A client is in the middle of a SOC 2 review. The auditor asks who controls private keys, how certificates are rotated, and whether anyone has validated the trust chain against real-world attack paths. Your team knows the firewall stack, the backup platform, and the EDR console. Then the conversation lands on encryption, and things get uncomfortable fast.
That happens more than most MSPs want to admit.
Public key and private key encryption sounds academic until it becomes an audit finding, an outage, or a breach root cause. If you're an MSP, vCISO, GRC advisor, CPA firm, or security reseller, you need more than a surface-level answer. You need to know where encryption fails in practice, what to check during a risk assessment, and how to prove controls work under penetration testing.
Why Your MSP Needs to Understand Encryption
A lot of providers still treat encryption like a checkbox. Turn on HTTPS, install a certificate, move on. That approach falls apart the second a client asks for evidence that key handling is secure across cloud apps, mobile endpoints, and vendor integrations.
Auditors don't care that a dashboard says "encrypted." They care who can access the private key, how trust is established, and whether an attacker could abuse a weak implementation. That affects SOC 2, HIPAA, PCI DSS, and ISO 27001 conversations immediately.
One useful way to frame the issue is as part of the client's broader overall security posture. Encryption doesn't live on an island. It's tied to identity, access, certificate management, endpoint protection, and incident response.
Where MSPs usually get stuck
Many can explain encryption at a high level. Fewer can answer questions like these without scrambling:
- Key ownership: Who controls the private key in a hosted app or shared environment?
- Certificate trust: Has anyone verified the certificate chain and revocation path?
- Operational reality: Are keys protected in a vault or sitting where admins and scripts can reach them too easily?
- Client reporting: Can you explain the business impact in plain English to a client, auditor, or board?
If those answers aren't clear, your client sees risk and your team looks reactive.
Encryption isn't just a control. It's an attack surface.
This is why layered validation matters. If you want a plain-English way to explain that to clients, our breakdown of security in layers helps connect cryptography to the rest of the environment.
Public Key vs Private Key Explained
Think of a mailbox.
Anyone can walk up and drop a letter through the slot. That's the public key. It's meant to be shared. But only the owner with the physical key can open the box and read what's inside. That's the private key.
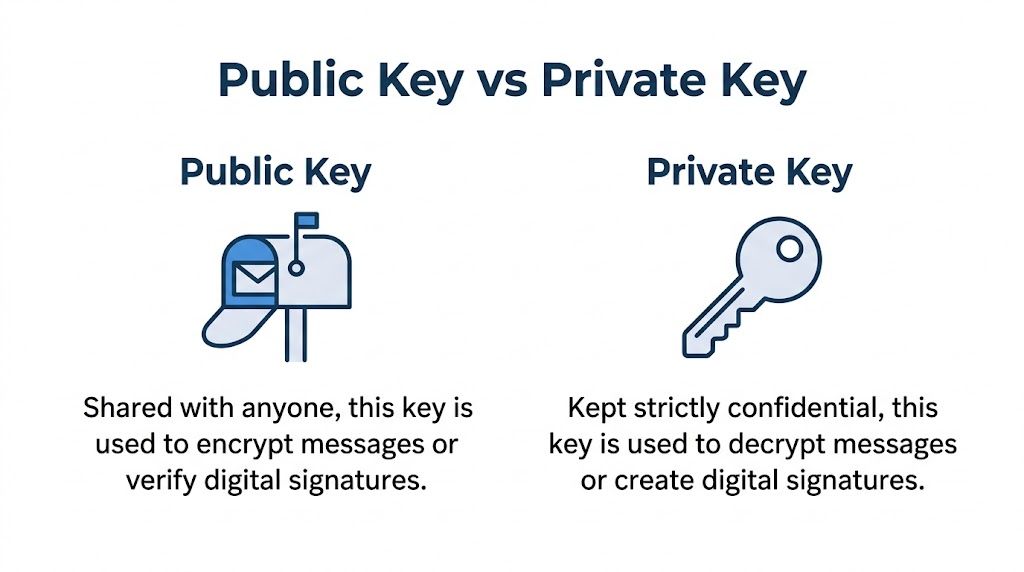
What the two keys actually do
In asymmetric cryptography, you have a matched pair:
- Public key: Shared openly. Used to encrypt data or verify a signature.
- Private key: Kept secret. Used to decrypt data or create a signature.
That setup solved a major problem in cryptography. IBM's history of cryptography notes that the breakthrough came in 1976, when Whitfield Diffie and Martin Hellman published New Directions in Cryptography, and 1977 brought RSA from Ron Rivest, Adi Shamir, and Leonard Adleman, which shaped the modern model still used today in many systems and workflows (IBM cryptography history).
Why this was a big deal
Before public key systems, secure communication usually depended on a single shared secret. Both sides needed the same key before they could talk securely. That's symmetric encryption.
That sounds simple, but it creates a nasty operational problem. How do you safely share the secret key in the first place?
Public key encryption changed that. You can publish the public key to the world. Anyone can use it to protect a message meant for you. Only your private key can decrypt it.
Here’s the simple comparison:
MethodKeys usedMain challengeSymmetric encryptionOne shared keySharing the key securelyPublic key and private key encryptionTwo related keysProtecting the private key
For MSPs, this matters because clients don't buy theory. They buy systems that need to exchange data safely across browsers, apps, APIs, and devices.
Encryption Signing and Key Exchange Flows
Public key systems do three jobs in real environments. If your team mixes them up, your recommendations get sloppy and your pen test scope misses important checks.
Encryption protects confidentiality
This is the easiest flow to understand.
A sender takes the recipient's public key and uses it to encrypt data. Only the matching private key can decrypt it. That protects the contents from anyone who intercepts the traffic.
Used correctly, this is what gives clients confidence that sensitive traffic isn't readable by random systems sitting in the middle.
Digital signatures prove identity and integrity
Signing works in the opposite direction.
The sender uses their private key to sign data. The receiver uses the sender's public key to verify the signature. If verification succeeds, the receiver gains confidence that the message really came from that sender and wasn't altered on the way.
That distinction matters. Encryption hides content. Signatures prove who sent it and whether it changed.
Practical rule: If a client thinks encryption alone proves sender identity, fix that misunderstanding immediately.
Key exchange makes real sessions practical
Most production systems don't use asymmetric cryptography for everything. It's too heavy for bulk traffic. Instead, they use it to establish a session safely, then switch to faster symmetric encryption for the actual data stream.
That happens during TLS handshakes and similar workflows. The public/private key system helps set up trust and establish a temporary session secret. Then the connection uses that session key for speed.
For an MSP, the takeaway is simple:
- Encryption keeps data secret.
- Signing proves authenticity.
- Key exchange creates a secure session efficiently.
If you're reviewing a client environment, ask which of those functions is in play. A web app cert issue, a code-signing problem, and a bad key exchange implementation are not the same finding. They create different business risks, and they need different remediation steps.
Understanding Algorithms and PKI for Compliance
Most client environments eventually land on two names. RSA and ECC. You don't need a math degree to advise on them, but you do need to understand the tradeoff.
RSA versus ECC in the real world
RSA is the old standard. It's familiar, widely supported, and still common in enterprise environments. A lot of legacy systems still run on it because it works and admins know it.
ECC is usually the better choice for modern deployments where performance matters. For enterprise pentesting, RSA-2048 keys are common, but expert pentesters recommend ECC keys like P-256 because they deliver a 30-50x speed increase in operations, reducing CPU overhead from 10-20ms per RSA signature to under 1ms in ECC on constrained devices (Kiteworks on public vs private key encryption).
That matters for:
- Mobile apps: Less overhead on phones and tablets
- IoT deployments: Better fit for low-power devices
- Busy web services: Faster operations without weakening security goals
- Compliance projects: Easier to defend modern choices in SOC 2 and audit reviews
PKI is the trust system
A public key by itself doesn't prove identity. Anyone can generate one.
Public Key Infrastructure, or PKI, is the governance layer that ties keys to identities using digital certificates. That's how a browser decides whether a public key belongs to the server it's connecting to. It also supports certificate issuance, renewal, and revocation.
Without PKI, you don't have trust. You just have keys.
What compliance teams should care about
When you're advising a client under PCI DSS, ISO 27001, or SOC 2, the discussion shouldn't stop at "encryption enabled." It should include:
- Certificate validity: Are certificates current and issued properly?
- Algorithm choice: Is the client stuck on old defaults when better options exist?
- Key storage: Who can access the private key and under what controls?
- Lifecycle management: Can the organization rotate and replace keys cleanly?
If you need a stronger map for evidence collection around cryptographic controls, use this guide to SOC 2 security controls as a practical reference.
How We Pentest Encryption for Your Clients
Reading docs and checking a certificate in a browser isn't enough. Penetration testing is where you find out whether encryption is protecting the client or just making them feel better.
What manual pentesting catches
Automated scanners are useful, but they don't think like an attacker. They also miss ugly implementation details that cause real incidents.
Real-world penetration tests show the gap clearly. CREST reports from 2025 indicated a 40% success rate in extracting private keys via side-channel attacks on cloud VMs, which is exactly why manual testing matters beyond configuration review (PreVeil on public and private key risks).
That aligns with what experienced testers already know. The crypto math is often solid. The implementation is the weak point.
Common failures in client environments
Here are the issues a strong penetration test should actively hunt for:
- Poor private key storage: Keys left in accessible file paths, shared servers, or weakly protected secrets stores
- Broken certificate validation: Apps that trust bad chains or skip proper verification
- Weak cryptographic choices: Legacy ciphers, old protocol support, or bad defaults carried forward for years
- Signing mistakes: Trusting unsigned or improperly signed content
- Deployment drift: One environment is fixed, another still exposes the old behavior
Some of these issues show up in web apps. Others appear in mobile, cloud, or internal services. That's why checkbox testing fails. Encryption problems cross boundaries.
A client can pass a config scan and still have a private key exposure problem.
What good testing looks like
A serious pen test around encryption should include both technical validation and business context. That means testers need to answer:
Testing areaWhat mattersCertificate checksIs the chain trusted and enforced correctly?Key handlingCan attackers reach or extract the private key?Protocol reviewAre modern secure settings actually deployed?Application logicDoes the app validate signatures and identities correctly?
For SOC 2 clients, this matters because a control isn't strong just because a policy says it exists. Auditors and buyers want proof the control works under realistic conditions.
The right team also has to communicate findings clearly. A vCISO needs executive risk language. An engineer needs reproduction details. A reseller needs a report they can stand behind without embarrassment.
That is why manual pentesting, pen testing, and targeted penetration testing are worth paying for. Fast reports and low pricing matter, but not if the methodology is weak.
Key Management Best Practices for MSPs
If you want fewer audit surprises and fewer ugly remediation calls, tighten key management first. Most encryption failures aren't about impossible math. They're about bad handling.

The controls worth enforcing
Use these as your baseline with clients:
- Generate keys in controlled systems: Don't allow ad hoc key creation on random admin workstations.
- Protect private keys hard: Use HSMs or secure vaulting where the risk justifies it.
- Automate certificate lifecycle tasks: Manual renewals create preventable outages and last-minute panic.
- Separate duties: The person who administers systems shouldn't automatically control every key.
- Rotate with purpose: Replacement should be planned, documented, and tested.
Why forward secrecy matters
The market moved for a reason. A 2018 empirical study found that after the 2013 Snowden revelations, TLS connections shifted sharply away from RSA and toward ECDHE, with RSA dropping to about 10% and ECDHE rising to roughly 90% of negotiated connections in the second half of 2013, highlighting the industry's push toward forward secrecy (empirical study on the societal impact of public key cryptography).
For MSPs, the lesson is practical. If a long-term private key is ever compromised, forward secrecy helps protect past sessions. That's a strong control to recommend, especially for clients with regulated data.
Good key management reduces both breach impact and audit pain.
Build this into your client strategy
Key management shouldn't be a once-a-year project. It should sit inside your client's operating model, alongside access reviews, logging, and change control.
If you're building a stronger long-term architecture, zero trust principles fit naturally here. This guide on how to implement zero trust security is a useful companion when you're tying identity, certificates, and least privilege together.
Partner With Us for Expert Pentesting
You don't need another vendor that runs a scanner, dumps generic findings, and disappears for two weeks. You need a channel partner that understands where public key and private key encryption fails and can validate those controls through manual pentesting.
That matters because real gaps keep showing up in the field. 28% of web application pentests uncover man-in-the-middle vulnerabilities in the PKI chain, often tied to unverified certificates, which is exactly the kind of weakness automated testing misses (Rippling on public key vs private key).
If you're advising on SOC 2, HIPAA, PCI DSS, or ISO 27001, encryption can't stay theoretical. It has to be tested, explained clearly, and tied to business risk. Strong operational discipline also helps. This overview of secrets management best practices is worth sharing with clients that need better handling of keys and secrets across teams and systems.
We make that easy. Our team delivers affordable, fast, white label pentesting with certified pentesters holding OSCP, CEH, and CREST credentials. We stay channel-only, so we never compete with your MSP, vCISO, GRC, or reseller business.
Need a trusted partner for fast, affordable, manual pentesting that won't compete with your client relationships? MSP Pentesting delivers white-labeled pentests, penetration testing, and red team support for MSPs, vCISOs, and compliance partners. Contact us today to get a quote and expand your security offering with confidence.


.avif)
.png)
.png)
.png)

