A client asks a simple question during a quarterly review. “How are we detecting threats on the network in real time?”
If you run an MSP, support a vCISO practice, or advise clients through GRC and compliance work, you need a clean answer. Not a deep engineer answer. A business answer.
Snort is one of those tools you should understand even if you never plan to manage it yourself. It helps you speak credibly about monitoring, compliance, and risk. More importantly, it helps you explain where automated detection ends and where pentest, pen testing, and penetration testing start.
What Is Snort in Plain English for MSPs

Snort is a network intrusion detection system, and it can also work as an intrusion prevention system. In plain English, it watches network traffic and looks for signs of attacks, suspicious behavior, or policy violations.
Snort operates as a digital security guard standing at the network entrance. Traffic passes by. Snort checks that traffic against known patterns and rules. If something looks bad, it can either raise an alert or block the traffic, depending on how it's deployed.
Why MSPs should care
Clients rarely ask for “Snort” by name. They ask for outcomes.
They want to know if someone is trying to break in. They want evidence for SOC 2, HIPAA, PCI DSS, or ISO 27001 conversations. They want reassurance that your stack includes actual monitoring, not just antivirus and good intentions.
If you can explain Snort clearly, you sound like an advisor, not a commodity reseller.
Why Snort still matters
Snort has been around for a long time because it solves a real problem well. It was created in 1998 by Martin Roesch, and in 2009 it was inducted into InfoWorld's Open Source Hall of Fame as one of the “greatest open source software of all time,” which reflects its status as a de facto standard in intrusion detection according to Snort's history on Wikipedia).
Business takeaway: Knowing what is snort helps you frame network monitoring as a managed security service, not just a technical feature.
For an MSP owner, that's useful because mature tools make sales easier. You don't need to invent a story around them. You just need to explain where they fit.
Snort fits well when a client needs network visibility, alerting, and a stronger compliance posture. It does not replace a full risk assessment. It also doesn't replace manual penetration testing. Those gaps matter, and they create room for better service packaging.
How Snort Works as an IDS vs IPS
The most important thing to understand about Snort is this. It can watch, or it can watch and act.
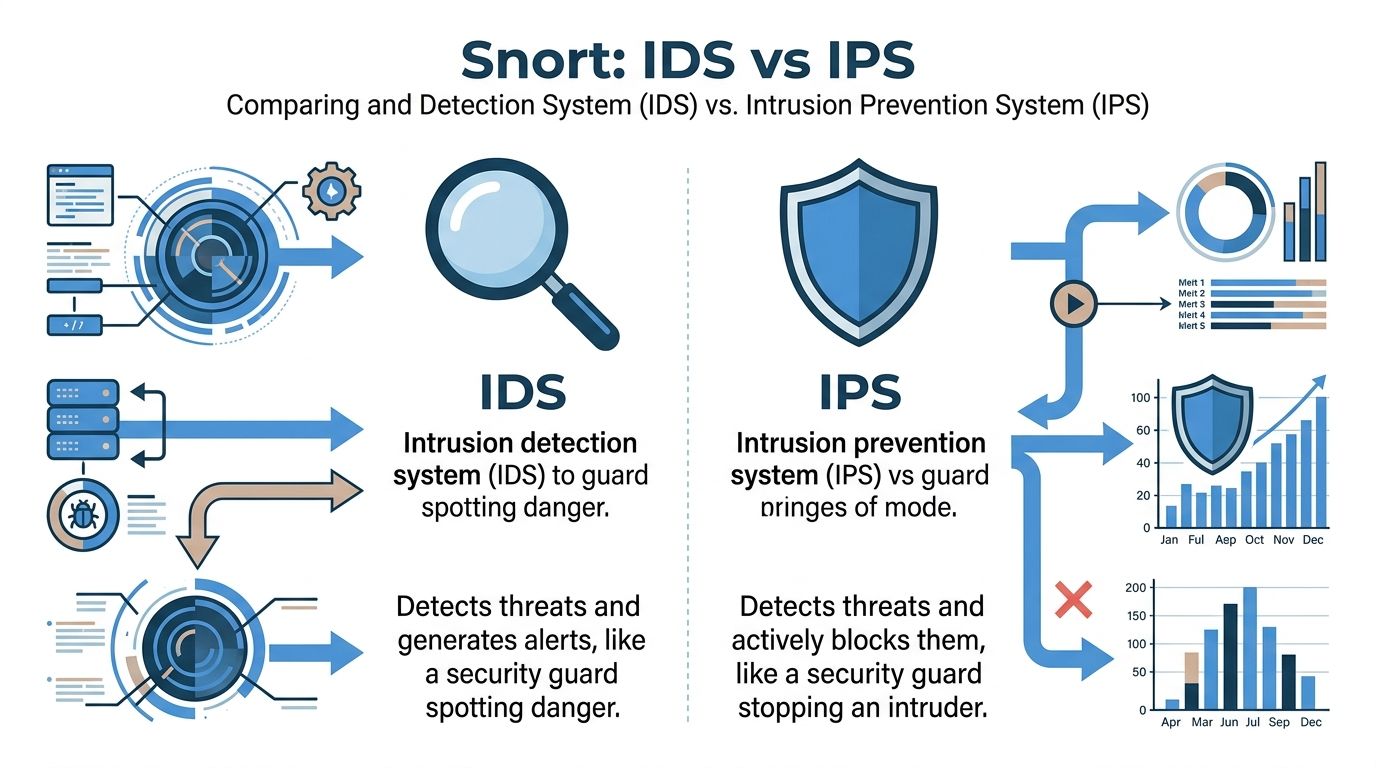
IDS means detect and alert
In IDS mode, Snort inspects traffic and generates alerts when traffic matches a rule. It tells you something bad may be happening, but it doesn't stop the traffic by itself.
That makes IDS easier to deploy in sensitive environments where clients worry about blocking legitimate business traffic. If you're managing a noisy client network or inheriting a messy setup, IDS is often the safer starting point.
IPS means detect and block
In IPS mode, Snort can take action. It can use responses such as drop or block when traffic matches a malicious pattern.
That changes the conversation from “we saw the attack” to “we stopped the attack.” For clients with stronger security requirements, that's a much better story.
The practical difference for resellers
Use this simple comparison in client meetings:
ModeWhat Snort doesBest fitIDSDetects suspicious traffic and alerts your teamClients that want visibility firstIPSDetects suspicious traffic and actively blocks itClients that need stronger automated control
Snort is widely adopted, which helps when you're recommending a known quantity. It has over 4 million downloads and nearly 400,000 registered users, establishing it as the most widely deployed intrusion prevention technology globally according to Forensics Wiki's Snort overview.
IDS is easier to sell first. IPS is easier to justify after you've shown the client what the network actually looks like.
That sequencing matters for margins. Start with monitoring, prove value, then expand into active prevention, compliance support, and eventually pen test or penetration test services to validate whether the controls are working.
Understanding Snort Architecture and Rule Basics
Most MSP owners don't need to write Snort rules from scratch. You do need to understand the moving parts well enough to ask smart questions and spot weak deployments.
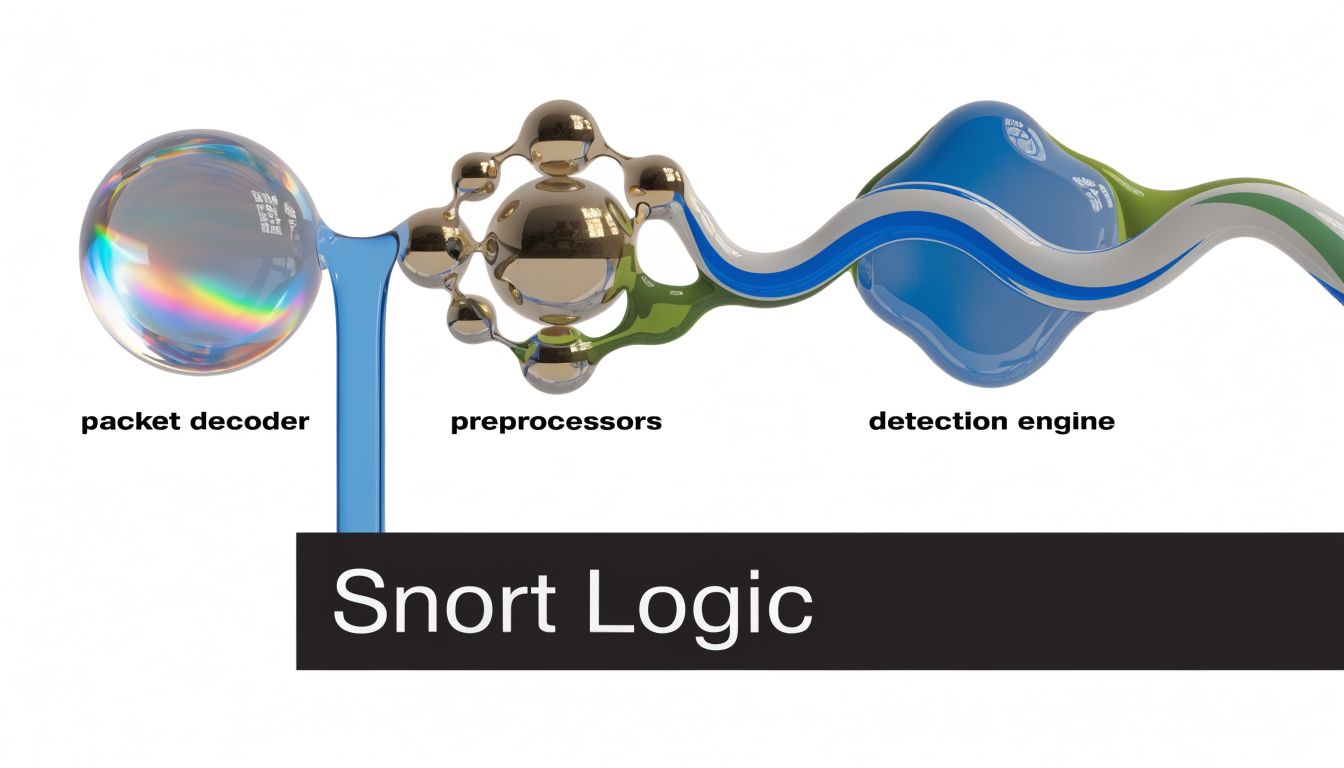
The three parts that matter
Snort's logic is straightforward when you strip away the jargon.
- Packet decoder reads the raw traffic and figures out what kind of packet it is.
- Preprocessors clean up and normalize traffic so Snort can inspect it consistently.
- Detection engine checks traffic against rules and decides whether to alert, log, drop, or block.
That last part is the heart of the product. Snort performs real-time traffic analysis by matching packets against a large library of signatures, and a single drop rule can terminate a malicious session at wire speed, reducing threat dwell time by up to 90% in benchmarked environments according to Snort.org.
What a rule really is
A Snort rule is just an if-then statement.
If traffic looks like X, do Y.
That’s it.
A rule usually looks at a protocol, source, destination, port, direction, and some content or behavior. Then it assigns an action. Alert it. Log it. Drop it. Block it.
For an MSP, the main point isn't syntax. The point is quality. Generic rules catch generic things. They don't automatically reflect the client’s business apps, weird legacy systems, cloud footprint, or approved traffic patterns.
Practical rule: If nobody has tuned the rules to the client environment, don't assume the alerts mean much.
Why architecture matters in a client review
When a client says “we already have monitoring,” your next question should be “what is it looking for?”
That opens a better discussion:
- Are the rules current
- Are they tuned for the environment
- Are alerts reviewed by someone competent
- Is the network design making inspection easier or harder
A weak network design can make any IDS or IPS less effective. If you want a useful companion discussion for clients that need cleaner segmentation and inspection points, this network architecture review is a practical starting point.
Often, MSPs miss an upsell. They sell a security stack, but they don't connect the stack to rule quality, network design, and validation. Clients end up paying for visibility without getting confidence.
Deploying Snort to Meet Client Compliance Needs
Compliance clients don't buy tools. They buy evidence, defensibility, and fewer audit headaches.
Snort helps because it supports continuous monitoring and intrusion detection conversations in a way auditors and security stakeholders understand. That matters for SOC 2, PCI DSS, HIPAA, and broader GRC programs.
Where Snort fits in compliance
For clients using Cisco infrastructure, Snort can sit directly in the environment without forcing a separate appliance conversation. In Cisco Snort IPS for 4000 Series ISRs, the engine runs in a service container and supports compliance goals such as PCI-DSS and SOC 2 through lightweight integration. Cisco states it can sustain 1-5Gbps inspection on an ISR4451 without data plane degradation in that deployment model, as shown in the Cisco 4000 Series ISR Snort datasheet.
That gives you a clean value proposition. Monitoring can be embedded into the infrastructure clients already own.
What auditors and clients want to see
They usually want proof that you can detect suspicious activity, retain logs, and respond consistently.
Snort supports that with:
- Alert visibility that shows known malicious or suspicious traffic was detected
- Log records that help support investigations and audit evidence
- Policy enforcement when deployed in prevention mode
- Operational reporting that strengthens a broader compliance narrative
For clients dealing with financial reporting and control oversight, this overview of Sarbanes-Oxley (SOX) cyber security compliance is useful context because it connects security monitoring to governance and internal control expectations.
The MSP sales angle
If you're only talking about tools, you're stuck in price pressure. If you're talking about audit readiness and risk reduction, you protect margin.
A better pitch is simple. “We help you maintain network visibility that supports your compliance posture, and we validate it with deeper testing where needed.” For SOC 2 engagements, this SOC 2 penetration testing guide fits naturally into that discussion.
Tuning Snort and Recognizing Its Critical Limitations
A default Snort deployment can create noise. Too many alerts, weak prioritization, and generic rules turn a good tool into background clutter.

Tuning matters more than installation
Plenty of MSPs install a detection tool and stop there. That's lazy, and clients feel it when every alert looks urgent.
Useful tuning usually means:
- Reduce false positives by disabling noisy rules that don't fit the client environment
- Prioritize high-risk traffic tied to exposed services, sensitive segments, and business-critical systems
- Align detection with reality so approved applications and expected flows don't flood the queue
Good tuning protects your team from alert fatigue. It also protects your client relationship. Nobody renews happily when the security service creates confusion every week.
Snort has a real limitation
This is the part many “what is snort” articles avoid. Snort is strong at catching traffic that matches known signatures and patterns. It is not magic.
Rule-based systems like Snort are challenged by zero-day and polymorphic threats that don't match existing signatures, creating a detection gap that complex attacks and advanced persistent threats can bypass, as explained in CrowdStrike's discussion of Snort rules and their limits.
Snort is a strong control. It is not a complete security strategy.
That limitation matters because attackers don't politely stick to known patterns. A skilled operator changes payloads, abuses legitimate tools, and finds overlooked paths between systems. That's exactly why manual pentesting, penetration testing, and real pen testing still matter.
Where manual pentesting earns its place
A well-run manual pentest shows what automated controls miss.
That includes:
- Unknown attack paths across internal systems, web apps, and cloud services
- Weak configurations that aren't obvious from packet inspection alone
- Business logic flaws in applications and workflows
- Human-driven evasions that test how a real attacker would move
If you're advising clients on security maturity, don't oversell Snort. Use it where it works best, then recommend manual validation by qualified testers. That's the honest answer, and it's the one that wins trust.
Offer Comprehensive Security with White Labeled Pentesting
If you sell managed security, you need both detection and validation. Snort covers part of the detection story. It does not prove the client is secure.
That gap is where white label pentesting makes sense for an MSP, vCISO, reseller, CPA firm, or GRC provider. You keep the client relationship. You add a high-value service. You don't build an internal penetration testing team from scratch.
A good partner model should be simple:
- Channel-only delivery so the testing firm never competes with you
- Manual pentesting performed by certified testers such as OSCP, CEH, and CREST
- Affordable pricing that works for mid-market compliance clients
- Fast turnaround so reports don't drag on for weeks
- Coverage across environments including internal, external, cloud, web, mobile, and social engineering scenarios
If you're shaping your broader service stack, this guide to Managed IT Security Services is worth a read because it frames how monitoring, response, and advisory services work together.
For MSPs that want to expand without channel conflict, this page on white label penetration testing shows how to add penetration testing under your own brand without slowing down delivery or hurting margin.
The short version is this. Use Snort to monitor. Use a risk assessment to prioritize. Use manual penetration testing to find what automated tools miss.
If you're an MSP, vCISO, reseller, or GRC advisor that needs fast, affordable, channel-only pentest support, MSP Pentesting can help you deliver white-labeled manual pentesting without competing for your clients. Contact us today to strengthen your security offering, improve compliance outcomes, and give clients a better answer than “we installed a tool.”



.avif)
.png)
.png)
.png)

