Your client asks a fair question: “How do you stop a real cyber attack, not just install tools and hope?”
If you run an MSP, serve as a vCISO, support GRC work, or advise clients on SOC 2, HIPAA, PCI DSS, or ISO 27001, you need a simple answer that makes sense to non-technical buyers. The Cyber Kill Chain gives you that answer.
Most articles treat it like a classroom topic. That’s a mistake. For resellers and managed providers, understanding what is a cyber kill chain helps you explain risk, justify penetration testing, and keep clients from shopping elsewhere for security help you should already own.
What Is the Cyber Kill Chain and Why It Matters for MSPs

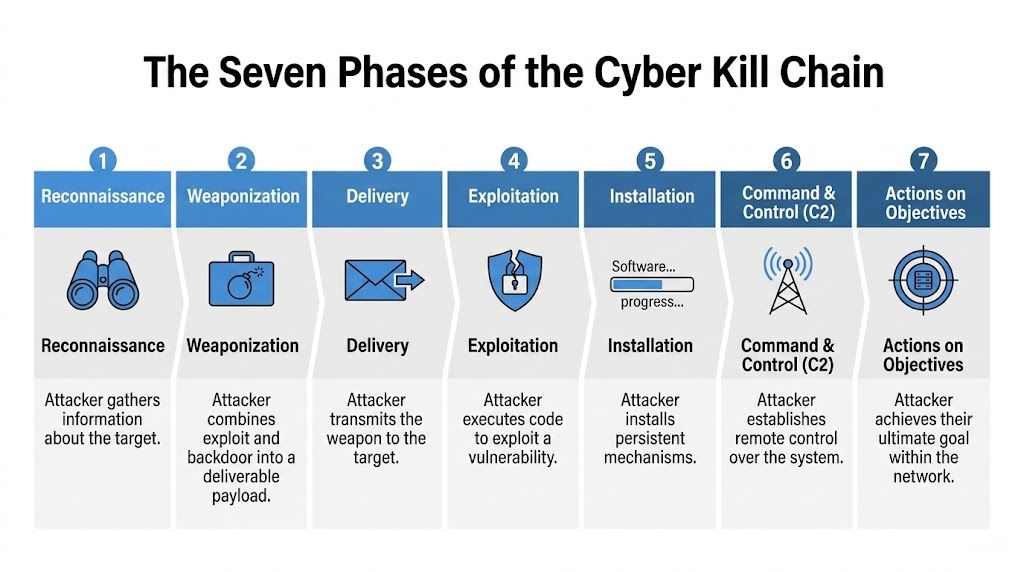
The Cyber Kill Chain is a cybersecurity framework developed by Lockheed Martin around 2011. It breaks attacks into seven sequential stages, which helps defenders stop an intrusion before it reaches the final objective, as explained by Netskope’s overview of the Cyber Kill Chain.
For an MSP, that matters because clients don’t buy theory. They buy confidence. They want to know you can identify how an attacker gets in, how they stay in, and where they can be stopped.
Why clients care about this framework
When a client is preparing for compliance, renewing cyber insurance, or facing board questions, they need more than a list of tools. They need a risk story they can follow.
The kill chain gives you a way to say:
- Attackers plan first: They research people, systems, and weak points.
- They move in stages: Email, web apps, credentials, and internal access all fit into a pattern.
- You can stop them early: A good control or a good pen test can break the sequence before real damage happens.
Practical rule: If you can’t explain how an attacker would move from public exposure to business impact, your client will assume you’re guessing.
This is also why layered security lands better when you frame it as business protection, not tool sprawl. If you want a plain-English way to discuss defense-in-depth with clients, this article on security in layers is useful.
Teams working toward leadership roles often need broader context too. A solid Certified Information Systems Security Professional (CISSP) study guide can help connect frameworks like the kill chain to governance, risk, and operational decision-making.
The Seven Phases of the Cyber Kill Chain Explained
Think of a cyberattack like a bank job. The criminal doesn’t start by opening the vault. They study the building, build a plan, get inside, avoid detection, and only then take what they came for.
That’s the kill chain.
The seven phases in plain English
- Reconnaissance
The attacker studies the target. They gather OSINT, review social profiles, identify exposed systems, and learn how employees work. Splunk notes that reconnaissance activity correlates with 80-90% of attack success rates, and richer target profiling can increase phishing effectiveness by up to 40% in its Cyber Kill Chain explainer at Splunk. - Weaponization
The attacker combines an exploit with a payload. That could mean pairing a malicious document with remote access malware or packaging code for a web app exploit. Splunk also notes this preparation can take nation-state actors 1-2 days. - Delivery
The weapon gets sent. That may be through email, a malicious link, a compromised website, or another entry path. - Exploitation
The target does something the attacker wants, or a system vulnerability gets triggered. Here, the malicious code runs. - Installation
The attacker plants persistence. They want access that survives a reboot, a user logoff, or a quick cleanup. - Command and Control
The compromised system talks back to the attacker. Once that channel exists, the attacker can issue commands remotely. - Actions on Objectives
This is the payoff. Data theft, ransomware deployment, lateral movement, privilege abuse, or business disruption all happen here.
A kill chain is useful because it forces one question at every step: where can we break this before it becomes a breach?
What this means for pentesting
A pen test should map to these phases. An external penetration test can reveal what an attacker sees in reconnaissance. A web application test can expose exploitation paths. An internal network penetration testing engagement can show whether installation and lateral movement are too easy.
That’s why the kill chain is practical. It turns “do we need pentesting?” into “which stage are we exposed in, and how fast can we fix it?”
Real World Examples of the Kill Chain in Action
A phishing-led ransomware incident is easy to picture because it happens in ways clients already understand. An attacker sends a believable email. That’s delivery. A user clicks, malicious code runs, and the attacker gains a foothold. That’s exploitation and installation. Remote control follows, then the files get encrypted when the attacker reaches their objective.
That story matters because it shows clients a breach is rarely one bad click by itself. It’s a chain of events. Good pen testing helps you test the weak links before an attacker finds them first.
A web application breach tells the same story in a different language. The Equifax incident is a strong example. A 2017 breach exposed 147 million records after attackers exploited an unpatched Apache Struts vulnerability, highlighting failures tied to exploitation and installation, as discussed in the verified data drawn from CrowdStrike’s framing of the event. That’s the kind of failure that turns a technical issue into a regulatory, legal, and revenue problem fast.
When evidence handling matters after a security event, your team also needs a clean process for documentation and preservation. A simple resource on chain of custody can help non-forensics teams understand why handling records properly matters.
The lesson for MSPs is simple. Clients don’t retain you because you mention EDR, firewalls, or awareness training. They retain you because you can connect a realistic attack path to a practical fix, then prove whether the fix works with a pentest or penetration test.
Limitations and Evolution Beyond the Original Model

The original kill chain is useful, but it isn’t perfect. Real attackers don’t always move in a neat straight line. Some skip steps, reuse access, or rely on built-in tools that don’t look like classic malware.
That’s why mature security teams don’t stop with the original model.
Where the classic model falls short
The biggest weakness is linear thinking. If your team assumes every attack starts with long reconnaissance and a custom payload, you’ll miss the opportunistic attacks that move fast.
Microsoft highlights this problem in its explanation of the model’s evolution. In 2017, the Unified Kill Chain merged Lockheed Martin’s model with MITRE ATT&CK into an 18-stage framework to better reflect non-linear behavior. Microsoft also notes that phishing can bypass early reconnaissance through opportunistic delivery, a technique seen in 32% of retail incidents in the cited material at Microsoft Security.
Why ATT&CK helps
The kill chain shows the broad path. MITRE ATT&CK gives you the detailed behaviors inside that path.
Use the kill chain when you need a business narrative for clients, boards, and compliance conversations. Use ATT&CK when you need sharper technical mapping for detection, response, and validation.
Bottom line: The kill chain tells you where the attacker is in the story. ATT&CK helps you understand how they’re acting inside that chapter.
For vCISOs, GRC firms, and compliance advisors, using both frameworks shows maturity. It strengthens your risk assessment process and helps you explain why one client needs a web app penetration testing engagement while another needs internal network testing, social engineering, or cloud validation.
How MSPs Can Break the Chain with Pentesting
Most MSPs still sell security like a stack of products. That’s weak positioning. Clients already hear that pitch from everyone else.
A better approach is to sell assurance. Show clients how you test whether their controls interrupt an attacker at key stages.
Turn the kill chain into a service model
The operational gap is real. Safous notes that 68% of breaches involve supply chain compromises targeting MSPs, and it also reports that integration of MITRE ATT&CK with the Kill Chain rose 40% in SOC tools over the last year in its discussion of MSP-focused kill chain strategy at Safous.
That should change how you package services.
- External pen test: Helps validate reconnaissance exposure and likely delivery paths.
- Web app penetration test: Finds exploitation opportunities before attackers do.
- Internal penetration testing: Tests whether one compromised device becomes full domain exposure.
- Social engineering assessment: Shows whether delivery and user-driven exploitation are too easy.
- Cloud and hybrid testing: Checks whether modern attack paths bypass your assumptions.
Why manual pentesting wins
Automated scans have a place, but they don’t replace a real penetration test. Clients need context, attack logic, and prioritized findings they can act on.
That’s why manual pentesting is the right fit for resellers and managed providers. It’s easier to explain, easier to align with SOC 2, HIPAA, PCI DSS, and ISO 27001, and easier to tie to a client’s actual business risk. If you want a clean view of how a serious engagement should work, this guide to methodology for penetration testing is worth reviewing.
Your commercial advantage is simple. You don’t need to build an expensive in-house red team to offer this. You need a reliable way to deliver white label pentesting, fast reporting, and credible findings from testers with OSCP, CEH, and CREST backgrounds.
Actionable Pentesting Recommendations for Your Clients

If you want to use the kill chain well, keep it simple and make it commercial.
Start every client conversation with one question: where would an attacker most likely enter, move, and cause damage in this environment? That shifts the meeting from generic security talk to a focused risk assessment.
A practical client roadmap
- Start with exposure: Review public footprint, remote access, email risk, and internet-facing apps.
- Match tests to likely attack paths: Web app for exploitation risk, internal for lateral movement, social engineering for delivery risk, and cloud testing for modern sprawl.
- Tie findings to compliance: Frame remediation in terms the client already cares about, such as SOC 2, HIPAA, PCI DSS, and ISO 27001 controls.
- Prioritize affordability and speed: Clients don’t want bloated scopes, inflated pricing, or month-long delays.
- Insist on manual validation: A scanner dump is not a client-ready penetration test.
Short, clear reporting matters too. Decision-makers need to understand what the attacker could do, what failed, and what to fix first. Technical teams need enough detail to reproduce and remediate.
Good pentesting reports should help you sell the next security project without sounding like a sales deck.
For MSPs, vCISOs, CPAs, and other resellers, a significant opportunity exists here. Don’t hand security assurance to another vendor. Own the relationship, deliver white label pentesting, and make your clients see you as the partner who can prove defenses work. This guide on penetration testing best practices is a strong next step if you want to tighten your process.
If you want a channel-only partner for affordable, manual pentesting with fast turnaround and certified OSCP, CEH, and CREST testers, talk to MSP Pentesting. We help MSPs, vCISOs, GRC firms, CPAs, and resellers deliver white-labeled pen test, penetration test, and penetration testing services without competing for your clients. Contact us today to learn more.



.avif)
.png)
.png)
.png)

