When you’re setting up secure remote access for a client, the choice between an SSL and an IPsec VPN isn't just a small technical detail. It’s a huge decision that shapes how your clients work securely. The main difference is straightforward: SSL VPNs give users browser-based access to specific applications, while IPsec VPNs lock down a device's entire network connection.
Getting this choice wrong can create security holes or frustrate users with a clunky experience, and neither of those outcomes makes you look good.
Understanding SSL VPN vs. IPsec for Your Clients

As an MSP or vCISO, your VPN recommendation directly impacts user experience, scalability, and how we approach a network architecture review or a penetration test. This isn't about picking the "best" technology; it's about matching the right tool to a client’s business needs and security goals.
Think of it this way: SSL VPNs are great for speed and simplicity. They are perfect for remote teams who just need to get into a few internal web portals. There's often no software to install, which makes getting started super easy.
On the other hand, IPsec VPNs are the heavy-duty workhorses for building a secure, always-on tunnel between entire networks, like connecting two branch offices. It’s a bit more work to set up, but it provides total network protection. Your choice here changes everything, from how you’ll scope a pen test to what it takes to pass a SOC 2 or HIPAA audit.
Breaking Down SSL VPN vs. IPsec VPN
This table breaks down the key attributes that distinguish SSL from IPsec VPNs, giving you a quick reference for making the right call for your clients.
| Attribute | SSL VPN | IPsec VPN |
|---|---|---|
| Primary Use Case | Remote user access to applications | Site-to-site and full network access |
| OSI Layer | Application Layer (Layer 7) | Network Layer (Layer 3) |
| Client Software | Often clientless (browser-based) | Requires dedicated client software |
| Access Granularity | Granular (per-application) | Broad (full network access) |
| Ease of Setup | Generally easier and faster | More complex and configuration-heavy |
| Firewall Traversal | Easier (uses standard HTTPS port) | Can be blocked by firewalls |
| Pentesting Focus | Web portal, authentication, XSS | Configuration, key management |
As you can see, there's no single winner. It all comes down to the use case. An SSL VPN offers precise control for application access, while an IPsec VPN provides a fortified, all-encompassing tunnel. Getting this right from the start is crucial for building a secure and efficient network for your clients.
How Each VPN Technology Actually Works

To make the right call for your clients, you need to know what’s really going on under the hood. The core difference between an SSL VPN and an IPsec VPN is simple: it’s where they operate in the network stack.
That single distinction changes everything. It dictates the user experience, what they can access, and most importantly, where our OSCP and CEH certified pentesters will hunt for vulnerabilities during a penetration testing engagement.
An SSL VPN lives at the Application Layer (Layer 7). Think of it as a gatekeeper for specific apps. It uses the same technology that secures every website you visit—Transport Layer Security (TLS)—to create a secure link between a user's browser and a single application.
This is exactly why they’re a go-to for remote access. A user just needs a web browser. No special software required. They log in and get access only to the resources you’ve approved, keeping them away from the rest of the corporate network. It’s perfect for contractors or employees on personal devices.
Analyzing Security Models and Attack Surfaces
When you're the trusted advisor, you know comparing the security of SSL VPN vs. IPsec VPN is more than a feature checklist. It's about understanding their core security differences and how those differences create separate attack surfaces for a penetration test.
IPsec is often seen as the more robust option from a pure security standpoint. It was built from the ground up to secure IP packets at the network level. It doesn't just suggest encryption; it mandates it, creating a truly hardened tunnel.
SSL VPNs, on the other hand, run on the Transport Layer Security (TLS) protocol. The security isn't baked into the protocol in the same way; it depends on how it's set up. One misconfiguration, like using a weak cipher, can completely undermine its protections.
Our OSCP, CEH, and CREST certified pentesters go after an IPsec VPN by focusing on configuration and protocol-level weaknesses. We look for weak keys, outdated protocols, and misconfigurations that could let an attacker bypass the tunnel.
Common Vulnerabilities and Your Pentesting Focus
Every piece of technology has a weak spot, and for something as critical as a VPN, attackers are always looking for a way in. The SSL VPN vs IPsec VPN debate isn't just about features; it’s about understanding their completely different attack surfaces.
Knowing where to look is half the battle when you're responsible for a client's security. As an MSP or vCISO, this is the knowledge you need to scope a pen test that actually finds things. The vulnerabilities you hunt for in an SSL VPN are worlds apart from an IPsec setup.
SSL VPNs and Their Web-Facing Risks
The biggest selling point of an SSL VPN—its simple browser access—is also its biggest security headache. The attack surface is almost entirely focused on that web portal. It's an open door to the internet, and if it's not locked down tight, attackers will find a way through.
Our manual pentesting teams consistently find the same handful of issues when we run an SSL VPN penetration test: weak credentials, outdated TLS ciphers, Cross-Site Scripting (XSS), and no Multi-Factor Authentication (MFA). This is why a specialized pen test is so crucial. Automated scanners will miss the nuanced misconfigurations that our OSCP and CEH certified pentesters are trained to find.
As a channel-only partner, we provide white label pentesting that you can resell under your brand. We deliver fast, affordable reports from our CREST-certified team, giving your clients clear, actionable guidance to fix these exact issues.
IPsec VPNs and Configuration Nightmares
With IPsec, the whole game changes. The focus of a penetration test shifts from a web app to the underlying network configuration. These vulnerabilities aren't about bad code; they're about simple mistakes in how the tunnel is built and managed.
Here’s what our team hunts for when we're running an IPsec pen test: weak pre-shared keys, insecure key exchange modes, and misconfigured split-tunneling. This is exactly why a pen test of an SSL VPN is a must-have for uncovering common misconfigurations—a key requirement for compliance audits like SOC 2.
SSL VPN vs. IPsec: Picking the Right Tool
Choosing a VPN is a critical security decision. As an MSP or vCISO, getting the SSL VPN vs IPsec VPN choice right for your client shows you know your stuff. It also ensures the solution actually works for their business without creating a new attack surface.
The whole debate boils down to a single question: who needs access, and what do they need to access? If you have a sales team that just needs access to a web-based CRM, an SSL VPN is your go-to. It's fast, doesn't require a clunky client install, and lets you lock down access to only specific applications.
For most remote users, SSL VPNs are the standard because they just work. This simplicity is hard to beat for sales teams, contractors, and BYOD environments.
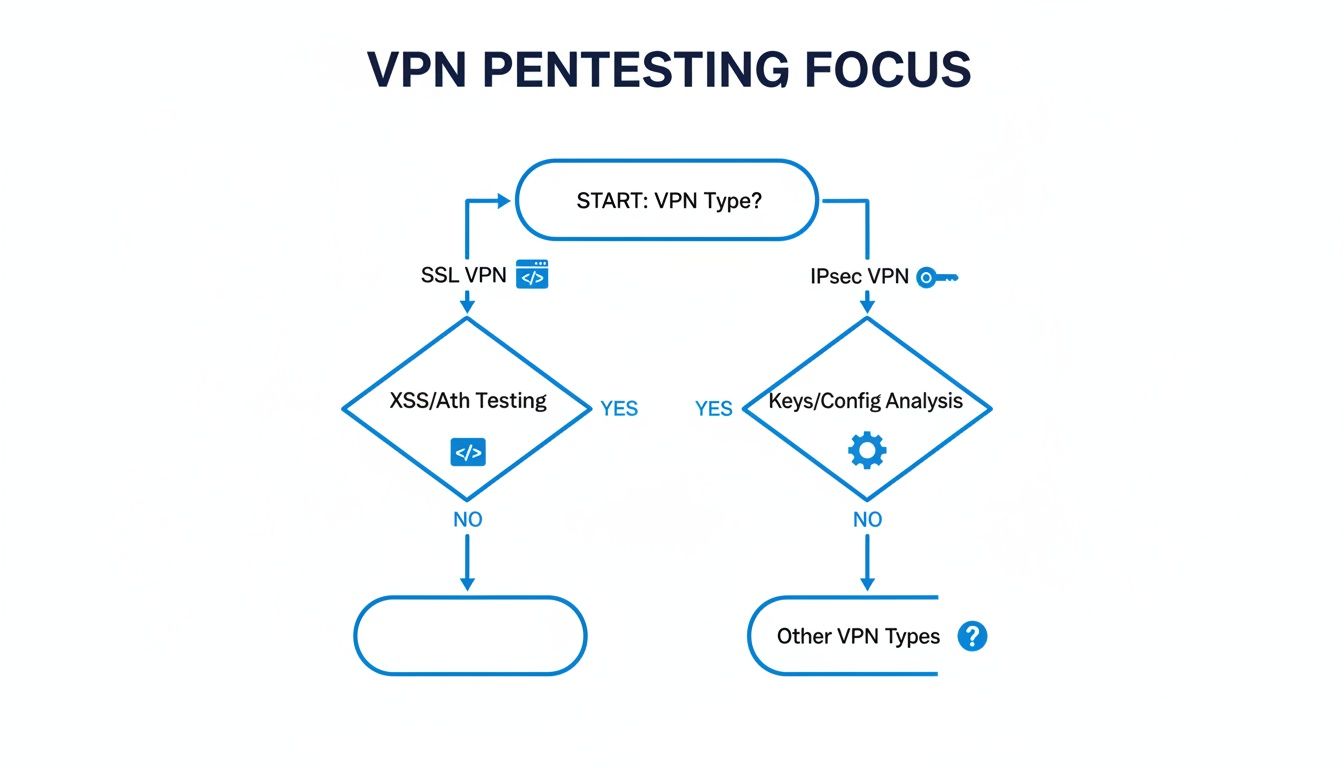
When we pentest an SSL VPN, we're hunting for web application flaws. With an IPsec VPN, the focus shifts entirely to misconfigurations on the gateway itself. When you need to connect two entire offices or give a developer full network access, IPsec VPN is the only serious choice. It's the way to go for branch office connectivity and for power users like IT staff.
The global market reflects this divide. The Asia Pacific region is seeing a huge spike in SSL VPN adoption. That market is projected to hit $5,261.7 million by 2025 according to a report on cognitivemarketresearch.com. Ultimately, most businesses use a hybrid model: IPsec for stable site-to-site connections and SSL VPNs for a mobile workforce. As their trusted reseller partner, your job is to deploy the right tool for each, then validate it with affordable, fast, white label pentesting.
Partnering for Affordable and Fast VPN Pentesting
Whether your clients use SSL VPNs, IPsec VPNs, or a hybrid setup, one thing is certain: if you want real security and compliance, you need regular penetration testing. But the managed service world has a problem. It's full of pentest vendors with inflated prices, bad testing methods, and long lead times. We are the solution.
We are a channel-only partner. We are 100% committed to your success and we will never compete with you for your clients. Our whole business is built to empower MSPs, vCISOs, and GRC companies like yours.
We deliver affordable, fast, and fully manual pentesting that you can sell as your own service. Our white label pentesting lets you add a high-margin security offering to your stack, all under your own brand. You won't be waiting weeks for a report; we get you comprehensive results fast.
Our team is made up of pros holding OSCP, CEH, and CREST certifications. They know exactly what to look for in both SSL and IPsec VPN environments. For an SSL VPN, they'll go after the web portal. For an IPsec VPN, they'll dig into weak key management and configuration mistakes.
As your reseller partner, we provide the expert firepower you need to tackle complex security challenges. We help you demonstrate the due diligence required for standards like SOC 2, HIPAA, and PCI DSS, proving to your clients that their remote access is locked down tight.
Picking the right side in the SSL VPN vs IPsec VPN debate is only the first step. The more important step is continuous validation. Learn more about how to become a pentest partner and grow your business with us. We handle the expert-level testing, so you can stay focused on being the trusted advisor your clients depend on. Contact us today to get started.
Frequently Asked Questions About VPN Security
Your clients are confused about VPNs, and that confusion is a risk. When the SSL VPN vs. IPsec VPN debate comes up, you need to have the right answers ready. Here are the straight-up answers to the questions we see MSPs and vCISOs field all the time.
Is IPsec VPN Always More Secure Than SSL VPN?
No. While IPsec gets a reputation for being tougher for site-to-site tunnels, its security is only as good as its configuration. A lazy IPsec setup is far more dangerous than a properly managed SSL VPN.
An SSL VPN can be rock-solid for remote access when you do it right. That means forcing modern TLS protocols, locking it down with strong MFA, and hardening the web portal itself. The "more secure" choice isn’t about the label—it’s about the specific use case and how well you maintain it.
How Often Should We Pen Test a Client's VPN?
Compliance frameworks like SOC 2 or PCI DSS might say an annual penetration test is enough, but that’s just a minimum. Waiting 12 months between tests leaves a massive window open for attackers.
A pen test should happen after any major change. This includes a major firmware update, a new VPN gateway going live, or right after a major vulnerability hits the news. Our affordable and fast manual pentesting makes this kind of continuous validation realistic.
Can One Penetration Test Cover Both VPN Types?
Yes, but the scope needs to be perfectly clear. An external network penetration test can target both, but they are fundamentally different. A good pen test treats them that way.
An SSL VPN test hunts for web application flaws in the login portal. In contrast, an IPsec VPN test focuses on protocol weaknesses and configuration mistakes. To deliver a real risk assessment, you need to define separate testing goals for each. This lets our OSCP and CREST certified testers dig deep. As a reseller, offering this kind of detailed testing proves you know your stuff.
At MSP Pentesting, we give our partners the ability to offer expert security validation without the ridiculous costs or long waits. Our channel-only model means we're your team, delivering the in-depth, manual pentesting you need to lock down your clients.
Contact us today to see how our white label pentesting services can help you win more deals.


.avif)
.png)
.png)
.png)

