake. Buyers, auditors, and insurers see policies as evidence that a company has rules, accountability, and a repeatable process for protecting systems.

The pressure isn’t coming out of nowhere. In 2025, ransomware was involved in 44% of data breaches, while the exploitation of vulnerabilities in devices like VPNs rose to 20% of initial access vectors, which is why documented, enforced network security policies have become a frontline defense against common attacks, according to NordLayer’s 2025 cybersecurity statistics summary.
Why this changes the MSP sale
Your client might ask for a policy because a prospect requested it in procurement. They might need it for a cyber insurance questionnaire. They might need it because their board finally realized “we have antivirus” is not a security strategy.
In every version of that conversation, your role changes. You’re no longer just patching endpoints and managing licenses. You’re helping define who gets access, how sensitive systems are separated, what gets monitored, and what happens when something goes wrong.
Practical rule: If your client has to prove trust to win revenue, they need policies. If you can package policies with validation, you’ve created a recurring security offering.
The business opportunity most MSPs miss
A strong policy practice helps you win more than compliance projects. It gives you a reason to talk about risk assessment, network design, cloud exposure, and security testing without sounding like you’re upselling fear.
It also protects retention. The MSP that can hand a client a usable policy set, explain it in plain English, and back it up with a pen test report looks strategic. The MSP that says “we can probably find a template online” looks replaceable.
That’s why policy work isn’t admin overhead. It’s margin.
Building Your Network's Rulebook for Security
A network security policy is the rulebook for how a client’s network is supposed to behave, akin to the security plan for a building.
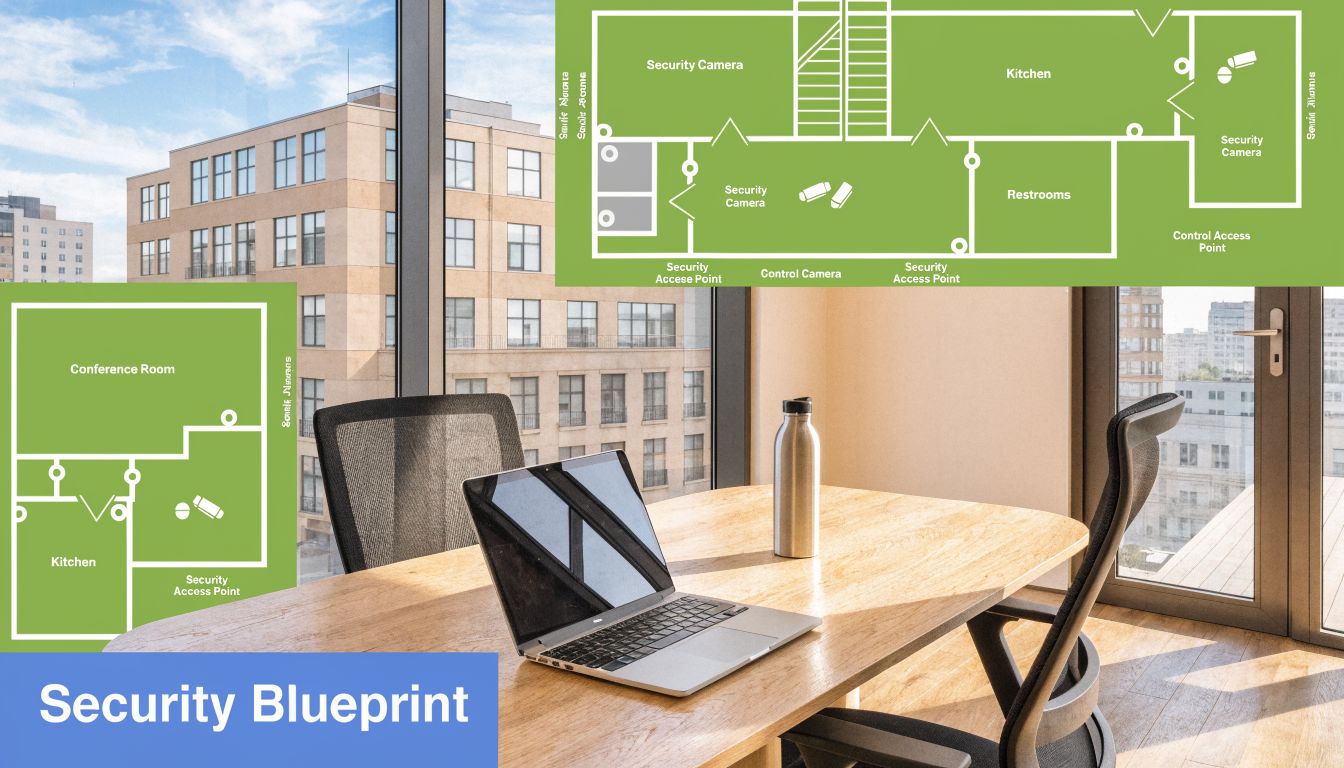
It says who gets a keycard, which rooms are locked, which doors stay alarmed, where cameras point, and what the staff does during a break-in. Your client’s network needs the same kind of clarity.
According to the Cisco 2025 Cybersecurity Readiness Index, 31% of global business leaders say Network Resilience is their most challenging security pillar, which makes a documented network security policy the foundation of resilience, as Cisco explains in its 2025 Cybersecurity Readiness Index.
What a real policy should cover
A useful policy doesn’t read like legal filler. It tells people and systems what’s allowed and what’s blocked.
Here’s the simplest way to explain it to clients:
- Access rules: Who can log in, from where, and with what level of privilege
- Traffic rules: Which systems can talk to each other and which ones can’t
- Device rules: How firewalls, routers, VPNs, switches, and endpoints are configured
- Monitoring rules: What gets logged, reviewed, and escalated
- Response rules: Who acts first when suspicious activity shows up
That’s also why policy work should start with design, not a document template. If the network architecture is sloppy, the policy will be fiction. If you need a practical starting point, a network architecture review helps you spot where the written rules and the actual environment don’t match.
What to stop doing
Stop handing clients copied templates packed with generic language. They won’t match the client’s cloud setup, remote access model, line-of-business apps, or admin workflow.
Stop writing policies that only exist to pass a checkbox. Good network security policies should help your techs make faster decisions. If a junior engineer can’t read the rulebook and know what’s approved, the policy is too vague.
The Five Pillars of Network Security Policies
Every client environment is different, but the core structure shouldn’t be. If you’re building network security policies for managed clients, five pillars matter most.

Access control and least privilege
Start with identity. Users should get the minimum access they need, not broad rights because it’s faster to deploy.
That means separate admin accounts, role-based access, approval for privilege changes, and short-lived elevation where possible. For MSPs managing many tenants, this matters even more because one bad credential can create a client-wide mess.
Segmentation and blast radius control
Most MSPs know segmentation matters. Fewer define it well in policy.
Your rulebook should identify sensitive systems, approved communication paths, and blocked lateral movement routes. That includes restricting administrative protocols where they don’t belong and isolating critical assets from standard user networks.
Effective micro-segmentation, a key policy component, can reduce attacker lateral movement by as much as 92% in tested environments, and that level of granular control is important for containing a breach and supporting what auditors look for in SOC 2 and PCI DSS, as outlined in Exabeam’s guide to network security policy components and micro-segmentation.
Device configuration and change discipline
Many policies often fall apart at this point. They say “secure configurations will be maintained” and stop there.
Write down what that means in operational terms:
- Firewall rules: Review approval, cleanup cadence, and documentation standards
- VPN settings: MFA requirements, device restrictions, and access scope
- Switch and router changes: Named ownership, backup expectations, and rollback plans
- Endpoint controls: Baselines for local admin, host firewall, and remote access tools
Specificity matters because compliance teams and clients don’t trust broad statements anymore.
Monitoring that creates action
Logging isn’t the goal. Useful detection is.
Your policy should define what gets collected, who reviews alerts, what severity levels trigger action, and how evidence is retained for compliance. If your client has Microsoft 365, cloud workloads, remote users, and on-prem gear, the policy should reflect that actual mix rather than pretending everything lives behind one firewall.
Field advice: If nobody owns alert review, you do not have monitoring. You have noise storage.
Incident response that people can follow
When a client gets hit, the first question won’t be “where’s our elegant policy binder?” It’ll be “who is doing what right now?”
So write response steps for humans. Keep it plain. Define escalation contacts, isolation authority, communication rules, evidence handling, and when legal, insurance, or compliance teams are notified.
A policy should reduce confusion under pressure. If it adds confusion, rewrite it.
Linking Your Policies to SOC 2 and ISO
Compliance buyers rarely care about policy language in isolation. They care whether your policy supports a framework they already recognize.
That’s why your network security policies should map cleanly to SOC 2, ISO 27001, and the broader structure many teams use for risk management. When you show that alignment, the client sees business value instead of paperwork.

Mapping policy components to compliance controls
| Policy Component | SOC 2 Trust Service Criteria | ISO 27001:2022 Annex A | NIST CSF V2.0 |
|---|---|---|---|
| Access Control | CC6.1 Logical & Physical Access Controls | A.9 Access Control | Protect |
| Data Protection | CC6.3 Data Encryption, Data Backup | A.12 Operations Security, A.18 Privacy | Protect |
| Incident Response | CC7.1 Incident Management | A.16 Information Security Incident Management | Respond |
| Vulnerability Management | CC7.2 Vulnerability Scanning | A.12.6 Management of Technical Vulnerabilities | Identify / Protect |
| Security Training | CC8.1 Security Awareness Training | A.7.2.2 Information Security Awareness, Education and Training | Govern / Protect |
This is the language GRC teams, auditors, and procurement departments understand. If your client asks why they need a documented access policy, you can tie it directly to trust criteria and annex controls instead of giving a generic security answer.
Make your evidence easier to use
If your client is preparing for attestation, it also helps to review the broader SOC 2 audit requirements so your policy set supports what auditors will inspect.
Keep the mapping simple. Don’t build a giant spreadsheet nobody updates. Tie each policy statement to a control family, identify the technical owner, and define what evidence proves enforcement.
That’s how policy work becomes a repeatable service instead of a custom fire drill every quarter.
Proving Your Security Policies Actually Work
A client signs the contract, asks for your security policies, and then their auditor asks the question that decides whether you keep the account. Show me proof these controls are enforced.
That is the gap many MSPs leave wide open. They deliver a polished policy set, then back it up with a scan export and a few screenshots. Compliance-driven buyers do not accept that. They want evidence that access restrictions hold up under attack, segmentation blocks movement, and exceptions have not turned the policy into theater.
A penetration test gives you that proof. It tests whether the rules you wrote survive contact with a real attacker mindset. For resource-strapped MSPs, this is how you turn policy work from paperwork into a service clients renew.
Why validation decides renewals
Policies drift fast. Firewall rules change. Admin access expands. Temporary exceptions become permanent. If you cannot validate enforcement, you are asking clients to trust documents instead of outcomes.
That is a bad bet in a market where buyers care about audits, customer security questionnaires, and board scrutiny. The MSP that can show tested controls keeps credibility. The MSP that cannot will lose deals to firms that package policy, validation, and remediation into one offering.
A vulnerability scan helps with hygiene. It does not prove an attacker cannot chain weaknesses together and break the policy in practice.
What good validation looks like
Your pentest should answer the questions clients, auditors, and procurement teams care about:
- Access control enforcement: Can a low-privilege user reach systems the policy says are restricted?
- Segmentation enforcement: Can testers pivot across VLANs, cloud workloads, or business units that should be isolated?
- Remote access exposure: Do VPN, RDP, SSO, and third-party access paths create policy violations?
- Exception risk: Have one-off changes or legacy systems weakened the standard your client thinks is in place?
- Evidence quality: Does the report clearly tie findings to business risk, failed controls, and corrective action?
Reporting matters. If the report is vague, slow, or written for engineers only, it does not help your client close audit gaps or justify remediation spend. A strong pen test report template shows the level of detail you should expect before you put your name on the deliverable.
Why white-label pentesting fits the MSP model
Many pentest vendors are a poor fit for MSPs. They are expensive, slow, and too dependent on automation. By the time the report arrives, the environment has changed and the client has lost patience.
Manual testing is the right fit for policy validation because human testers check how controls fail in context. They follow the path an attacker would take. They find the exception, weak trust relationship, or overlooked route that a scanner misses.
White-label delivery also protects your client relationship. Your client wants one accountable advisor. They do not want a third party stepping into the account and owning the security narrative. MSP Pentesting offers channel-only, white-label pentest services across internal, external, cloud, web, mobile, social engineering, and physical environments using certified pentesters with OSCP, CEH, and CREST backgrounds.
If you want to win and retain compliance-driven clients, sell policies with enforcement built in. Write the rulebook. Test it manually. Hand the client evidence they can use in audits, board updates, and renewal conversations. That is how a lean MSP builds a profitable security offering instead of a stack of documents no one trusts.
Your Top Questions on Security Policies Answered
MSPs usually ask practical questions once they start packaging policy work. Good. That means you’re thinking like an operator, not just a writer.
How do I build simple network security policies for small clients
Start with a lean template, then customize it for access control, remote access, segmentation, device hardening, monitoring, and incident response. Keep the language plain enough that a client owner and your help desk can both understand it.
Many small organizations operate below the cybersecurity poverty line, lacking funds and expertise, which is why MSPs can create value with scalable templates validated by affordable pentesting, as discussed by Aspen Digital’s analysis of the cybersecurity poverty line.
Don’t sell a small medical office or local manufacturer an enterprise binder full of controls they’ll never implement. Sell them a policy set they can follow and defend.
What’s the difference between a vulnerability scan and a penetration test
A vulnerability scan finds known issues. A penetration test tries to exploit them in context.
That difference matters for policy validation. A scan can tell you a service looks exposed. A pen testing engagement can show whether that exposure results in access, movement, or data risk. For SOC 2, HIPAA, PCI DSS, and ISO 27001 conversations, clients usually need more than a list of scanner output.
How often should policies be reviewed
Review them whenever the client changes something important. New cloud workloads, office moves, mergers, remote admin changes, firewall redesigns, compliance projects, and vendor access all justify updates.
You should also review them on a regular cadence tied to the client’s risk and compliance needs. If you’re not revisiting the policy, you’re almost guaranteed to drift away from reality.
How do I make this profitable as a reseller or vCISO
Standardize the package. Pair policy drafting with a risk assessment, a network review, remediation guidance, and recurring pentesting.
That creates a service clients can understand and budget for. It also keeps you from doing custom one-off policy work that burns hours and crushes margin.
If you want a channel-only partner to help you turn network security policies into a sellable service, MSP Pentesting can support your team with white label pentest, pen test, and penetration testing services across internal, external, cloud, web, mobile, and physical environments. We don’t compete with our partners. We help MSPs, vCISOs, GRC firms, CPAs, and resellers deliver affordable, manual pentesting with fast reporting that backs up compliance claims and helps retain clients. Contact us today to learn more.



.avif)
.png)
.png)
.png)

