A vendor risk assessment is all about figuring out the potential dangers that come with bringing a third-party supplier into your world. Think of it like this: if you let a friend borrow your car, you'd want to make sure they're a good driver first. It's the same idea, but for your business and your clients.
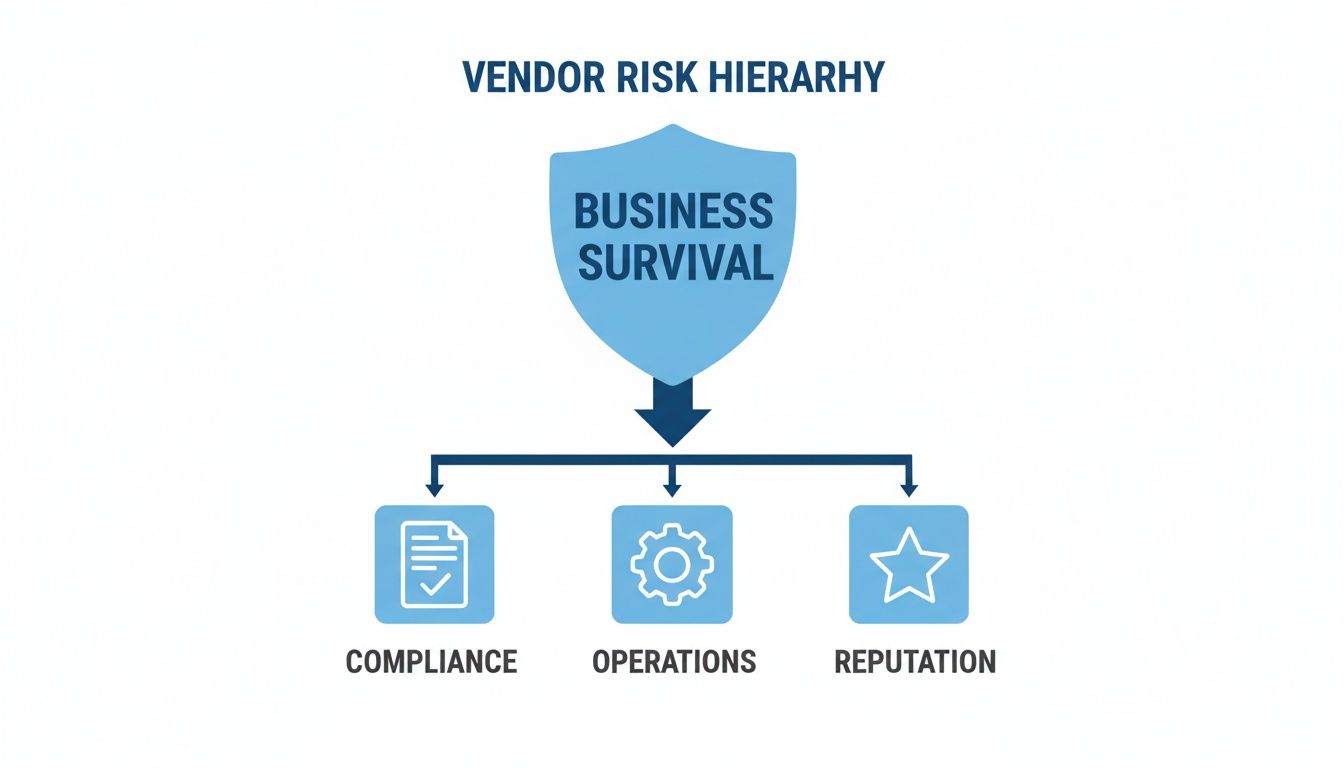
This process ensures a vendor's security (or lack of it) doesn't become your next big problem. What used to be a simple compliance checkbox has now become a core survival strategy for any modern MSP or vCISO.
Why Vendor Risk Assessment Is No Longer Optional
In the past, checking a vendor’s security was often an afterthought. Now, it’s a critical part of protecting your business and your clients from real, damaging threats. Every new piece of software, cloud service, or contractor you bring on board is another potential doorway for an attacker.
Ignoring these risks is a massive gamble. A single weak vendor can lead to a devastating data breach, cripple your operations, and shred the reputation you’ve worked so hard to build. For MSPs and vCISOs, the stakes are even higher; if your vendor fails, your client's trust in you evaporates.
Understanding the Soaring Demand for Vendor Oversight
The market tells the whole story. The global vendor risk management market is exploding, showing how seriously companies are taking this. This isn't just a trend; it's a direct response to how much we all rely on third parties for everything from IT infrastructure to specialized software.
This growth is driven by a need to avoid breaches and meet strict compliance demands. Frameworks like SOC 2, HIPAA, PCI DSS, and ISO 27001 require businesses to have a tight grip on their vendors. For an MSP, having a strong vendor risk assessment process is a huge selling point. It shows you're a strategic security partner, not just another IT provider.
To really get into the weeds of this process, a resource like A Practical Guide to Vendor Risk Assessment offers some great insights.
How to Map Your Vendor Landscape Effectively
Trying to give every single vendor the same deep-dive security review is a fast track to burnout. It’s like using a sledgehammer to hang a picture frame—total overkill for most situations. A smarter approach for any vendor risk assessment is to sort them into tiers based on the actual risk they bring to the table.
Not all partners are created equal. The company that stocks your office coffee machine operates in a completely different risk universe than the cloud provider hosting your client's sensitive data. This is why a tiered system is mission-critical for an efficient risk assessment program.
First, you need to know who you're dealing with. Create a master inventory of all your vendors. For each one, capture what service they provide, what data they access, how they integrate with your systems, and how critical they are to the business. If they disappeared tomorrow, would it be a minor headache or a full-blown crisis?
Once you have your list, categorize them into tiers like Critical, High, Medium, and Low. Critical vendors are the ones with the keys to the kingdom—they access sensitive data and are essential to operations. By sorting vendors this way, you create a roadmap that tells you where to focus your most intense efforts, like a manual pentesting engagement.
Why Technical Due Diligence Is So Important
You’ve tiered your vendors, now comes the real work: due diligence. This is where you gather actual evidence to back up a vendor’s security claims. The process usually kicks off with security questionnaires, which you can learn more about in our guide on the vendor security assessment questionnaire.
Next is reviewing their documentation, like SOC 2 reports or ISO 27001 certifications. These are important because they offer third-party validation that a vendor has certain controls in place. But here’s the hard truth: questionnaires and reports are static snapshots in time. A vendor can have a clean report from six months ago and be full of critical vulnerabilities today.
That trust-based model is a huge gamble. You can't just take their word for it. For major projects, a solid vendor due diligence checklist can help you spot risks, but even that can’t verify technical reality. This is where penetration testing comes in.
Think of it this way: a vendor’s documentation is them telling you their house is secure. A pen test is you hiring an expert to actually jiggle the locks and check the windows. It's the only way to verify that the security controls a vendor claims to have are actually working against real-world attacks. This moves your risk assessment from a theoretical exercise to a practical one.
As an MSP or vCISO, this is where you can shine. We offer affordable, white-label pentesting services built for channel partners. Our manual pentesting is done by certified pros with OSCP, CEH, and CREST certifications. And because we are a channel-only partner, we never compete with you. We're simply the technical firepower in your back pocket.
How to Integrate Penetration Testing into Assessments
After wading through questionnaires and certifications, it's easy to call it a day. But that paperwork only tells you what a vendor claims their security looks like. To actually know if their defenses hold up, you have to test them. This is the core of any real vendor risk assessment—trust, but verify.
For your most critical vendors, the ones with deep access to your clients’ data or systems, a penetration test is the only way to prove their controls are working. It shows whether their shiny SOC 2 report translates to real-world security.

Different types of penetration testing exist, like web application, external network, or cloud infrastructure tests. The right pen test depends on what the vendor does. Nailing the scope is everything to get results that truly reflect the risk that vendor brings to the table. Automated scanners are quick but they can't think like a real attacker. That’s why manual pentesting is so critical.
A skilled human tester, like our team of OSCP, CEH, and CREST certified professionals, can find the complex flaws that automated tools miss. This gives you the ground truth on a vendor's security. If you want to learn more about ongoing validation, check out our guide on continuous penetration testing.
As an MSP or vCISO, talking about a pen test for a client's vendor can be tough. Clients might see it as slow and expensive. That's why we provide affordable, fast, and white-label pentesting services designed for you to sell under your own brand. We are a channel-only partner, so we never compete with you. Our job is to give you the technical firepower you need to deliver a comprehensive vendor risk assessment.
How to Drive Remediation and Continuous Monitoring
Finding a vulnerability isn’t a failure—it's the whole point of a vendor risk assessment. The real work begins after you've flagged the risks: pushing for fixes and ensuring the vendor's security stays strong over time. Your value as an MSP or vCISO is in guiding this process.
After a penetration test, work with the vendor to build a remediation plan. This plan needs specific actions, clear ownership, and firm timelines. Track these plans closely. This shows your client you are actively reducing their risk.
Your biggest leverage is before a contract is signed. Bake security requirements right into vendor contracts and SLAs. This means specifying the right to conduct a penetration test, requiring compliance with frameworks like SOC 2, and defining penalties for security failures. This gives you the authority to enforce standards.
A vendor risk assessment can't be a one-and-done deal. A vendor that looks clean today could be breached tomorrow. Continuous monitoring is the backbone of any mature risk management program. You can dig deeper into market trends by checking out the vendor risk management market report on Mordor Intelligence.
Continuous monitoring means reassessing high-risk vendors annually, which may include a recurring pen test. It also means keeping an eye on security news and triggering a review if a vendor makes a major change. This proactive approach provides real, ongoing value and positions you as a long-term strategic partner.
Answering Common Vendor Risk Assessment Questions
As an MSP or vCISO, your clients will have questions about their vendor risk assessment program. Having the right answers helps you lead these conversations with confidence.
So, how often should you assess vendors? It depends entirely on the risk. Critical vendors need a full risk assessment annually, including a manual pentesting engagement. High-risk vendors also get an annual review. Medium-risk vendors can be reviewed every 18-24 months, while a check-in every two years is fine for low-risk ones.
What’s the difference between an assessment and a pentest? A vendor risk assessment is like running a background check—it’s a broad evaluation of their security program based on documents. A penetration test is like hiring an expert to try and break into their systems—it's a real-world test to find actual vulnerabilities. The pen test separates theory from reality.
How can you convince clients to invest in this? Frame it around their business risk. A breach at their payroll provider is a breach of their company. Lean on compliance requirements for frameworks like SOC 2 or HIPAA. And this is where our white-label pentesting is your superpower. You present an affordable, fast solution as an integrated part of your security service, making it an easy "yes" for the client.
At MSP Pentesting, we built our entire model to help our partners deliver this kind of robust vendor validation. We're a channel-only, white-label shop, which means you can sell expert manual penetration testing under your brand, without the crazy overhead. Contact us today to learn how we can help you strengthen your clients' vendor risk assessment programs.



.avif)
.png)
.png)
.png)

