Welcome to our guide on the penetration testing process, built for Managed Service Providers (MSPs), vCISOs, and IT resellers. Think of a penetration test, or pentest, like a fire drill for your client's cybersecurity. We get permission to simulate a real-world cyberattack to find security weaknesses before the bad guys do.
What is the Penetration Testing Process?
A penetration test, also called a pen test, is a methodical process for finding and exploiting security vulnerabilities. It’s an essential part of any serious cybersecurity program and a hard requirement for compliance frameworks like SOC 2, HIPAA, and PCI DSS. If you’re an MSP or vCISO, understanding this process is critical to selling and delivering security services that your clients actually need.
The managed service industry has a problem with pentesting. Prices are often inflated, lead times are too long, and the testing methodologies can be weak. We are the solution. We offer affordable, fast, and thorough manual pentesting as a channel-only partner. This means you can resell our services under your brand, building a profitable security offering without ever competing with us.
Think of a penetration test like hiring a friendly inspector for your client’s digital house. Our certified testers will ethically check all the doors and windows to see if any are unlocked, helping you secure everything before a real burglar comes knocking.
This flowchart breaks down the entire penetration testing process into its three core stages: planning, testing, and reporting.
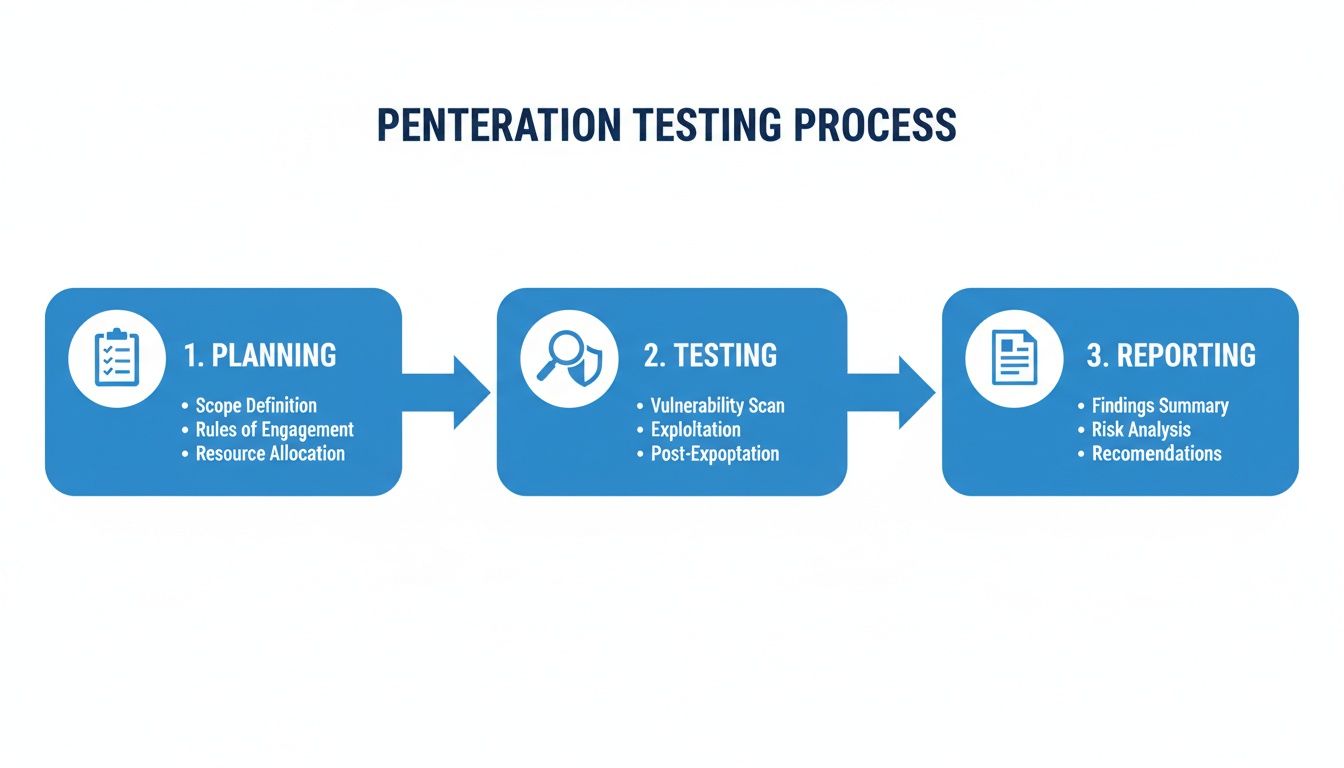
This simple workflow shows how a quality pen testing engagement moves from setting clear goals to hands-on analysis and, finally, to a report with actionable steps.
Our approach is built for efficiency and real-world value, ensuring you can confidently solve your clients' security and compliance headaches. Our team of OSCP, CEH, and CREST certified testers delivers high-quality reports that you can proudly white label and hand directly to your clients. We help you turn a compliance chore into a strategic advantage.
A Breakdown of The Five Pentesting Phases
A professional penetration test isn't just one event; it's a multi-stage project. Each phase has a distinct purpose, building on the last to ensure a thorough and valuable assessment. Here’s a quick overview of the five essential stages our team follows.
| Phase | Objective |
|---|---|
| 1. Planning & Scoping | Define the test's scope, objectives, and Rules of Engagement (RoE). This ensures everyone is on the same page and the test stays within legal and technical boundaries. |
| 2. Reconnaissance & Discovery | Gather as much information as possible about the target systems. This "casing the joint" phase identifies potential entry points and attack vectors. |
| 3. Vulnerability Analysis & Scanning | Use automated tools and manual inspection to identify weaknesses in the target environment based on the information gathered during reconnaissance. |
| 4. Exploitation & Post-Exploitation | Attempt to actively exploit the identified vulnerabilities to gain access. If successful, the tester then tries to escalate privileges and move laterally, mimicking a real attacker. |
| 5. Reporting & Remediation | Document all findings in a clear, actionable report. This includes a non-technical executive summary, detailed technical findings, and practical steps for remediation. |
From initial planning to the final report, this structured approach guarantees that nothing is missed and that your clients receive a comprehensive assessment they can actually use to improve their security posture.
This guide will walk you through each phase in detail. By mastering this process, you can become the go-to security resource your clients need to manage their GRC and risk assessment programs.
Phase One: Planning and Scoping the Engagement
Every solid pentest starts with a plan. You wouldn't build a house without a blueprint, and you shouldn't run a security test without a clear strategy. This first phase is where we get everything on the table, working directly with you—our MSP, vCISO, or GRC partner—to map out the entire project. The goal is to make sure our efforts are perfectly aligned with what your client actually needs.
We start by defining the scope. This simply means we decide together what our ethical hackers will target. Is it a public-facing website, the internal network, or a new mobile app? Just as important, we define what’s completely off-limits to avoid disrupting your client’s day-to-day business. Getting this right from the start is non-negotiable.
With the scope set, we establish the Rules of Engagement (RoE). Think of these as the official "rules of the game" for our manual pentesting team. This isn’t just us telling you how it's going to be; it’s a collaborative process to make sure the pen test runs smoothly and safely. The RoE nails down specifics like testing windows, approved techniques, and emergency contacts. This step is all about managing expectations and making sure there are no surprises.
As an IT reseller, this planning phase is where you really add value. You’re the one who translates your client's business goals and compliance drivers—like SOC 2, HIPAA, or ISO 27001—into a concrete technical plan. Properly understanding the principles of a cybersecurity risk assessment is crucial here for defining the right testing objectives. This focuses our efforts on what truly matters, whether it’s protecting customer data, securing IP, or hitting a compliance deadline.
By working together closely during scoping, we ensure our affordable, fast, and manual pentesting delivers real impact. This is how we turn a simple security test into a strategic tool that proves your value as a trusted advisor.
Our team of OSCP, CEH, and CREST certified pros depend on this detailed plan to deliver a test that’s both thorough and relevant. This initial legwork guarantees the final report isn't just a list of problems, but a direct answer to your client’s biggest security concerns.
Phase Two: Reconnaissance and Vulnerability Analysis

Once the rules are locked in, our ethical hackers get to work. This is where the real detective work of the penetration testing process begins. We break this stage into two parts: reconnaissance (gathering intel) and vulnerability analysis (finding the weak spots). Think of reconnaissance as our team "casing the joint." They’re mimicking a real attacker, carefully mapping out your client's entire digital footprint to get a crystal-clear picture of the target. This groundwork is absolutely essential for a thorough pen test.
In this part of the penetration testing process, the mission is simple: gather as much information on the target as possible. We use passive reconnaissance to find publicly available info without touching the client's systems. Then we use active reconnaissance to gently probe systems for live hosts, open ports, and software versions. This phase gives our pentesters a detailed map of the battlefield. It shows them where the juicy targets are and where security might be thinnest.
With a map in hand, our experts shift to vulnerability analysis. This is where we start actively probing for actual security holes. Our approach blends the speed of automated tools with the irreplaceable critical thinking of our manual pentesting team. We kick things off with automated scans to find low-hanging fruit—known vulnerabilities and common misconfigurations. But we don't stop there. An automated scan is just a noisy starting point, often full of "false positives" that aren't real risks. You can see a full breakdown of the differences in our guide on security vulnerability scanning.
This is where the skill of our OSCP, CEH, and CREST certified testers truly shines. They manually investigate every single finding, cutting through the noise to focus on what actually matters. They also hunt for complex business-logic flaws that automated tools are completely blind to.
For an MSP or vCISO, this deep analysis is everything. It guarantees that the findings you present to your clients for compliance needs like SOC 2 or PCI DSS are legitimate, exploitable risks. This manual validation is a cornerstone of our affordable and fast white label pentesting service, delivering a high-quality risk assessment you can confidently stand behind.
Phase Three: Exploitation and Gaining Access

This is where the real "penetration" happens. After we’ve mapped out the target and found the likely weak spots, our ethical hackers get to work trying to exploit them. The mission isn’t to cause damage—it’s to prove that a vulnerability is real and show what the business impact could be. Think of it like this: in the last phase, we found a window that looked unlocked. Now, we’re going to give it a gentle push to see if it swings open.
During this phase, our certified pentesters start acting just like a real-world attacker would. This is where the true value of manual pentesting shines, leaning on human creativity and skill instead of just automated scripts. A successful exploit is often a chain reaction leading to outcomes like gaining initial access, escalating privileges to an admin, or accessing sensitive data to prove a full-blown breach is possible. This step is absolutely critical for compliance frameworks like SOC 2 and PCI DSS, which demand proof that you’ve actually validated vulnerabilities.
This is where the skill of our OSCP, CEH, and CREST certified professionals really pays off. Automated scanners are decent at finding known issues, but they can't think on their feet. Our team can chain together multiple, seemingly low-risk flaws to create a high-impact attack path a scanner would miss every single time. For you as an MSP or vCISO, this is a game-changer. Our affordable and fast manual pentesting gives you undeniable proof of risk.
This hands-on exploitation is what separates a true pen test from a simple vulnerability scan. It provides the "so what?"—the context that shows clients exactly what’s at stake and why they need to act now.
The data doesn’t lie. Organizations that conduct annual penetration testing see fewer breaches. With ransomware attacks jumping over 35% each year, many firms are boosting their pentesting budgets to guard their assets. You can read more about the growing market for these essential services and its projected 15.29% growth rate. Ultimately, this phase gives you the ammunition for real security conversations. Our white label pentesting service arms you, our reseller partner, with clear, actionable results that make you the hero.
Phase Four: Reporting And Strategic Remediation
After all the poking and prodding is done, what are you left with? The single most important part of the penetration testing process: the report. A pen test is only as valuable as the report it generates. If it’s just a mountain of technical jargon with no clear next steps, it's useless. That’s why we build our reports to serve two very different, but equally important, audiences.
First, you get a clean, straightforward executive summary. It’s written in plain English, cutting out the technical noise to explain the real-world business risks to leadership. Then, you get the deep-dive technical breakdown. This section gives your IT team the step-by-step details they need to replicate our findings and, more importantly, actually fix the problems.
The report is the final product, the culmination of all that hard work in the exploitation and analysis phases. As a reseller, you’ll get this entire report, fully white-labeled with your brand, typically within a week of testing. Our quick turnaround means your clients can get to work right away. It puts you, the MSP or vCISO, in the driver's seat to guide clients on where to start. For a closer look at how we structure these deliverables, check out our guide on building a solid penetration testing report template.
For your clients in regulated industries, the report is more than just a list of fixes—it’s non-negotiable proof of due diligence. Meeting compliance standards is a massive driver for organizations investing in penetration testing. A solid report from a manual pentesting engagement is exactly what auditors for frameworks like SOC 2, HIPAA, and ISO 27001 want to see. It proves you’re not just checking a box but are actively managing your risk assessment and GRC programs.
As your channel-only partner, we give you a report that makes you look like the expert you are. It’s clear, professional, and designed to help you strengthen client relationships by turning a simple compliance check into a powerful tool for ongoing risk management.
This approach reinforces your value, helping you shift from being just another service provider to becoming a strategic security partner. Our affordable, fast, and thorough pen testing service is built to support your business, giving you the deliverables you need to succeed without ever competing for your clients.
Phase Five: Retesting And Continuous Improvement

The penetration test isn't over when you hand over the report. This final phase, retesting, is where you prove the fixes actually worked and your client’s security is stronger. It's the step that turns a one-off project into real, measurable security improvement. After you deliver our white-labeled report and your client’s team patches the holes, we go back in. Our expert pentesters target the exact vulnerabilities we found the first time around to make sure they’re truly gone.
Retesting is what gives you and your client concrete proof that the money they spent made a difference. It confirms vulnerabilities are closed and that the remediation work didn't introduce new, unexpected flaws. This validation isn’t just a nice-to-have; it's a mandatory requirement for compliance audits like SOC 2, HIPAA, and PCI DSS. Auditors don't just want a list of problems—they want proof you solved them.
A pen test without a retest is like a doctor diagnosing an illness but never checking if the medicine worked. You're just hoping for the best. This final verification is what completes the cycle and demonstrates true due diligence in any GRC program.
We include this final check in our affordable and fast pentesting services. It’s the proof you need to close the loop on the engagement and show your client a job well done. Our OSCP, CEH, and CREST certified experts re-run the original exploits to confirm they fail and check for any new vulnerabilities. This step delivers the documentation auditors need to see, proving that you’ve properly addressed every risk.
As your channel-only partner, our goal is to help you build profitable, long-term client relationships. The retesting phase is the perfect time to talk about what’s next. By scheduling annual or semi-annual penetration tests, you help clients stay ahead of new threats without breaking their budget. It shifts your service from a single fix to an ongoing security program. If you want to dig deeper into this model, check out our article on the benefits of continuous pentesting. This phase doesn’t just end the penetration testing process. It sets you up for the next engagement, creating a cycle of improvement that keeps your clients secure and your business growing.
Your Pentesting Questions, Answered
We get a lot of the same questions from MSPs and vCISOs looking to add pentesting to their stack. Let's cut through the noise and give you the straight answers you need to protect your clients and grow your business.
How is Manual Pentesting Different From a Scan?
Think of an automated vulnerability scan like a spell checker. It’s fast and catches common mistakes, but it has zero understanding of context. It will flag a known missing patch or a default password, but it also buries you in "false positives" that aren't real risks. It's a decent first pass, but it's absolutely not a true pen test.
A manual penetration test, on the other hand, is like bringing in a master locksmith to check your work. Our testers take those initial scan results, throw out the noise, and then use their skill and creativity to find the weaknesses that matter. This manual pentesting approach finds complex attack chains and business logic flaws that automated tools are blind to—which is exactly why a manual pen test is a non-negotiable requirement for serious compliance frameworks like SOC 2 and PCI DSS.
How Can We Resell Your White Label Pentesting?
It couldn't be easier. We're a 100% channel-only company. That means we never sell to your clients directly or compete with you. Ever. You own the client relationship from start to finish; we just act as your on-demand, expert pentesting team.
The whole process is designed to make you look good:
- Scope the Project: You work with your client to figure out what needs testing. If you need help, we've got your back.
- We Do the Work: Our certified pentesters get the job done quickly and quietly, with minimal disruption.
- You Deliver the Report: We hand you a thorough, professional report that is completely white-labeled with your company's branding.
You present the findings to your client as if your own team did the work. This lets you add a high-margin security service to your lineup without the six-figure headache of hiring, training, and retaining an in-house expert.
As a reseller, you become the go-to expert for a critical security service. We handle all the technical heavy lifting while you strengthen your role as a trusted advisor and capture revenue that would otherwise go straight to a competitor.
Which Pentester Certifications Are Important?
Not all certifications are created equal. You need to look for pentesters who hold certifications that require intense, hands-on practical exams. These are the ones that actually prove someone can break into a network, not just answer questions about it.
The credentials that really matter in this industry are:
- Offensive Security Certified Professional (OSCP): This is the undisputed gold standard. It involves a grueling 24-hour, hands-on exam where testers have to compromise a live lab network. If they have this, they know their stuff.
- Certified Ethical Hacker (CEH): A well-known certification that provides a broad foundation in hacking tools and methodologies.
- CREST Certifications: For enterprise-grade engagements, certifications from CREST (Council of Registered Ethical Security Testers) are globally recognized and highly respected.
Our team is built around experts who hold these top-tier certifications. You can rest easy knowing your clients' penetration testing is being performed by skilled, ethical professionals who have proven their abilities under pressure.
Ready to add affordable, fast, and expert white label pentesting to your service offerings? Contact us today to learn how we can help you grow your business and secure your clients. Learn more at https://msppentesting.com.



.avif)
.png)
.png)
.png)

