Value Added Resellers Guide for MSPs vCISOs and IT Resellers
You lose deals when a prospect asks for a pentest, a pen test, or full penetration testing support and you can’t deliver it cleanly. That’s usually when a competitor slides in with a broader package, or worse, a bloated security firm shows up with high prices, long wait times, and a scanner dressed up as a real assessment.
That gap is where value added resellers become more interesting than most MSPs realize. They already sit close to the client, they already influence buying decisions, and they already bundle technology into business outcomes. If you pair that reach with white label pentesting, you turn a weak spot into a revenue stream.
Your Guide to Value Added Resellers

A value added reseller is not just a company that resells software or hardware. A good VAR takes existing technology, adds setup, integration, support, and practical advice, then sells a complete solution that works in the client’s environment.
That matters because VARs already have trust and access. The global Value-added Resellers for IT market was valued at USD 12.72 billion in 2025 and is projected to reach USD 24.84 billion by 2035, with 68% of enterprises depending on VARs for IT solutions, according to Business Research Insights on the VAR market.
Most MSPs still treat VARs like old-school box movers. That’s a mistake. A modern reseller often sits right in the middle of cloud projects, endpoint rollouts, identity work, and compliance-driven buying.
Practical rule: If a VAR influences the tech stack, they can also influence whether a client buys a risk assessment, penetration test, or recurring security service.
The opportunity is simple. VARs need stronger security depth. MSPs, vCISOs, and GRC firms need easier access to buyers who already trust an advisor. Put those together and you get a channel that can sell more complete solutions without building every capability in-house.
What Exactly Is a Value Added Reseller
Think of a normal reseller like a store that sells you a bicycle in a box. A value added reseller is the shop that assembles it, adjusts the brakes, fits the seat, and makes sure you can ride it safely the same day.
In IT, that means the VAR doesn’t just sell Microsoft, Cisco, cloud licenses, backup tools, laptops, or firewalls. They also connect the pieces, deploy them, train the client, and make the purchase useful.
Where the value actually comes from
The value-add usually shows up in a few places:
- Integration work that makes products function together
- Deployment support so the client isn’t stuck figuring out setup alone
- Advisory help around product fit, workflow, and compliance
- Ongoing service handoff to an MSP, internal team, or specialist partner
A lot of VARs hit the same wall, though. Security is now part of nearly every deal, but many resellers still can’t deliver serious compliance support or real penetration testing. That’s why the smarter move is partnership, not pretending. A key challenge for VARs is integrating cybersecurity into their offerings for frameworks like SOC 2, and CBH notes that partnering with specialized pentest providers can lead to 64% higher close rates.
That’s not just a delivery issue. It’s a sales issue too. If your team struggles to turn technical capability into a repeatable offer, this sales outsourcing service is a useful example of how channel-focused firms tighten positioning and pipeline support.
Why MSPs should care
You don’t need to become a VAR. You need to understand how to work with one. If you want a simple primer on how channel delivery works behind the scenes, this explanation of what a white label service is helps frame the model.
A VAR opens doors. You bring the managed service, the security insight, or the white label pentesting engine behind it.
VARs vs MSPs and MSSPs Explained
People mix these labels up all the time. That creates bad expectations, weak proposals, and channel conflict that doesn’t need to exist.
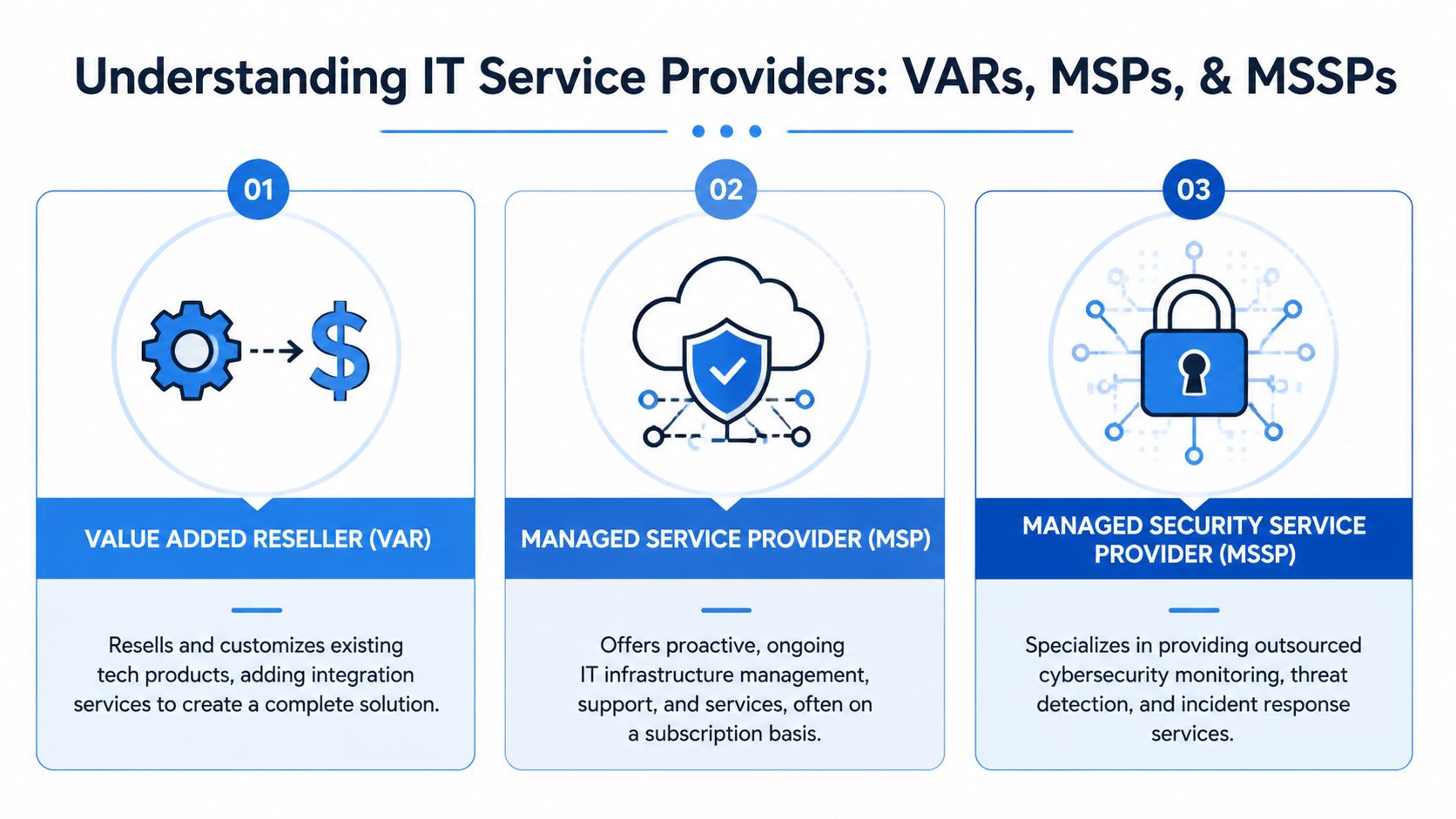
A VAR usually sells and implements. An MSP usually manages and supports over time. An MSSP focuses on outsourced cybersecurity operations and specialized defense work.
VAR vs MSP vs MSSP At a Glance
| Attribute | Value Added Reseller (VAR) | Managed Service Provider (MSP) | Managed Security Service Provider (MSSP) |
|---|---|---|---|
| Core model | Project and solution resale | Recurring managed IT services | Recurring managed security services |
| Main focus | Product bundling, integration, deployment | Ongoing IT operations, support, maintenance | Security monitoring, detection, response |
| Sales motion | Transactional and project-led | Subscription and relationship-led | Subscription with security depth |
| Customer need | Buy and deploy the right stack | Keep systems stable and supported | Reduce cyber risk and improve response |
| Typical security gap | Deep testing and validation | Advanced security specialization | Broader IT ownership outside security |
Why the difference matters
A VAR can sell a firewall. An MSP can manage it. An MSSP can monitor threats moving through it. A pentest provider can validate whether any of that would hold up under real attack.
The smartest partners don’t argue over labels. They line up roles so the client gets one complete answer.
That’s the comparison that matters. If your client needs SOC 2, HIPAA, PCI DSS, or ISO 27001 support, the conversation usually leaves simple product resale fast. Buyers want proof, not promises. They want to know whether the controls work.
MSPs and vCISOs should treat VARs as upstream deal partners. MSSPs should treat them as distribution. VARs should stop trying to fake every security function with a slide deck and a scanner report.
Why MSPs And vCISOs Should Partner With VARs

If you’re an MSP or vCISO, partnering with VARs offers significant benefits. You get access to deals earlier, you attach services to active technology projects, and you avoid the grind of sourcing every opportunity from scratch.
VARs also need this. Many of them know clients want more security, but they don’t want to build a full security bench, hire specialized testers, or own every delivery risk themselves.
According to MSP Weekly’s analysis of VARs shifting to MSP models, VARs that move toward managed services can achieve over 20% growth in cybersecurity revenue streams. That tells you the demand is already there in their customer base.
What each side gets
For MSPs and vCISOs:
- Warmer opportunities from existing reseller relationships
- Bigger deal scope when security gets bundled into the sale
- More authority in compliance conversations tied to real testing
For VARs:
- Stronger close rates when security objections are handled well
- A broader service catalog without staffing every specialty
- Less risk than trying to build penetration testing internally
This is also where channel discipline matters. A partner model only works if the pentest provider doesn’t poach accounts. That’s why channel-only delivery is so attractive. You keep the client relationship. The specialist does the work behind the curtain.
If your team is building a formal partner motion, this guide for partner sales leaders is worth reading because it shows how channel revenue grows when ownership and partner roles are clear.
Add Pentesting To Your VAR Service Offering

Most reseller offers break down. They say “security” but deliver a vulnerability scan, a generic PDF, and a long delay before anyone explains what matters.
That’s not enough for serious SOC 2, HIPAA, PCI DSS, or ISO 27001 work. A client paying for a penetration test expects a human to think, pivot, validate exploitability, and explain impact in plain English.
What to add to the offer
A practical VAR security bundle should include:
- Manual pentesting for web apps, internal networks, external networks, cloud, mobile, or social engineering
- White label reporting so the partner keeps brand control
- Remediation guidance that helps the client fix issues, not just read about them
- Retesting options so compliance teams can verify closure
Why manual testing matters
Automated tools are useful for coverage. They are not the same as a real pen test.
A manual tester checks logic flaws, chaining issues, access control mistakes, business process abuse, weak cloud permissions, and attack paths that scanners miss. That’s why certifications matter. OSCP, CEH, and CREST signal that the tester has been trained to do actual offensive security work, not just launch software and export a report.
Field advice: If the “penetration testing” vendor can’t clearly explain what was tested manually, you’re probably buying a scan with better branding.
For channel teams that want a ready-made model, pentesting for the channel lays out how white-labeled delivery fits MSP and reseller workflows. MSP Pentesting is one example of a channel-only provider that offers white-labeled manual pentests across multiple environments with certified pentesters.
Onboarding And Pricing Your Pentest Service
The onboarding process should be boring. That’s a good thing. If adding white label pentesting feels complicated, your team won’t sell it consistently.
The market tailwind is there. The global VARs Software market is estimated at USD 58,988.34 million in 2026 and is projected to grow significantly, driven by digital transformation and demand for customized software solutions that increasingly need security validation like penetration testing, according to Tussell’s public sector VAR market analysis.
A simple onboarding checklist
Pick the service menu
Decide what you will sell first. Start with the environments your clients already ask for, such as web app, external, internal, cloud, or mobile.Define handoff rules
Make it clear who owns scoping, scheduling, client communication, remediation follow-up, and final delivery.Use brand-ready templates
Your reports, proposal language, and scoping notes should be easy for an MSP, vCISO, CPA firm, or GRC advisor to present under their own brand.Set turnaround expectations
Long waits kill deals. Buyers facing audits and compliance deadlines won’t tolerate vague scheduling.
Pricing without confusion
Keep the pricing model easy to explain. Your margin should come from packaging, account ownership, and advisory value, not from hiding the service behind inflated markups.
A better model is straightforward:
- Base scope first based on environment and complexity
- Partner margin next so the MSP or reseller earns cleanly
- Retest separately if the client needs validation after fixes
- Rush delivery only when needed so speed stays an advantage, not a headache
If you want a channel-specific starting point, the pentest partner program shows how white-label billing and delivery can be structured for resellers.
Frequently Asked Questions About Reselling Pentests
Is a vulnerability scan the same as a pentest?
No. A scan looks for known issues automatically. A real penetration test includes human validation, attack paths, and business context.
Why do compliance buyers ask for manual pentesting?
Because serious frameworks care about evidence that controls work in practice, not just that a tool found missing patches.
Can a VAR resell pentesting without hiring an in-house team?
Yes. That’s the whole point of a white-label model. The reseller keeps the relationship and the specialist handles delivery.
What should a good report include?
Clear findings, business impact, remediation guidance, and language a technical team and an executive can both use.
Do remediation and retesting matter?
Absolutely. A report without a fix path just creates more work for the client and makes the reseller look incomplete.
If you want to add affordable, fast, channel-only pentesting, pen testing, and penetration testing to your MSP, vCISO, GRC, or reseller offering, MSP Pentesting can help you deliver white-labeled manual assessments without competing for your clients. Contact us today to learn more.



.avif)
.png)
.png)
.png)

