In networking, think of a DMZ as a secure lobby for your digital office. It’s a special, safe area that sits between the public internet and your private internal network. This is where you put things that need to be public, like your company's website, so visitors can access them without getting keys to the whole building.
This setup is crucial. If someone breaks into a server in the DMZ, they are still stuck in that lobby, far away from your company’s sensitive data and internal systems.
What is a DMZ for Network Security?
A Demilitarized Zone, or DMZ, is your network’s frontline defense. It's a small, isolated network segment where you place any service that needs to be public-facing, like web servers, email servers, or DNS servers. This separation is a core part of a strong security plan.
The goal is simple: if a public server gets hacked, the attacker is trapped in the DMZ. They can't easily jump into your trusted internal network where all your important client data, employee workstations, and business systems are stored. This separation is fundamental to building a secure environment.
To understand a DMZ, it helps to know about the bigger idea of Network Segmentation. A DMZ is just a very common and effective way to use that strategy. For Managed Service Providers (MSPs) and vCISOs, setting up a DMZ for clients is essential for creating a defensible architecture that auditors and clients can trust.
A properly segmented DMZ is also a basic requirement for many compliance frameworks. It's a must-have for audits like SOC 2, PCI DSS, and HIPAA because it clearly shows you're separating your networks to protect sensitive information. This controlled isolation is exactly what our penetration testing teams are hired to check.
During a pen test, our OSCP, CEH, and CREST certified experts try to break through the DMZ's boundaries. They look for misconfigurations that a hacker could use to get from the DMZ into the private network. Finding these flaws with an affordable and fast manual pentesting service is key. As a channel-only partner, we provide these white label pentesting services to help you give that assurance to your clients.
Understand DMZ Architecture and Components
When you build a DMZ, the best practice is using a dual-firewall design. This setup creates a true buffer zone by placing the DMZ between two separate firewalls. Think of it as a layered defense. If a hacker gets past the first firewall, they only land in the DMZ. They are then blocked by a second firewall before they can even get close to your internal network.
This architecture creates a vital security layer between the untrusted internet and your trusted private network. It’s the industry standard for a reason.
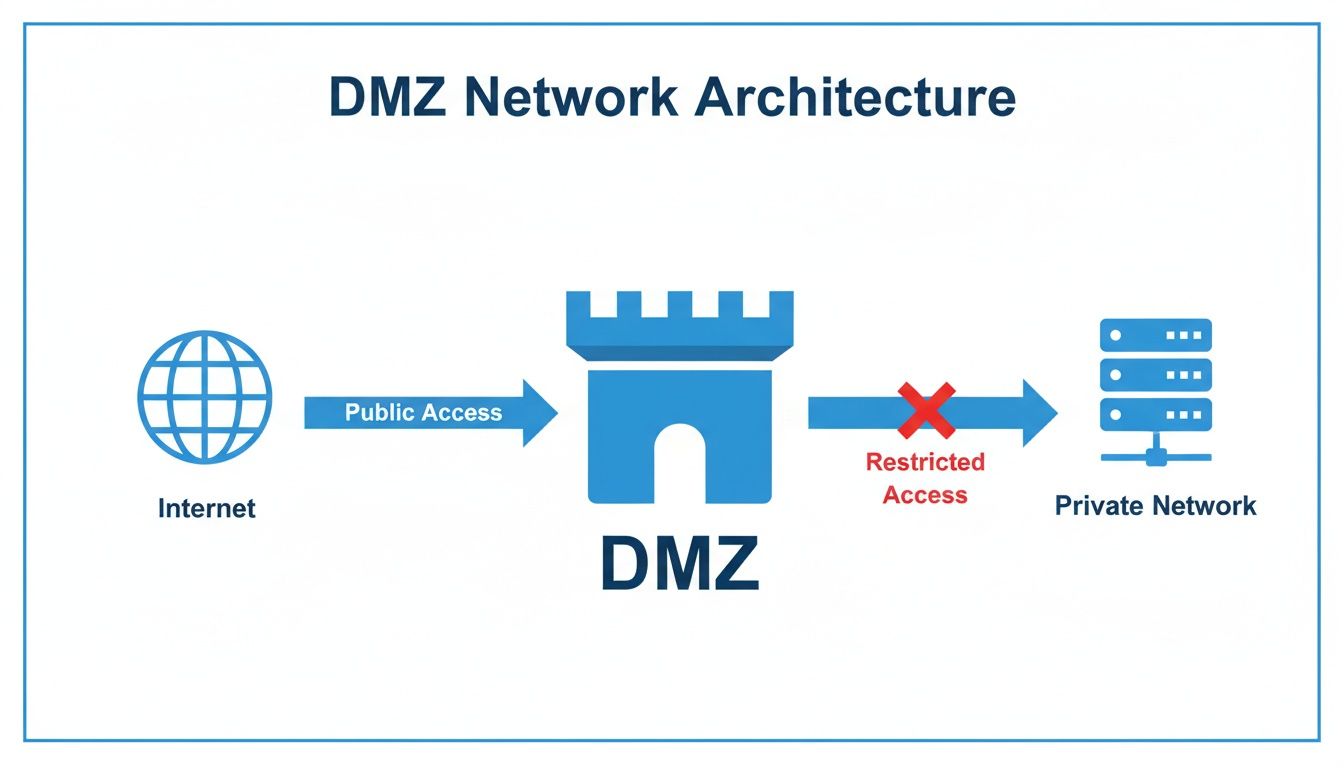
As you can see, internet traffic is allowed to the DMZ, but any direct, uninitiated traffic from the DMZ to the private network is completely blocked. This isolation is what makes the whole concept work. The components work together to create a strong, layered security posture. Let’s break down what makes it work.
- External Firewall: This is your front door. It sits between the internet and your DMZ. Its only job is to allow specific traffic—like web traffic on port 443—to reach your public servers. Everything else is blocked.
- DMZ Servers: These are your public-facing systems, like web servers or email gateways. They should be hardened to do only their specific job and nothing else.
- Internal Firewall: This is the real hero. It separates the DMZ from your internal network and should operate on a strict "deny-all" policy by default. Its purpose is to stop any unsolicited traffic from the DMZ from ever reaching your internal assets.
This same logic applies directly to cloud environments. In AWS or Azure, you create a DMZ using security groups and network ACLs to isolate public subnets from private ones. The tools are different, but the concept is the same. This is where a manual pentesting engagement is so important. A detailed network architecture review is the only way to be sure you haven't left a door open.
How DMZ Firewall Rules and Traffic Flow Work
A DMZ is only as good as the firewall rules that protect it. Think of the firewall as a bouncer and the rules as the guest list. Without a strict list, anyone can get in. Properly set up rules are what truly define a DMZ in networking and give it the power to protect your client’s valuable assets.
For any MSP or vCISO building a network, there are three absolute rules for traffic flow. Getting these wrong is like leaving the back door of a bank vault wide open. The whole point is to control access with precision by setting specific "allow" and "deny" rules on your firewalls.
You must enforce these core principles:
Internet to DMZ: Traffic from the public internet should only be allowed to reach specific services in the DMZ, like a web server on port 443. It should never be allowed to pass straight through the DMZ into the internal network.
Internal to DMZ: Your internal private network can usually access the internet. But any connections started from the internal network to the DMZ need to be tightly restricted and watched closely.
DMZ to Internal: This is the most important one. Traffic from the DMZ must be blocked from starting any connections to the internal network. This single rule is what stops a hacked web server from moving laterally and attacking your internal database or domain controller.
To add another layer of security, you'll almost always see Network Address Translation (NAT) used. NAT hides the real IP address structure of your internal network. This makes it much harder for a hacker who has compromised the DMZ to know what to target next.
While firewalls are the foundation, you can strengthen your defenses even more. Learning how to implement Zero Trust Security builds on these principles of strict access control. You can also see how these rules fit into a bigger strategy by checking out these network segmentation best practices. Misconfiguring these rules creates huge security holes, which is what our penetration testing team gets paid to find.
Uncover Common DMZ Misconfigurations with a Pentest

In theory, a DMZ is a great security layer. In the real world, it’s where we find some of the most critical mistakes. This is where our value as a pentest partner becomes obvious for you—the MSP or vCISO. Our OSCP, CEH, and CREST certified pentesters see the same dangerous flaws again and again.
The most common and dangerous misconfiguration is the "allow any/any" firewall rule. Someone puts it in place "temporarily" to fix an issue, and then forgets about it. This one rule turns your firewall into a simple router, destroying the isolation that helps define a DMZ in networking. An "any/any" rule lets a hacker who gets into a DMZ server connect to anything on your internal network, making the DMZ worthless.
Another classic mistake is letting servers in the DMZ start connections back to the internal network. This gives hackers a direct path for lateral movement. They can compromise a public web server and then use it to attack sensitive internal systems like domain controllers. Finding this exact error is what a professional penetration test is for.
Our manual pentesting experts will simulate this attack path, trying to pivot from the DMZ to the internal network to give you proof of the vulnerability. Our penetration testing engagements consistently reveal the same patterns. Here are the top flaws we uncover:
- Improper Asset Placement: Sensitive systems like domain controllers or databases full of PCI DSS data sitting right in the DMZ.
- Unpatched Systems: Forgetting to patch DMZ servers, leaving them open to well-known exploits.
- Lack of Egress Filtering: Letting DMZ servers connect anywhere on the internet, which allows attackers to download more malware or send stolen data out.
These aren't just minor issues for a compliance report; they're active threats waiting to be used. Our fast, white label pentesting lets you resell our findings under your own brand, strengthening your security offerings for frameworks like SOC 2 and ISO 27001. This is why an affordable risk assessment and pen test is so valuable.
Why a DMZ Penetration Test is a Business Requirement
Just setting up a DMZ isn’t enough. You have to prove it can withstand an attack, and that’s where a penetration test becomes non-negotiable for any serious security program. This is a business-critical step that separates truly secure MSPs from those just hoping for the best.
Compliance frameworks like SOC 2, HIPAA, and PCI DSS don't just take your word for it. They often require routine pentesting to validate your security controls. An auditor wants to see hard proof that your defenses work, and a pen test report provides that proof.
A penetration test is a simulated, real-world attack designed to answer one crucial question: "If our public-facing web server gets hacked, can an attacker get to our internal network?" This is where we come in. As a channel-only company, we never compete with our MSP or vCISO clients. We provide fast, affordable, and thorough manual pentesting designed for resellers.
Automated scanners can miss subtle flaws that a creative human attacker can exploit. Our OSCP, CEH, and CREST certified experts are trained to find the dangerous issues scanners can't, like a tricky firewall rule that allows a pivot right into sensitive data. A solid pen test report is a powerful business asset that serves two key purposes for you:
- Evidence for Auditors: It gives you undeniable proof for auditors handling ISO 27001 and HIPAA that your security controls are tested and working.
- A Key Sales Differentiator: It lets you, the reseller, prove the strength of your security stack, building massive trust with your clients.
Our white label pentesting model means you deliver these valuable findings under your own brand, making your client relationships stronger. A detailed risk assessment is a great start, but a full pen test is how you validate that your defenses will hold up. You can dig deeper into our method in our guide to network penetration testing.
Frequently Asked Questions About DMZ Networking
As an MSP or vCISO, your clients look to you for clear answers about their security. Here’s how to answer the most common DMZ questions with confidence.
Is a DMZ Still Relevant in a Cloud Environment?
Yes, absolutely. The tools have changed from physical firewalls to virtual ones, but the core principle that helps define a DMZ in networking is more important than ever in the cloud.
In AWS or Azure, you create a DMZ with virtual private clouds (VPCs), subnets, and security groups. The goal is the same: build an isolated zone for public servers that’s completely walled off from your critical backend systems. Cloud misconfigurations are a huge risk, making a regular risk assessment and penetration test essential to ensure your virtual DMZ is secure.
What Is the Difference Between a DMZ and a Firewall?
This question is common, but the answer is simple. A firewall is a tool. A DMZ is a network design you build using that tool.
Think of it this way:
- A firewall is the bouncer at the door, checking IDs based on a strict guest list.
- A DMZ is the guarded lobby between the street and the private back office. It has one bouncer at the front door (the external firewall) and another at the door to the office (the internal firewall).
You need both working together to create a secure environment.
How Does a DMZ Help With SOC 2 or PCI DSS Compliance?
For any client facing an audit, a properly implemented and validated DMZ is a huge help in the compliance process.
With PCI DSS, a DMZ can drastically shrink your audit scope. By proving that all systems handling cardholder data live in their own segmented network, you can argue to auditors that the rest of the client's network is out of scope. This saves everyone a lot of time and money.
For SOC 2, a solid DMZ is your proof for the Security Trust Services Criterion (TSC). It's hard evidence that you have strong access controls and risk mitigation strategies in place. A clean penetration testing report focused on the DMZ is the best way to show an auditor your controls are effective. This is why our fast, affordable manual pentesting is so critical for MSPs guiding clients through the compliance maze.
At MSP Pentesting, we empower our partners by providing the expert validation needed to prove security controls are working. Our channel-only model ensures we are always your partner, never your competitor. Contact us today to see how our fast, affordable, and certified pentesting services can strengthen your security offerings.



.avif)
.png)
.png)
.png)

