A client calls because their auditor keeps circling wireless access, remote access, and network segmentation. They want SOC 2 evidence. They want HIPAA confidence. They want it fixed fast, and they assume their Wi-Fi is already “secure enough” because it has a password.
That’s where a lot of MSPs get burned.
If you support business networks, you need to understand extensible authentication protocol EAP. Not as trivia. Not as a vendor checkbox. You need to understand it because EAP sits in the middle of how users and devices get onto Wi-Fi, wired networks, and VPNs. If it’s configured well, it raises the bar for attackers. If it’s configured badly, it gives attackers a clean path to credentials, internal access, and audit findings.
Why EAP Matters for Your MSP and Your Clients
A common MSP scenario looks like this. Your client needs stronger access control before a SOC 2, HIPAA, PCI DSS, or ISO 27001 review. They’ve got staff on laptops, phones, guest devices, maybe a warehouse switch stack, and a mix of managed and unmanaged endpoints. Shared passwords aren’t going to cut it.

That’s where EAP matters. RFC 3748 formally defined EAP in June 2004 as an authentication framework supporting multiple methods and established it as the standard for network access control in protocols like IEEE 802.1X. That matters to your business because EAP is not just a Wi-Fi thing. It also shows up in wired access control and VPN authentication.
Why busy MSP owners should care
You’re not selling a protocol. You’re selling reduced risk, cleaner compliance evidence, and fewer bad surprises during a client security review.
Here’s the business angle:
- Better client protection: EAP helps replace weak access controls with identity-based authentication for users and devices.
- Stronger compliance story: Auditors want proof that access is controlled, not just assumed.
- Higher-value services: A client who understands network access risk is far more likely to buy a risk assessment, a pen test, or ongoing security hardening.
- Less blame later: If a rogue device lands on a client network through weak 802.1X or sloppy certificate validation, your team will be answering uncomfortable questions.
Practical rule: If your client uses enterprise Wi-Fi, NAC, or remote access, EAP belongs in the scope of every serious pentest and penetration testing conversation.
Where EAP becomes a reseller opportunity
Most clients don’t know whether they’re using EAP-TLS, PEAP, or something weaker. They just know users connect and internet works. That gap is your opportunity as an MSP, vCISO, GRC advisor, or compliance-focused reseller.
When you can explain what protects client access and what doesn’t, you stop sounding like a generalist. You sound like the person who knows how attackers get in.
Understanding the EAP Authentication Framework
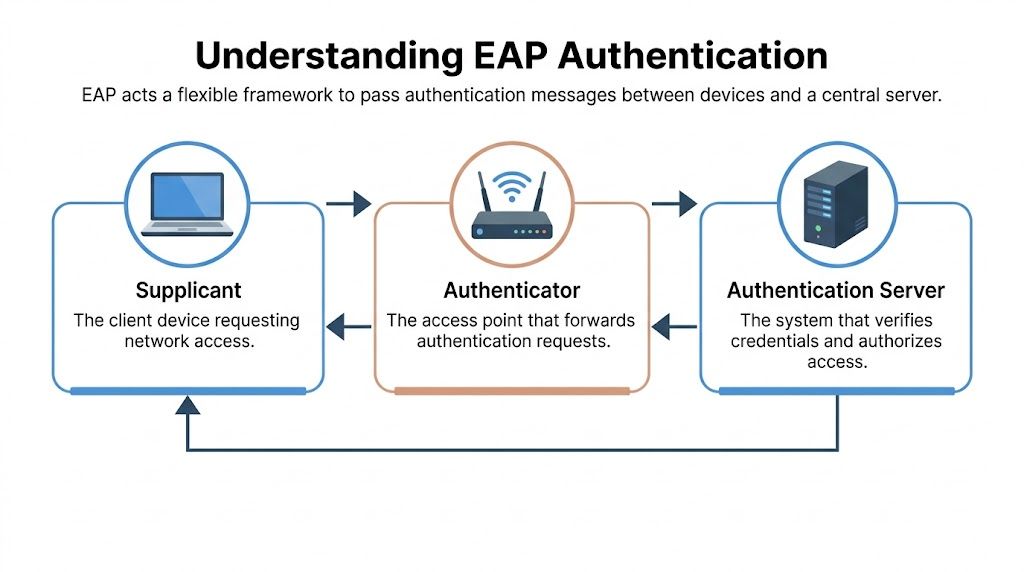
EAP makes more sense if you stop thinking of it as a single login method. It’s a framework that carries authentication messages between the device asking for access and the system making the decision.
EAP functions much like a bouncer at a private event. The bouncer doesn’t personally verify every badge, passport, or credential. The bouncer checks who’s asking, passes the details to the right authority, then enforces the answer. That’s EAP.
The three parts that matter
There are three players in a normal EAP flow:
- Supplicant: The device trying to connect, like a laptop or phone
- Authenticator: The gatekeeper, like a switch or wireless access point
- Authentication server: Usually a RADIUS server that validates identity and returns allow or deny
The supplicant asks for access. The authenticator forwards the request. The authentication server decides whether the credentials, certificates, or other method checks out. If the answer is yes, the port or wireless session opens.
Why this matters in real environments
This is why EAP configuration mistakes are dangerous. A problem might live on the endpoint, on the access point, or on the RADIUS side. If your team only checks one layer, you miss the attack path.
For MSPs doing architecture and security reviews, this is exactly why a network architecture review has value before or alongside a penetration test. If the trust flow is messy, the client is already behind.
Most EAP failures aren’t dramatic. They’re quiet configuration mistakes that sit there until someone with the right toolset abuses them.
EAP is flexible, which is both good and bad
EAP supports many different methods. That flexibility is useful because clients have different device fleets, identity systems, and operational limits. It’s also why weak deployments happen. Teams choose what’s easy, not what’s strong.
That’s where identity hygiene matters too. If a client still leans on passwords inside tunneled methods, they need stronger user-side controls as well. Nutmeg Technologies has a solid guide on best practices for Multi-Factor Authentication (MFA) that complements EAP hardening well, especially for remote access and identity-heavy environments.
Comparing Popular EAP Methods for Network Security
Not all EAP methods deserve the same trust. Some are strong enough for regulated environments. Some are acceptable in limited cases. Some should be retired.
EAP has secured billions of network connections worldwide and underpins authentication in up to 90% of corporate wireless traffic, with over 40 registered methods. That scale is exactly why MSPs need to know which methods are worth recommending.
The short version
If you manage business networks, EAP-TLS should be your default recommendation when the client can support certificates. If they can’t, you need to understand the tradeoffs before you settle for easier options.
Common EAP Methods at a Glance
EAP MethodAuthentication MethodSecurity StrengthBest ForEAP-TLSMutual client and server certificates over TLSStrongest option in this groupManaged device fleets, high-security environments, regulated clientsPEAPTLS tunnel with inner authentication, often username and passwordGood if configured correctly, weaker than certificate-first approachesFaster deployment, Windows-heavy environments, clients without full PKI maturityEAP-TTLSTLS tunnel with flexible inner authentication methodsUseful but depends heavily on inner method and configuration qualityMixed environments with varied backend requirementsEAP-FASTPAC-based secure tunnelingCan work, but provisioning and handling need careCisco-leaning environments and specific legacy deployments
EAP-TLS is the right answer most of the time
EAP-TLS uses mutual certificate-based authentication. That means both sides prove who they are using certificates, not just usernames and passwords. In practice, this is the cleanest answer for clients that care about SOC 2, HIPAA, or mature ISO 27001 controls.
It’s also the one I trust most because it removes password theft from the core authentication path. If an MSP has MDM, certificate management, and a reasonably controlled device fleet, there’s no good reason to settle for weaker methods.
If the client can manage certificates, stop debating and move to EAP-TLS.
PEAP is common, but common isn’t the same as safe
PEAP is widely deployed because it’s easier to roll out. The tunnel helps, but many environments still rely on password-based inner authentication. That means the design is only as strong as certificate validation, password policy, endpoint configuration, and the team that maintains it.
MSPs often make poor assumptions. They think “encrypted tunnel” means “problem solved.” It doesn’t.
EAP-TTLS is flexible, which means you need discipline
EAP-TTLS can fit mixed environments and legacy backend requirements. That flexibility is useful when you’re dealing with weird client realities. It also creates more chances to make a bad design choice inside the tunnel.
If your GRC or vCISO work includes advising on risk assessment priorities, TTLS usually deserves a deeper review than the client expects.
EAP-FAST solves some deployment pain, but watch the details
EAP-FAST avoids full client certificate dependency by using a Protected Access Credential. That can make it attractive in certain environments, especially where legacy design choices already exist. But “easier than PKI” is not the same as “safe by default.”
When you see EAP-FAST, don’t assume the client understands PAC handling or server trust well enough. Check it.
How We Conduct a Penetration Test on EAP
Automated scanners won’t tell you whether a user device will trust a rogue authentication server. They won’t stand up a believable fake access point, test downgrade paths, or validate whether the endpoint enforces certificate checks. That’s why EAP testing needs manual pentesting.

What a real EAP pen test looks for
A proper penetration test on EAP examines how the whole authentication chain behaves under attack, not just whether the service answers.
We focus on issues like:
- Certificate validation failures: If the supplicant doesn’t properly validate server trust, the client may connect to an attacker-controlled system.
- Rogue access point exposure: A fake wireless network can bait devices into disclosing credentials or trusting the wrong endpoint.
- Weak tunneled methods: Password-based inner authentication can create openings that don’t exist in certificate-first designs.
- Policy drift across devices: One managed profile may be secure while another device group is missing a critical trust setting.
A good example comes from Huntress. They note that if a supplicant doesn’t properly check a Certificate Revocation List, a pentester can use a rogue certificate on an Evil Twin access point to perform a man-in-the-middle attack. You can review that risk in their writeup on EAP certificate validation flaws and Evil Twin attacks.
Why certifications matter during testing
This work is not checklist work. A strong tester has to think through trust relationships, endpoint behavior, wireless exposure, and identity flow. That’s why experienced OSCP, CEH, and CREST certified pentesters are useful here. They know how to chain findings instead of reporting them as isolated trivia.
A weak tester says, “802.1X is enabled.”
A strong tester asks better questions:
- Will the endpoint reject a fake server certificate?
- Can a rogue AP trigger user interaction or silent trust?
- Are inner methods exposing credentials to offline cracking risk?
- Does the client have one bad profile among many good ones?
Field advice: If your pentest report never mentions supplicant behavior, certificate validation, or rogue infrastructure testing, the EAP portion probably wasn’t tested deeply enough.
Where wireless pentesting fits
For many clients, the fastest way to prove EAP strength or weakness is targeted WiFi pentesting for enterprise networks. That’s where you validate whether the actual deployment matches the clean diagram in the design document.
This is also where penetration testing creates direct business value for MSPs. It turns abstract network security claims into evidence your client can act on.
Securing Networks with EAP for Your Clients
Most EAP problems are self-inflicted. They come from old methods left enabled, rushed onboarding, or devices that don’t validate what they should. Fixing that doesn’t require magic. It requires discipline.
One stat should get your attention. Portnox states that 60% of network breaches involve weak or misconfigured authentication, and legacy methods like EAP-MD5 are still found in production. If you’re responsible for client security, you should assume drift and test for it.
The no-fluff EAP hardening checklist
Use this as a baseline:
- Default to EAP-TLS: If the client manages devices, go certificate-based first.
- Kill weak methods: Remove EAP-MD5 and other legacy options from production.
- Enforce certificate validation: Don’t let endpoints trust any server that looks close enough.
- Standardize profiles: Push consistent settings through MDM, GPO, or equivalent controls.
- Separate managed from unmanaged access: Don’t force one policy model onto every device type.
- Review wired access too: 802.1X on switches deserves the same scrutiny as wireless access.
- Test after changes: A config pushed at scale can break security as easily as it can improve it.
Tie every control to business outcomes
Clients don’t buy EAP because the acronym sounds impressive. They buy outcomes.
Those outcomes include:
- Cleaner audit evidence for SOC 2, HIPAA, PCI DSS, and ISO 27001
- Reduced credential theft risk on business-critical networks
- Better network segmentation enforcement on wired and wireless access
- A stronger managed security offering for the MSP or reseller
If you want a broader security validation path around these controls, a network penetration testing approach for internal and external exposure helps confirm whether your access controls hold up under attack.
Don’t mark EAP as done because users can connect. Mark it as done when the wrong user, wrong device, and wrong certificate can’t.
Where MSPs often miss the sale
A lot of providers treat this as backend plumbing. That’s a mistake. EAP review is a service conversation.
If you support clients in regulated industries, EAP hardening can lead naturally into a risk assessment, penetration testing, policy remediation, wireless segmentation review, and ongoing compliance support. That’s not upselling fluff. That’s responsible advising.
Partner with Us for Affordable EAP Pentesting
EAP is one of those controls that looks solid until someone tests it properly. A client may have enterprise Wi-Fi, RADIUS, certificates, and polished policies, then still fail on endpoint trust, weak methods, or a rogue AP scenario.
That’s why MSPs, vCISOs, GRC firms, CPAs, and resellers need a testing partner that understands the business side and the technical side. Our team delivers affordable, manual pentesting with fast turnaround, performed by OSCP, CEH, and CREST certified pentesters. We work white label, we stay channel-only, and we never compete with our partners for downstream services.
If you’re evaluating vendors, this outside perspective on top penetration testing companies can help frame what to look for. Then compare that list to what matters for channel partners: affordability, manual testing depth, speed, and no channel conflict.
If you need a white label partner for fast, affordable, manual pentesting, talk to MSP Pentesting. We help MSPs and resellers deliver real pen test, penetration test, and penetration testing services without long lead times, inflated pricing, or channel conflict.



.avif)
.png)
.png)
.png)

